Contents:
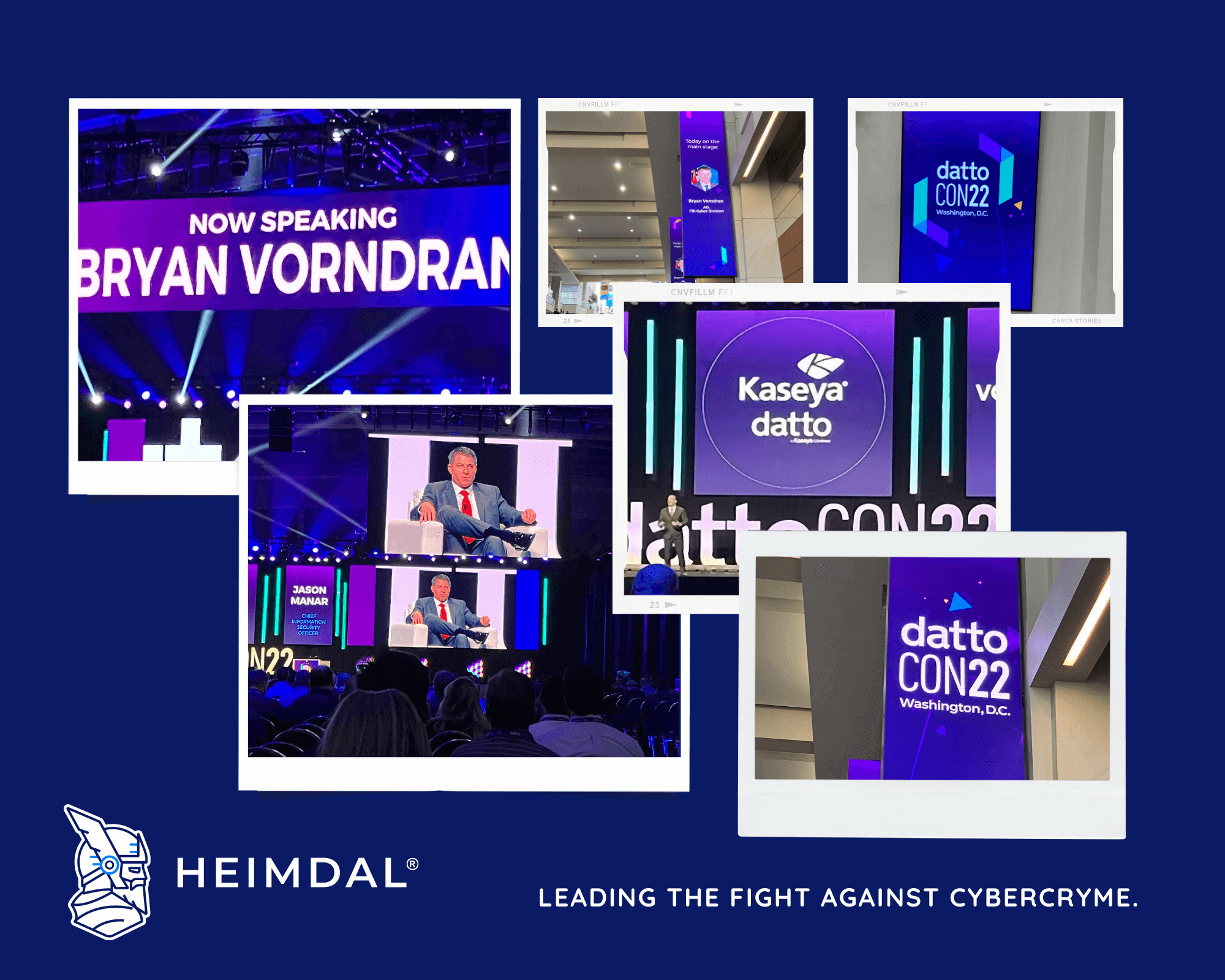
Over 2,700 participants from 29 countries gathered for an event that was jam-packed with news about technological advances (with a particular focus on the security space) that are currently working to help MSPs and businesses defend themselves against cybercrime in a world that is becoming more unsafe. DattoCon22 took place September 11-13 at the Walter E. Washington Convention Center in Washington, D.C.
Heimdal® US, Canada & LATAM Partner Manager Tom Elias attended the event and met our customers, partners, and colleagues, alongside MSPs from all over the world, technology experts, and some of the most forward-thinking minds in the business.

As the most recent technological insights were provided by top security experts, new security advances have set the pace. Both techs and executives have learned practical business methods that they can use right away.
In the security keynote, Kaseya CISO Jason Manar held a fireside chat with Bryan Vorndran, Assistant Director, FBI Cyber Division.
Heimdal’s correlation with the FBI goes back a long way. Vorndran recalled that back in 2014 the Bureau announced that Cryptolocker ransomware functioned by locking users out of their computers, encrypting their files, and then demanding money to restore them. Their disclosure coincided with authorities reporting that they had shut down a related cybercrime operation based on the Gameover Zeus (GOZ) software, which enabled its authors to steal more than $100 million by obtaining victims’ online banking login credentials.
Our company was seeing as many as 8,000 new Cryptolocker infections every day but had dropped to almost zero following the global law enforcement effort. Based on preliminary data, Heimdal reported that the operation against Cryptolocker was successful. The FBI has applauded our company for its technical support in locating the infection.
Vorndran also commented on the July 2021 Kaseya security incident, praising Kaseya’s response and telling attendees:
“Kaseya leaned in and engaged authorities immediately; all tools, all hands on deck. The leadership took on the problem and fought against the cyber attackers without giving them an inch or fear of the press. Timely reporting greatly assisted in identifying and apprehending the attackers. Without the quick cooperation of Kaseya that wouldn’t have been possible.”
Both Manar and Vorndran provided great insights on the threat landscape from the FBI’s perspective, the importance of incident response, the necessity of open information exchange, and the benefits of proactive threat monitoring in the fight against cybercrime. They continued by disclosing the three crucial actions that organizations may take to lower their risk:
- Regular patch management;
- Creating and protecting strong, secure passwords in a zero-trust environment;
- Educating staff on how to identify and resist phishing.
Determining how clearly they can see downstream to their resellers is crucial for MSPs and other channel participants, Vorndran said. They should also establish ties with the American government now so that they have one when an attack occurs.
He also added that it’s crucial to notify the FBI of an attack as soon as possible. The Bureau can thus assist in identifying the perpetrators of the incident and support companies in crucial negotiations with attackers.
With engaging presentations, lively discussions, and entertainment for MSPs and other business professionals at every corner, DattoCon22 was a huge success. We look forward to taking part in the 2023 edition.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security