Contents:
A rapidly expanding malware is entrapping routers, DVRs, and servers all over the web in order to launch Distributed Denial-of-Service (DDoS) attacks on over 100 victims every day.
CNCERT and Qihoo 360’s Network Security Research Lab (360 Netlab) worked together and found this botnet they dubbed Fodcha.
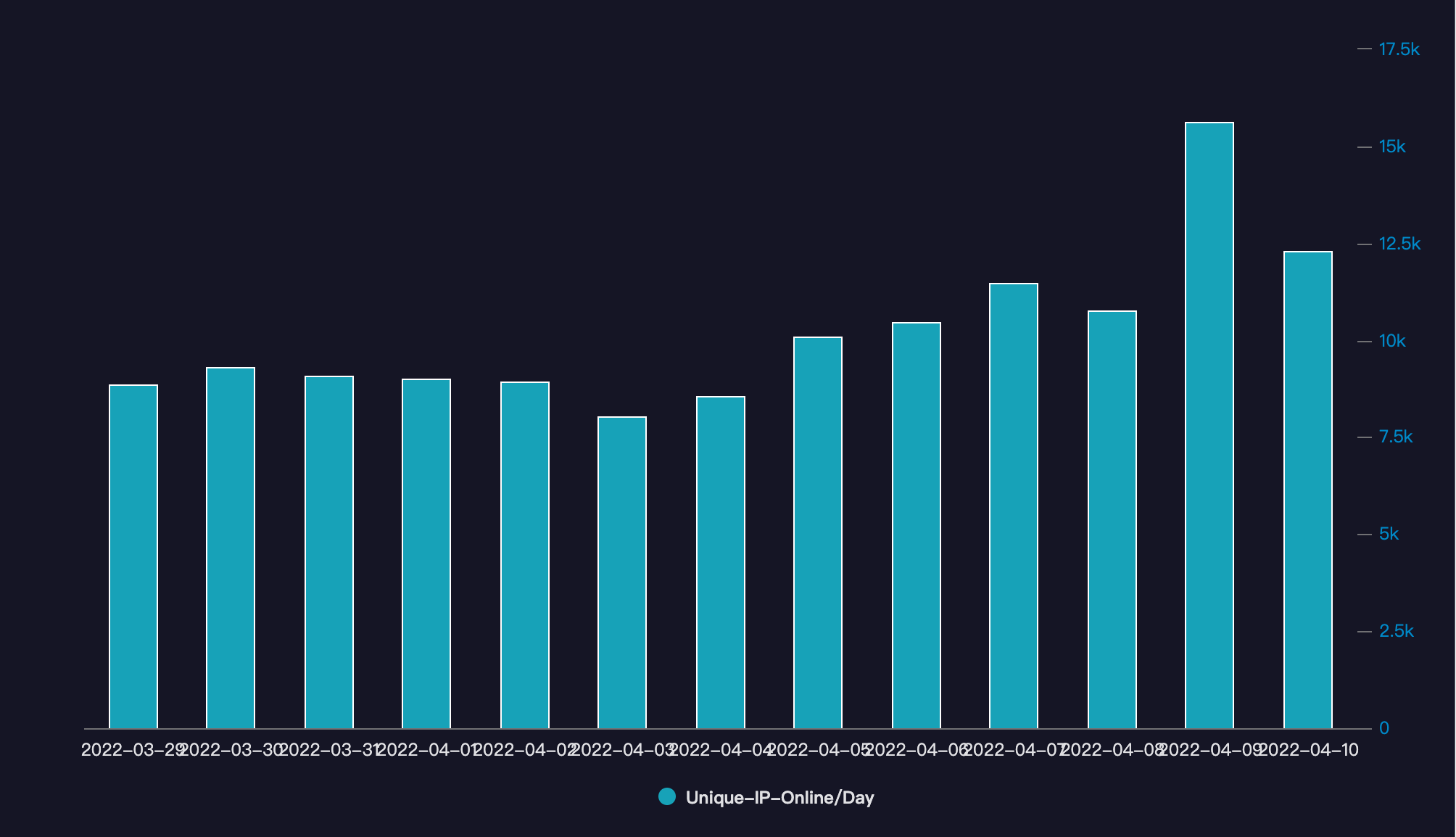
According to a report by 360 Netlab, between March 29 and April 10, Fodcha malware has infected 62,000 devices, and daily numbers fluctuate around 10,000.
As per 360 Netlab security researchers, the top regions from which the bots come from are Shandong (12.9 %), Liaoning (11.8 %), and Zhejiang (9.9%). China Unicom (59.9%), China Telecom (39.4%), and China Mobile (0.5%) are the service providers from which these bots originate.
Based on direct data from the security community that we worked with, the number of daily live bots are more than 56000.
The global infection looks fairly big as just in China there are more than 10,000 daily active bots (IPs) and also more than 100 DDoS victims being targeted on a daily basis.
Fodcha Spread Method
The specialists discovered that the Fodcha botnet compromises new devices with exploits created to abuse NDay vulnerabilities in multiple machines, as well as a brute-force cracking tool they named Crazyfia.
Below you can see a list of the main vulnerabilities provided by 360 Netlab and the devices and services targeted by the Fodcha malware:
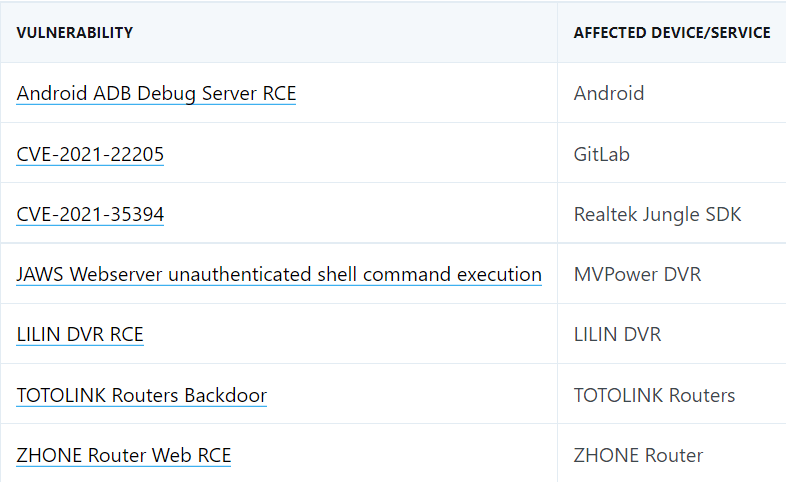
After they managed to obtain access to vulnerable Internet-exposed devices samples, the developers of the Fodcha botnet use Crazyfia scan evaluation to distribute malware payloads.
An analysis shows that the botnet includes samples targeting mips, mpsl, arm, x86, and other CPU architectures.
The botnet used the folded[.]in command-and-control (C2) domain from January 2022 until March 19, when it changed to fridgexperts[.]cc after the cloud vendor removed the original one.
The shift from v1 to v2 is due to the fact that the C2 servers corresponding to the v1 version were shutdown by a their cloud vendor, so Fodcha’s operators had no choice but to re-launch v2 and update C2.”
The new C2 is mapped to more than a dozen IPs and is distributed across multiple countries including the US, Korea, Japan, and India, it involves more cloud providers such as Amazon, DediPath, DigitalOcean, Linode, and many others.
Did you enjoy this article? Follow us on LinkedIn, Twitter, Facebook, Youtube, or Instagram to keep up to date with everything we post!










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security