Contents:
Hacks, leaks, and phishing scams happen so often that they hardly register as news anymore. Just last week, Google warned of a phishing scam perpetrated by Fancy Bear, a hacking group associated with the GRU, Russia’s military intelligence organization. LinkedIn was used to perpetrate a OneDrive phishing scam, and Zoom has been shown to be vulnerable to packet injections.
With more people working from home due to the coronavirus epidemic, more e-commerce, and mobile social media users accounting for the greatest online growth in 2021, it’s more important than ever to know where your users are coming from and protect your organization from cybercrime.
Integrating IP geolocation into your threat intelligence toolbelt can protect your users from fraud and your systems from cyberattacks. IP addresses are physical addresses, identifying _where_ a connection takes place – for example, the router provided by your Internet Service Provider in your house.
IP geolocation APIs determine the geographic location of IP addresses and this can then be used to:
- Identify a request’s country of origin, and block IPs coming from countries with high fraud activity
- Identify proxies and web scrapers
- Display the currency of the user’s location
- Offer content based on the user’s location (or block content)
- Identify fraudulent activity
A geolocation API returns information such as:
- City, country, and regional location
- Long / lat coordinates
- Timezone details
- Currency (`USD` for US Dollar, as an example)
- Internet service provider name
- Security data including VPN, TOR, proxy, and crawler detection
So, with a simple API call, we can identify where a connection is taking place. This is powerful information to have! You’re probably already thinking of ways you can use this to protect your users. Read on to see how we can leverage this data in threat intelligence and cybersecurity.
Traffic filtering
If your company only does business within the USA, it would be suspicious to have an IP from Kazakhstan pinging your servers, wouldn’t it? Well, maybe.
Most geolocation APIs offer up-to-date databases of malicious IP addresses reported to be involved in fraudulent activity and allow you to filter them out. Of course, cybercriminals are always changing their domain names with proxies and VPNs, which are third parties that allow users to route their IP addresses through their servers for anonymity. Make sure you check how often the geolocation database is updated. An IP that was once a hotspot for fraud can be a ghost town the next day.
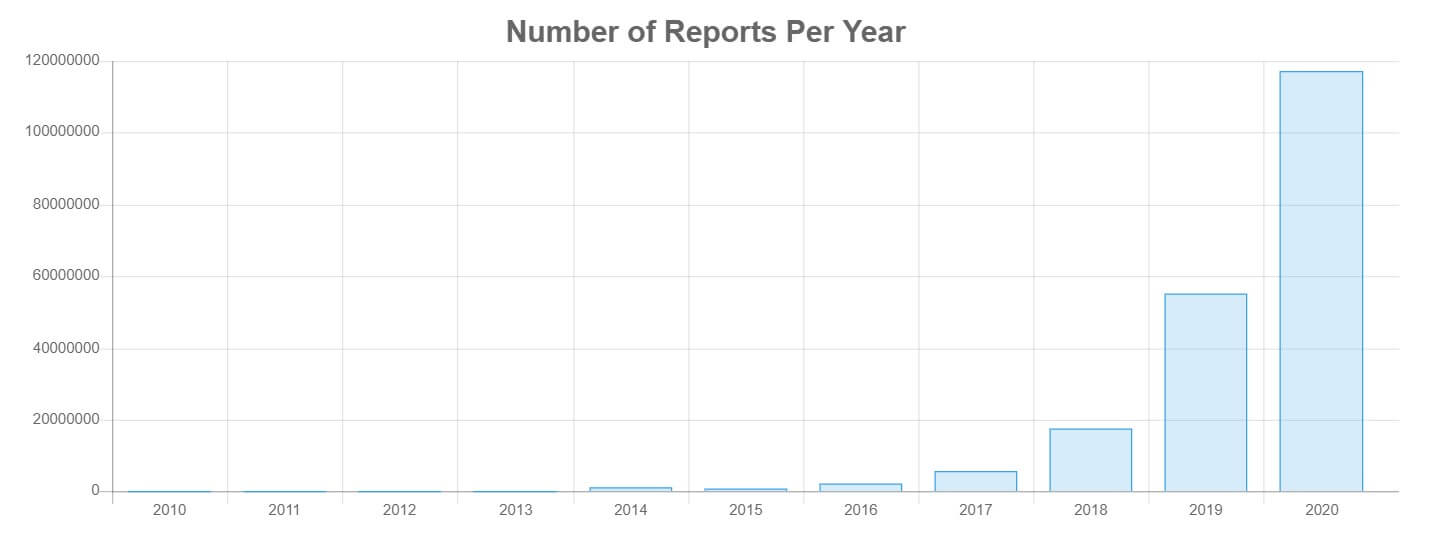
Image Source: AbuseIPDB
Your site could also be scraped by a proxy pool. Professional webscrapers automate their scraping across multiple proxies to dodge traffic filtering. Once an IP is listed on suspicious IP address databases, it might already be abandoned. Either way, web scraping sucks valuable resources from your system, because not everyone follows the ethical rules of web scraping. Similar to IP geolocation databases, proxy databases should be updated frequently.
