Contents:
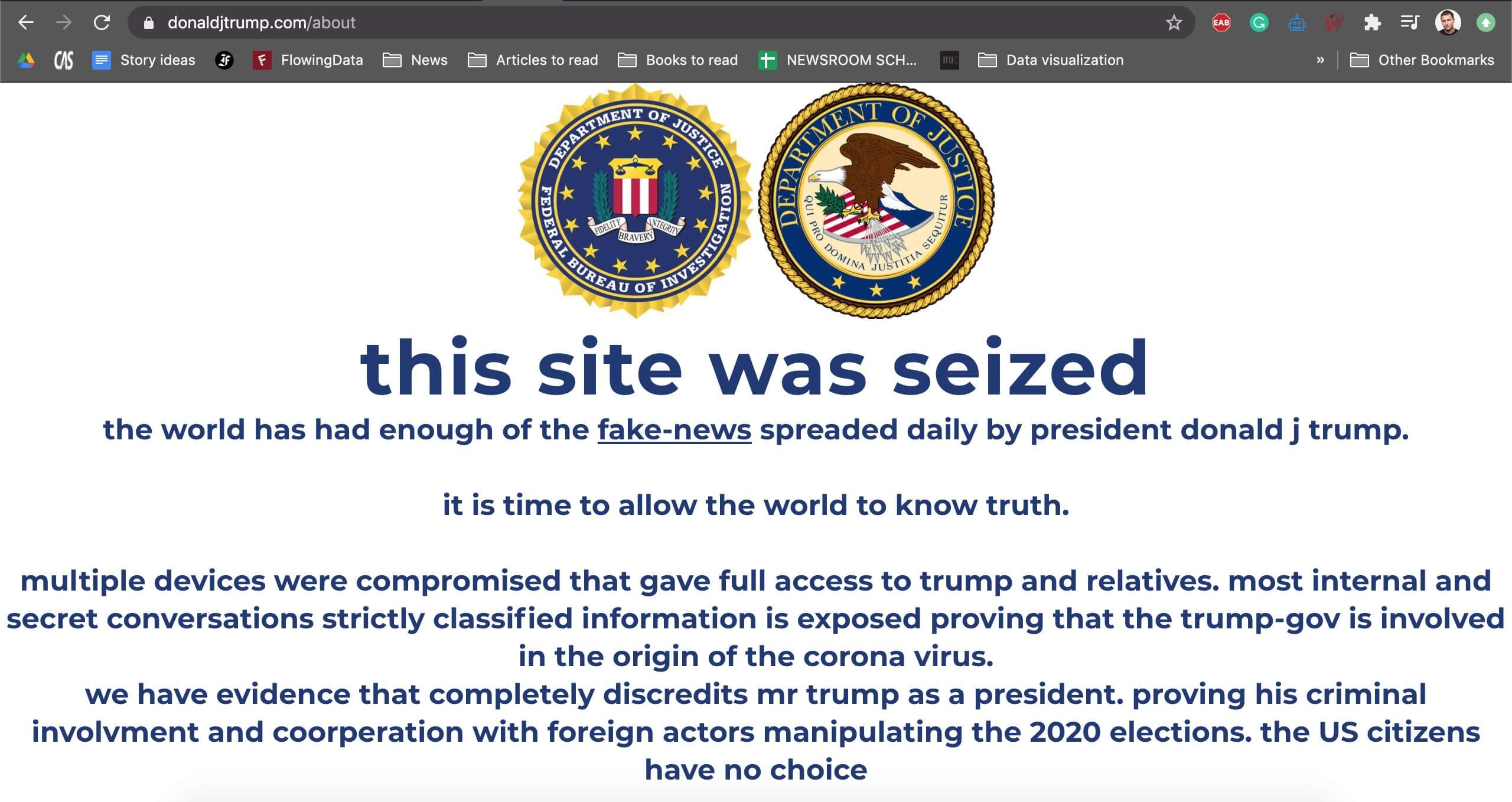
On Tuesday night, White House officials confirmed that Donald Trump’s campaigned site become temporarily unavailable due to hacking. The POTUS’s website was replaced by a fake FBI seizing notice, which blatantly accused the Trump administration and his relative of the distribution of fake news, withholding information about the coronavirus pandemic’s origin, and manipulating the outcome of the upcoming presidential elections.
