Contents:
In the wake of frequent cyber-attacks affecting businesses, cyber insurance has become a highly researched and debated topic. This industry has been constantly growing for a couple of decades now. As per Zion Market Data research, the global cyber insurance market is expected to reach $22.8 billion globally by 2024, with a compound annual growth rate of 24%.
In spite of the high availability of cybersecurity protection and prevention tools, there still might be a chance for a company to become a data breach victim. However, this doesn’t mean measures such as employee training and cybersecurity solutions should be left behind. By all means, you should not be relying solely on reactive practices, like buying insurance policies. It’s always better to prevent a cyber disaster than deal with the consequences.
But what does cyber insurance cover? Is it worth investing in cyber insurance? These questions may have crossed your mind, so, in this article, I’m going to try to give answers to some burning questions and help you decide if or which cyber insurance providers may be right for your organization.
What is Cyber Insurance?
First things first, let’s start off with a definition of cyber insurance.
Cyber insurance is a type of insurance for businesses against digital threats. It is also commonly known as cyber risk or cyber liability insurance.
With so many cyber dangers threatening companies, no wonder it has become a highly popular service for organizations large and small around the world. But if you do decide to invest in cyber insurance, are you fully aware of what it’s all about?
Keep on reading to find out.
Why do companies generally purchase cyber insurance policies?
And how many organizations out there are actually covered by cyber insurance? According to Spiceworks data, 38% of organizations are covered by a cyber-insurance plan, with nearly half having had a policy for under 2 years, 32% for 3-4 years, and 24% having been covered for 5+ years.
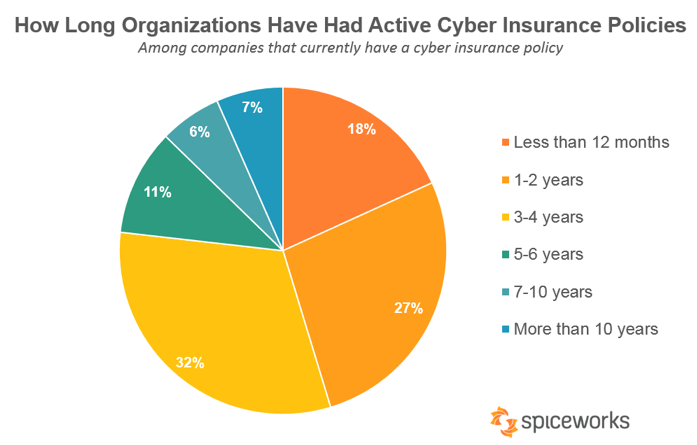
Source: Spiceworks study
What’s more, 71% of survey respondents stated that they purchased a policy for precautionary reasons. This seems to be the top driver for organizations to get coverage, followed by an increased priority on cybersecurity (44%), handling a high volume of personal data (39%), and industry-specific regulations (28%). On top of that, only 14% seem to have bought insurance coverage due to customer requirements and an additional 14% as a result of new data protection regulations, such as GDPR. Additionally, IT professionals admit to choosing cyber insurance coverage just to get some peace of mind and hope they never use it.
