Contents:
According to data gathered from over 200,000 network-connected medical infusion pumps used to deliver medication and fluids to patients, 75% of them have known security flaws that threat actors could abuse.
The discovery shows that tens of thousands of devices are exposed to six critical-severity flaws (9.8 out of 10) made public in 2019 and 2020.
More On the Critical Vulnerabilities
Researchers at American multinational cybersecurity company Palo Alto Networks examined the security state of over 200,000 medical infusion pumps using data collected from customers and discovered that “between 30,000 and at least 100,000 of them are vulnerable to critical security issues.”
According to BleepingComputer, the most widespread critical-severity vulnerability is tracked as CVE-2019-12255, a memory corruption bug in the VxWorks real-time operating system (RTOS) used for embedded devices such as infusion pump systems.
Based on data from the California-based cybersecurity firm, the weakness exists in 52% of the examined infusion pumps, totaling more than 104,000 devices.
CVE-2019-12255 is one of 11 vulnerabilities known as ‘URGENT/11’ that researchers at Armis, an organization providing security for connected devices, found and noted in 2019.
Wind River, the company that maintains VxWorks RTOS, has patched all URGENT/11 flaws since July 19, 2019. Nevertheless, in the embedded device world, significant delays in applying updates or not installing them at all are common issues.
The remaining five critical-severity vulnerabilities were discovered in June 2020 and impact products made by the American healthcare company Baxter International.
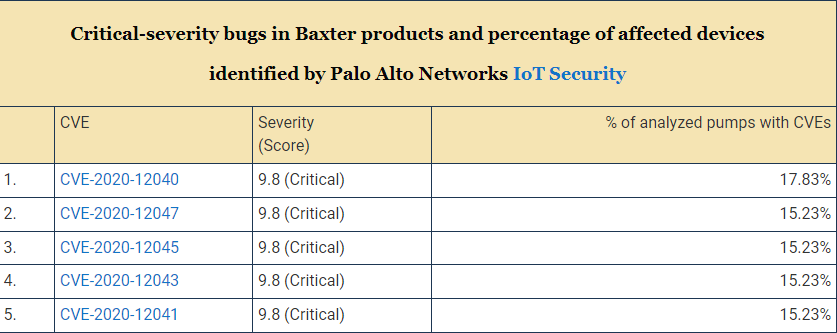
Most of the flaws can be exploited if the attacker is already on the network, according to Baxter’s security bulletin at the time.
They vary from cleartext data transmission without authentication to hardcoded credentials and incorrect authorizations that grant access to private information or allow the Wireless Battery Module’s network configuration to be changed.
Although there are no fixes available for these vulnerabilities, Baxter has provided a set of mitigations in order to minimize the chances of them being abused. It also recommended upgrading to the newer Spectrum IQ Infusion system, which is not impacted by the above bugs.
According to a CISA advisory, a low-skilled cybercriminal could take advantage of them.
What Is There to Do?
It is recommended that healthcare organizations implement a proactive security strategy to protect devices from known and unknown dangers and that this strategy begins with an accurate inventory of all systems on the network.
Not all of the security flaws impacting the analyzed medical infusion pumps are practical for cyberattacks, according to the researchers, but they do pose a “risk to the general security of healthcare organizations and patient safety.”
If you liked this article, follow us on LinkedIn, Twitter, Facebook, Youtube, and Instagram for more cybersecurity news and topics.


 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management
 Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security