There are a few ways geolocation can help us in traffic filtering:
- We might block IPs coming from countries with high fraud activity. We won’t call any countries out here, but you can find lots of articles on the subject with your favorite search engine.
- We might block requests geographically outside of our usual customer base. Using the example above, if our IT department is showing all of our requests usually coming from within our home country, we might find requests from outside that region suspicious.
- We might block traffic from datacenters using crawlers but allow residential proxies. Remember, proxies are not illegal, but are often a tool for anonymity.
DDoS Attacks
A Distributed Denial of Service or DDOS attack is an attempt to overwhelm a company’s hosting server to prevent them from providing service to website visitors. Cybercriminals do this with a flood of bots (a “botnet”) automated by a programmer. The botnet will send a flood of GET or POST requests to a server’s endpoints and overwhelm its resources. Sometimes, the DDoS is a feint to gain access without being noticed or to plant malware in the server.
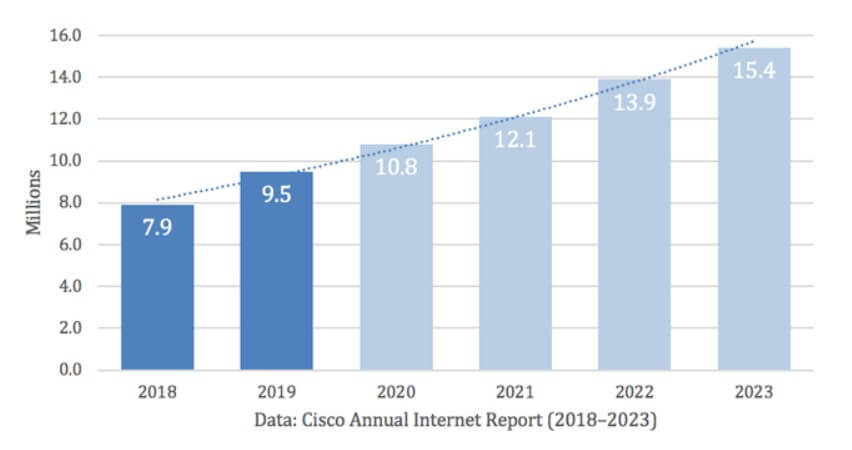
Image Source: A10 Networks
There are three main areas that are attacked:
- Network layer (Layer 3) attacks send massive amounts of traffic to overwhelm a network’s bandwidth.
- Transport layer (Layer 4) attacks exploit vulnerabilities in a server’s resources.
- Application layer (Layer 7) exploits weaknesses on particular web applications, including Internet of Things devices.
IP geolocation APIs can identify _where_ bad traffic is coming from during an ongoing DDoS attack. Closing your network to the identified IP address geodata locations can act as a temporary shield while your IT team does damage control. Afterward, you can permanently block those IP addresses. Ideally, you have your server backed up on a CDN (Content Delivery Network), and can continue serving customers while IT blackholes the DDOS traffic.
Of course, you can catch these issues early by having a clear idea of where most of your traffic comes from, knowing what your servers can handle, and being prepared for usage spikes.