The website was restored after a few minutes. Investigators declared for the press that no sensitive information was leaked during the attack. Steps have been taken to identify the culprit(s) behind this brazen attack. Scenarios such as foreign agencies at work have been dismissed, the experts believing this to be the work of a group of self-proclaimed vigilantes whose sole purpose would be to scam anti-Trump supporters by playing the ‘secret information card’.
Donald Trump’s family tied to foreign affairs and coronavirus pandemic
Cybersecurity experts are still examining the evidence obtained after the attack on Donald Trump’s campaign website. The initial findings suggest that the threat actors were able to infiltrate the campaign website’s web server through unknown means and insert a long-winded JavaScript code to simulate the seizing notice. The fake page contained the logos of the FBI and the United States’ Department of Justice. FBI officials have declined to comment on the incident.
The hacking attack was first brought to the public attention by independent journalist Gabriel Lorenzo Greschler. On his Twitter page, Greschler wrote that the scam page “popped up” while he “was doing research for a climate change article”. As to the contents of the inflammatory page, the group wrote that the “world has had enough of the fake-news spreaded (!sic) daily by president donald j trump (!sic)”.
The full version of the text is included in the image below.
Image courtesy of Gabriel Lorenzo Greschler
Among other allegations, Trump’s administration and his close relative are accused of partaking in the coronavirus pandemic and colluding with foreign agencies to manipulate the outcome of the 2020 elections. The threat actors behind this attack, which are believed to be hacktivists rather than black-hat hackers, mentioned that they are currently in possession of evidence capable of substantiating their claims.
To that end, they’ve been careful to enclose two cryptocurrency transfer accounts. One of them was labeled “want to know the truth” while the other was for “keeping the secret.” An undisclosed deadline was also included in the note.
In a nutshell, this “for the people, by the people decision” boils down to the hacktivist will decide whether to blow the whistle or keep the secret based on which coffer is fuller. Talking about the power of free will. The two cryptocurrency transfer addresses are impossible to track back to the recipient as they are tied to Monero, a crypto transaction platform notorious for its cult of anonymity.
The page itself was found to have been encrypted with a public PGP key, appended to a domain that doesn’t exist.
Tim Murtaugh, Trump’s campaign communications director confirmed the incident and added that there’s no evidence to suggest that the data hosted on the webserver has been accessed or compromised in any way.
Protecting against Ransomware and Cryptocurrency Scams
Heimdal™ Security classifies this recent event as “severe” and cautions institutions and companies on the dangers of unsecured coding loopholes. The hacktivists were able to penetrate Trump’s campaign website because it’s less secure compared to institutional websites such as whitehouse.gov, fbi.gov, and others. Cryptocurrency scams and ransomware are on the rise.

Heimdal® DNS Security Solution
- Machine learning powered scans for all incoming online traffic;
- Stops data breaches before sensitive info can be exposed to the outside;
- Advanced DNS, HTTP and HTTPS filtering for all your endpoints;
- Protection against data leakage, APTs, ransomware and exploits;
This is why it’s vital to improve your cybersecurity posture. DNS traffic filtering is the best (and only) defense against these types of occurrences. Heimdal™ Security’s Heimdal™ Threat Prevention is capable of detecting and terminating connections to malicious servers trying to connect with your web servers or endpoints to exfiltrate data. Heimdal™ Patch & Asset Management, Heimdal Threat Prevention’s automatic patching, and updating module will close any security gaps that might compromise your system.
Conclusion
Donald Trump has yet to comment on the recent hacking. However, last week, during the campaign rally in Arizona, the POTUS noted that hacking is next to impossible since the act itself requires a high IQ (197 to be precise) and some info about the victim’s password. Trump’s anecdotal discourse on the intricacies of hacking couldn’t have come at a better time. One can certainly remember the infamous maga2020 hiccup, orchestrated by Victor Gevers, a Dutch cybersecurity expert who managed to gain access to the president’s personal Twitter account after guessing his password (maga2020!). Hacktivism or higher interests at work? Remains to be seen.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security