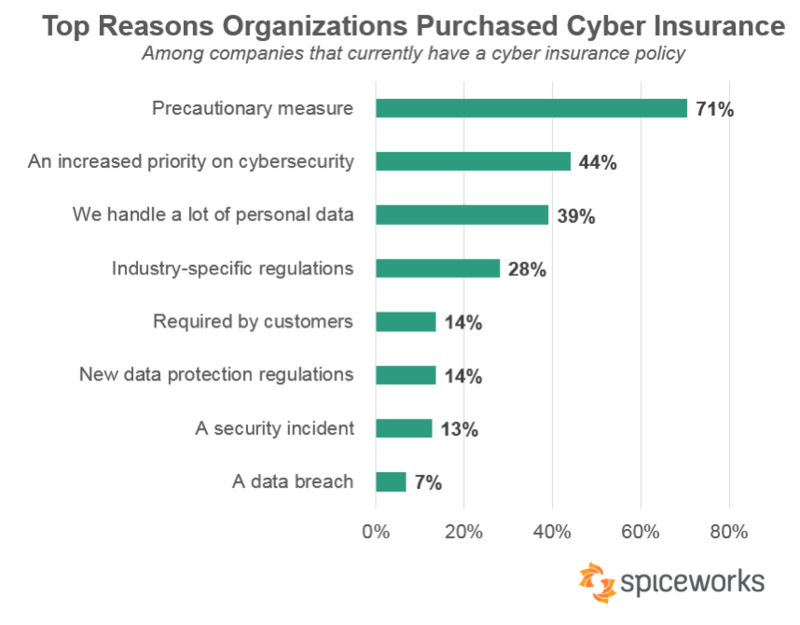
Source: Spiceworks study
What does cyber insurance cover?
Cyber risk is without a doubt one of the most difficult aspects to deal with as it has a high impact on both societies and businesses worldwide. Cyber insurance plans are typically created with digital risk in mind in order to ensure (in the best way they can) the continuity of a business and ultimately enable companies to become cyber resilient.
However, not all cyber insurance policies are created equal. Sometimes, decision-makers may be tempted to choose low-price services and end up with a bad deal. This typically happens because in some cases, cyber insurance providers trying to safeguard their existence in the face of harsh competition, tend to create packages that leave high-risk areas uncovered. Why does this happen, you may be wondering. Because some cyber insurance vendors are inexperienced in cybersecurity and don’t fully understand an organization’s actual needs in the current threatscape.
Before deciding to purchase a cyber-insurance policy, you will want to know what it covers to be able to better asses if a certain insurer is a good fit for your company. So, evaluate your options carefully.
A Cyber insurance coverage checklist
Here are the main items typically covered by cyber insurance policies:
- Restoration of damaged data and software destructed by forms of malware (such as viruses, spyware, worms, etc.)
- Extortion losses (ransomware)
- Setting up a temporary environment so your company can continue to operate
- Business interruptions that resulted directly from a cyber-attack (such as DDoS attacks)
- Temporary security experts hired to defend your company against the attack
- Legal expenses and fees
- Costs with notifying employees and the public
- Costs associated with the reputation damage
What does cyber insurance NOT cover?
Even though your cyber insurance may fix some of your post-cyberattack problems, keep in mind that it will not sort everything out. Below are some aspects that are (usually) not covered:
- Physical property loss and damage
Normally, cyber insurance coverage excludes physical loss that happened as a direct result of a cyber-attack. For instance, think about manufacturers and energy suppliers that may be more likely to become victims of cyberattacks meant to cause physical damage. If machines are destroyed due to malicious hackers overriding them, losses will not be covered by cyber insurance and instead, they would most likely fall under other types of business insurance, such as crime insurance.
- Social engineering attacks
Oftentimes, cyber insurance policies have social engineering reduction clauses. Some sources are mentioning a payout reduction if employees fall victim to social engineering attacks. For instance, according to a city government, “they had a $50-million-dollar cybersecurity insurance policy, but if a claim involved social engineering, then it only paid out a maximum of $200,000.” And unfortunately, customers who are not aware that 70% to 90% of all successful data breaches happen due to social engineering attacks, are potentially wasting up 90% of they were expecting to be covered.
What’s more, according to a report released by Mactavish, many insurance policies contain grey areas. Below you can see what they normally don’t cover.
- They do cover attacks or hacks but exclude accidents and errors
- They do cover costs imposed by law, but not total incident costs
- They only cover the time of the network interruption, but not the overall business disruption moving forward
- They may exclude systems delivered by third-party service providers
- They may not cover software or systems currently in development
- Policies may sometimes not cover incidents caused by contractors
- Customers may not be able to choose their own IT, PR or legal specialist since the insurance policy only covers appointed advisors.