Credit card fraud
You know when you pump gas, you’re asking for your credit card’s ZIP code? This is an anti-fraud measure to ensure someone isn’t running amok with your stolen credit card.
IP geolocation can be used similarly: when an online purchase is made, IP geolocation can tell the physical location that IP is connected from. If your card is registered in one country, and the purchase is made on the other side of the world, your financial provider will notify the merchant and the cardholder of the suspicious purchase and possible identity theft based on IP geolocation data.
It’s possible the purchase was just made over a VPN, or the buyer was traveling abroad, but IP location data information is used to make the check.
This method can also be used to check phishing scams. If you receive a message that looks like it comes from SalesForce, but the IP is listed as belonging to a different company, from a country known for dark web fraud, it’s possible it’s a phishing attempt and should be reported to your security team, who may blacklist the IP in their security system.
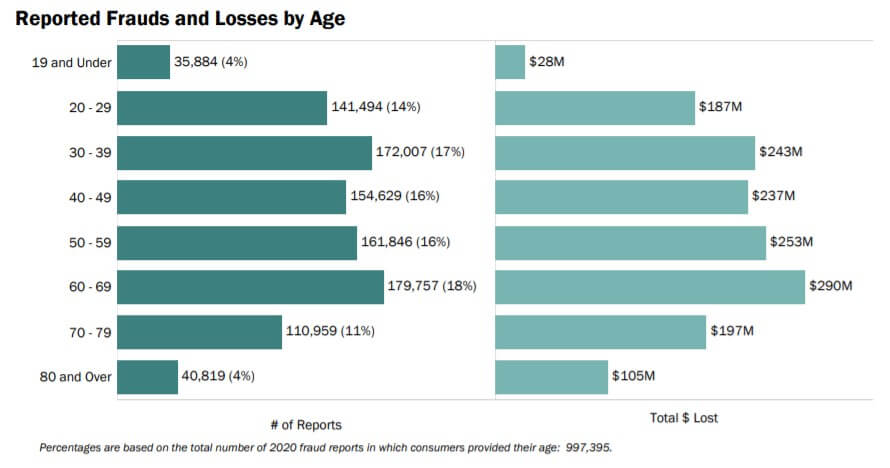
Image Source: Federal Trade Commission
IP geolocation: A horror story
IP address geolocation is usually correct, but once in a while, it’s very, very wrong. Due to a mistake by the National Geospatial Intelligence Agency, millions of IP addresses were mapped to some Pretoria, South Africa residents’ front yard. After being accused of everything from theft to running a cult, and finally being unjustly sued for cyberbullying (remember, their location was millions of other people’s IP address data), they asked for legal and technical help.
Of course, to correctly find a criminal, an officer of the law would have to go to the Internet Service Provider (ISP) with a warrant to find out who was actually using the IP at the time of the infraction. In this use case, the family was absolved of all wrongdoing, and in a month, the location was moved to the geographic center of Pretoria and safely away from their front yard.
Conclusion
IP geolocation is a powerful tool in your threat intelligence and cybersecurity arsenal and should be integrated into your larger security plan. The IP information can be used by a SaaS like SalesForce, or security suites like CloudStrike, to locate your users, identify potential fraud, and protect your resources. In a world that’s more connected than ever, and where cyberattacks occur every 39 seconds, it’s a good time to check your security.
And hey, even the US Department of Justice is feeling the heat, and they definitely know a thing or two about cybersecurity. The DOJ is now threatening to sue federal contractors who fail to follow prescribed cybersecurity standards or don’t report cybersecurity breaches. If the cybersecurity professionals at the DOJ are worried, you definitely want to know where your user’s requests are coming from with geolocation services.
About the Author:

Emma Jagger is a Google alumna, CMU grad, and a full stack engineer and maker at Abstract API.

- Granular telemetry across endpoints and networks.
- Equipped with built-in hunting and action capabilities.
- Pre-computed risk scores, indicators & detailed attack analysis.
- A single pane of glass for intelligence, hunting, and response.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security







