Contents:
Nerbian RAT, a novel malware variant that comes with a long list of capabilities, including the ability to avoid detection and analysis by security researchers, has been recently spotted.
The new remote access trojan is written in the Go programming language, compiled for 64-bit systems, and it’s currently being distributed through a small-scale email distribution operation that uses macro-laced document attachments.
Yesterday, a report on the new Nerbian RAT malware was published by researchers at cybersecurity firm Proofpoint, who were the ones to observe the email campaigns.
Nerbian RAT M.O.
The emails sent to the victims are allegedly coming from the World Health Organization (WHO) with important information concerning COVID-19.
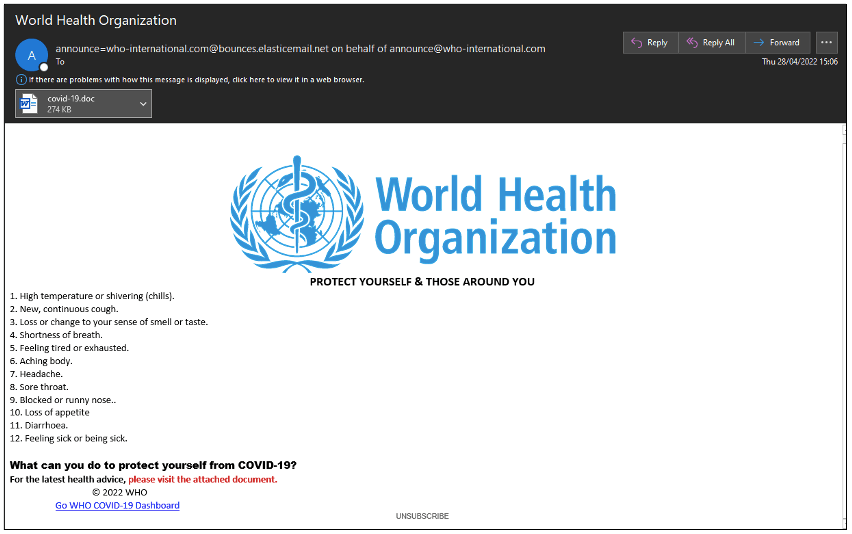
As explained by BleepingComputer, because the RAR attachments contain Word documents laced with malicious macro code, when opened in Microsoft Office with content set to “enabled,” a bat file carries out a PowerShell execution step to download a 64-bit dropper.
The dropper for Nerbian RAT, dubbed “UpdateUAV.exe,” is written in Golang as well, 3.5MB in size and UPX packed.
Executable files created in the Go language tend to be slightly larger than most other executable files. Likely, this malware is packed with UPX to reduce the overall size of the executable being downloaded. Unpacked, the file is 6.6MB in total.
Before the Serbian RAT malware deployment, the dropper reuses code from multiple GitHub projects to integrate a rich set of anti-analysis and detection-evasion mechanisms.
In addition, UpdateUAV will try to create a scheduled task named MicrosoftMouseCoreWork to launch the RAT payload hourly in order to establish persistence.
The following is a list of anti-analysis tools from Proofpoint:
- Examine the process list for the presence of reverse engineering or debugging programs
- Look for any dubious MAC addresses
- Analyze the WMI strings to confirm whether the disk names are valid
- Check to see if the hard disk size is less than 100GB, which is common for virtual machines
- Check the process list for any memory analysis or tampering detection programs
- Check the time since execution and compare it to a predefined threshold
- Use the IsDebuggerPresent API to find out if the executable is being debugged
Because of all these verifications, it is nearly impossible to get the RAT running in a sandboxed, virtualized environment, ensuring long-term stealthiness for the trojan developers.
A Deeper Look into the Nerbian RAT Malware
The malware is downloaded as “MoUsoCore.exe” and is saved to “C:ProgramDataUSOShared.” It supports multiple features, and its creators can configure it with some of them.
Keylogging and Screen Capture Features
The RAT seems to be capable of logging keystrokes and writing them, encrypted, to the rev.sav file. It also performs screen captures on a variety of different operating systems.
This RAT, like most modern malware families, prefers to handle communications with the C2 server over SSL (Secure Sockets Layer). This way, all data exchanges are encrypted and shielded from in-transit network scanning tools.
The Future of Nerbian RAT
Researchers have definitely discovered an intriguing, complex novel malware that focuses on stealthiness via multiple verifications, encrypted communications, and code obfuscation.
It might not be considered dangerous now as the RAT is spread via limited email campaigns, but the situation could be different if its developers decide to open up their business to the wider community of cybercriminals.
If you liked this article, follow us on LinkedIn, Twitter, Facebook, Youtube, and Instagram for more cybersecurity news and topics.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security