Contents:
4 members belonging to APT40, a hacking group supported by the Chinese government, were indicted yesterday by the U.S. DOJ (Department of Justice). They were charged with several hacking crimes that unfolded between 2011 and 2018 where they targeted state entities, universities, and enterprises.
This above-mentioned indictment follows another accusation from yesterday, where the U.S., the European Union, the UK, and NATO have officially blamed China for being responsible for the malicious campaign targeting Microsoft Exchange that has been in progress in the course of this year, pointing out especially to another APT Group by its name Hafnium.
How Does APT40 Operate?
APT40 is the name of a Chinese cyber-espionage group that normally focuses on defense and engineering organizations. Their target list also included Belt and Road Initiative regional adversaries, contractors from the U.S. and Europe belonging to naval defense sectors and maritime industries, and various electoral bodies in Cambodia. Aviation, government, education, biopharmaceutical, and healthcare industries were of equal interest for the hacking group.
Their modus operandi follows some tactics, as DOJ points out:
- Deploying malware such as PHOTO, BADFLICK, HOMEFRY, or MURKYTOP.
- Spearphishing emails containing fake profiles and links that led to doppelgänger domains. Goal? Simulation of real domains of the companies.
- Targeting credentials to hijack them that also helped them to conduct spearphishing campaigns.
- They also used TOR (The Onion Router) to access malware on the victims’ network and GitHub to hide and store stolen information and malware through steganography.
Who are the 4 Indicted members of APT40?
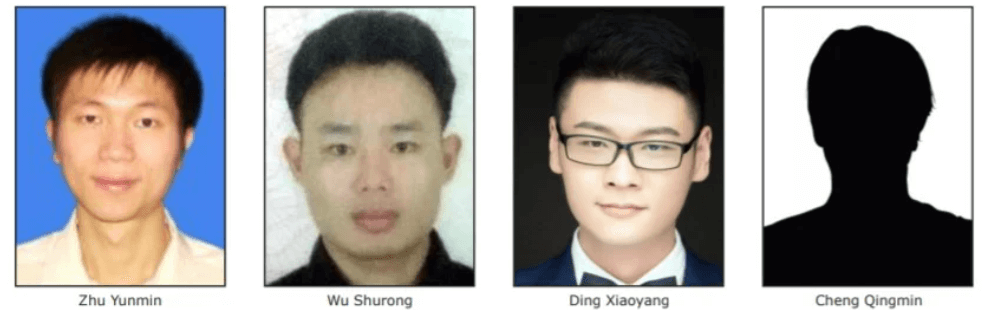
As Bleeping Computer reports, the Chinese-members the U.S. Department of Justice charged with cybercrimes are Ding Xiaoyang (丁晓阳), Cheng Qingmin (程庆民), Zhu Yunmin (朱允敏) and Wu Shurong (吴淑荣).
The first three ones, Hainan State Security Department (HSSD) intelligence officers, laid the foundations of Hainan Xiandun Technology Development Co., Ltd. (海南仙盾) (Hainan Xiandun), an enterprise meant to work as camouflage to let them conduct their crimes undisturbed.
Then the above-mentioned company hired Wu Shurong (吴淑荣). His task was to develop malware in order to target foreign systems, enterprises, or universities. Goal? Theft of intellectual property, trade secrets, and other valuable data.
The U.S. Department of Justice also declared in a statement:
The conspiracy’s hacking campaign targeted victims in the United States, Austria, Cambodia, Canada, Germany, Indonesia, Malaysia, Norway, Saudi Arabia, South Africa, Switzerland, and the United Kingdom. (…) Stolen trade secrets and confidential business information included, among other things, sensitive technologies used for submersibles and autonomous vehicles, specialty chemical formulas, commercial aircraft servicing, proprietary genetic-sequencing technology and data, and foreign information to support China’s efforts to secure contracts for state-owned enterprises within the targeted country (e.g., large-scale high-speed railway development projects). At research institutes and universities, the conspiracy targeted infectious-disease research related to Ebola, MERS, HIV/AIDS, Marburg, and tularemia.
The APT40 members face charges of economic espionage and computer fraud and they could stay in prison up to 15 years.
How Can Organizations Mitigate APT40 effects?
To mitigate the effects produced by APT40’s actions, NSA, the FBI, and CISA took some measures.
Thus, Indicators of Compromise and TTPs, intended to help organizations identify and mitigate damage, were released by CISA and FBI, and together with NSA they also published a joint advisory stating more than 50 techniques APT40 used to perform their crimes.
General mitigations outlined include: prompt patching; enhanced monitoring of network traffic, email, and endpoint systems; and the use of protection capabilities, such as an antivirus and strong authentication, to stop malicious activity.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security