Contents:
Fake Pokemon NFT card game website is used by threat actors to spread malware. Visitors are tricked to download the NetSupport remote access tool or RAT, a malicious software that takes over victims’ devices.
Details About the Campaign
Analysts at ASEC explained how the spam website “pokemon-go[.]io” pretends to offer a new Pokemon NFT card game, but it is, in fact, distributing malware. The cybercriminals choose a highly popular theme for the malicious site to attract as many individuals as possible through malspam, social media posts, etc.
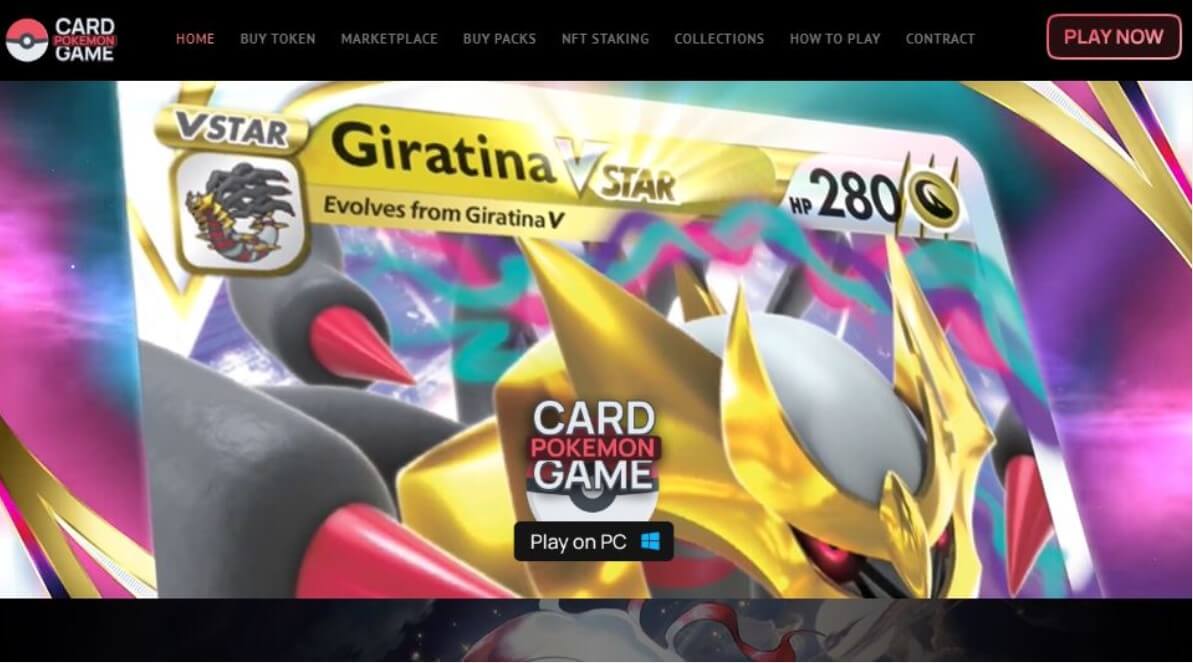
By clicking on the “Play on PC” button from this site, users download an executable that seems to be a legitimate game installer. But the malicious file is in fact installing the NetSupport remote access tool (RAT) on the victims’ devices.
This campaign’s first signs of activity appeared in December 2022, while earlier samples retrieved from VirusTotal showed that the same operators pushed a fake Visual Studio file instead of the Pokemon game.
The NetSupport RAT
The executable is called “client32.exe” and its ramifications are hidden in a new folder in the %APPDATA% path. This makes NetSupport RAT harder to detect at a manual inspection.
An entry is created in the Windows Startup folder so the RAT will execute upon system boot. After installation, hackers can remotely connect to a device, to exfiltrate data, deploy further malware or execute lateral movement in the network.
Threat actors use NetSupport RAT because the legitimate program, NetSupport Manager, can bypass security measures.
NetSupport Manager is a remote control tool that can be installed and used by ordinary or corporate users for the purpose of remotely controlling systems. However, it is being abused by many threat actors because it allows external control over specific systems.
Threat actors frequently employ NetSupport RAT as part of their harmful efforts. In 2022 COVID-19-related phishing scams dropped NetSupport RAT, and in August 2022 WordPress sites were targeted with fake Cloudflare DDoS protection that proved to be the same type of infection.
If you liked this article, follow us on LinkedIn, Twitter, Facebook, YouTube, and Instagram for more cybersecurity news and topics.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security