Thus, the points above would typically need to be negotiated before signing the insurance contract. Therefore, you really need to bear in mind these common exceptions when you are evaluating cyber insurance vendors and be sure you choose the plan that best matches your business and cybersecurity needs. And better yet, never put large amounts of money and your trust in cyber insurance policies and invest in proactive cybersecurity measures instead.
Is cyber insurance really worth it after all?
It depends on several factors. Ultimately, it’s up for you to decide, according to your current business needs.
For instance, would it be better to spend $15,000 to buy a cyber insurance policy or to use that money to upgrade your current cybersecurity offering and train your employees to recognize and react at the first signs of cyber compromise? Or split the amount between these areas?
Oftentimes, cyber insurance may create a false sense of security, so be careful how much you actually invest in it and what items it includes. Also, keep in mind that after choosing a certain insurance policy, you should not just leave it there to gather dust indefinitely. In fact, your cyber insurance contract should be constantly reviewed and updated depending on your evolving needs and current cyber-threat dangers.
So, how much cyber insurance coverage do you really need?
On average, data breaches cost companies 150$ per record, according to the IBM and Ponemon Institute 2019 Cost of a Data Breach Report. Furthermore, the study also concluded that the average time to identify and contain a data breach was 279 days. If you do decide to purchase a cyber insurance policy, these figures can be some good starting points.
You should take into consideration aspects such as:
- How much sensitive information you store
- Where is the sensitive information stored
- What measures you would need to take if you experienced a data breach
- What would the costs be to replace the damaged software (and perhaps hardware)
- Do you have any employees trained to mitigate the damage, or do you need external security specialists?
- Is there any PR staff able to deal with crisis management if you experienced a data breach?
Trying to find answers to these questions and come up with answers to other questions formulated by yourself taking into account your own business model will help you get an idea of how much insurance coverage you would need in case of an emergency.
Should you replace cybersecurity with cyber insurance?
No, never! Cyber insurance should never be used, under any circumstances, as a cybersecurity replacement. Do not operate with the it-won’t-happen-to-me mentality and try to cut down costs associated with security tools. You may “save” some money for a while, but in the long run, this practice will only damage your business.

Heimdal® DNS Security Solution
- Machine learning powered scans for all incoming online traffic;
- Stops data breaches before sensitive info can be exposed to the outside;
- Advanced DNS, HTTP and HTTPS filtering for all your endpoints;
- Protection against data leakage, APTs, ransomware and exploits;
Cyber insurance and ransomware payouts, a controversy
Some cyber-insurance companies seem to encourage ransomware victims to pay the ransom. Apparently, this practice is seen as the cheapest way to reverse ransomware attacks and at the same time ensure the least downtime possible. And this happens despite warnings and discouragement from law enforcement agencies that are saying “ransoms shouldn’t be paid because they fund criminal activity.” What’s more, in the past, we saw ransomware strains that deleted data even if the victims paid, so the ransomware payment behavior certainly comes as a red flag. Sadly, the main goal of insurance companies here is to get the issues resolved at the lowest price possible.
What should companies do instead of paying the ransom? Use the proper cybersecurity tools, apply system and software updates as soon as they are released, and always back up their sensitive data.
Bottom Line

- Next-gen Antivirus & Firewall which stops known threats;
- DNS traffic filter which stops unknown threats;
- Automatic patches for your software and apps with no interruptions;
- Privileged Access Management and Application Control, all in one unified dashboard
Even though no organization will be completely safe from cyber-attacks and even if cyber insurance does offer you protection to some extent, it’s never advisable to rely solely on it. So, make sure that you invest in the right proactive cybersecurity tools, systems, and procedures alongside your employees’ cybersecurity training. And only then, if you choose to, create a cyber insurance plan tailored to your company and be certain it gets constantly revised and updated.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security








