Contents:
Conti’s source code was exposed after the company allied with Russia in the Ukraine conflict, and a security researcher obtained 170,000 internal chat messages as well as the source code for the company’s functioning from the company.
What Happened?
A hacker organization known as NB65 has been infiltrating Russian businesses, collecting their data, and then exposing it online, stating that the attacks are being carried out in retaliation for Russia’s military intervention in Ukraine.
The hacker gang claims to have targeted a number of Russian businesses, including document management company Tensor, the Russian space agency Roscosmos, and the state-owned Russian television and radio station VGTRK.
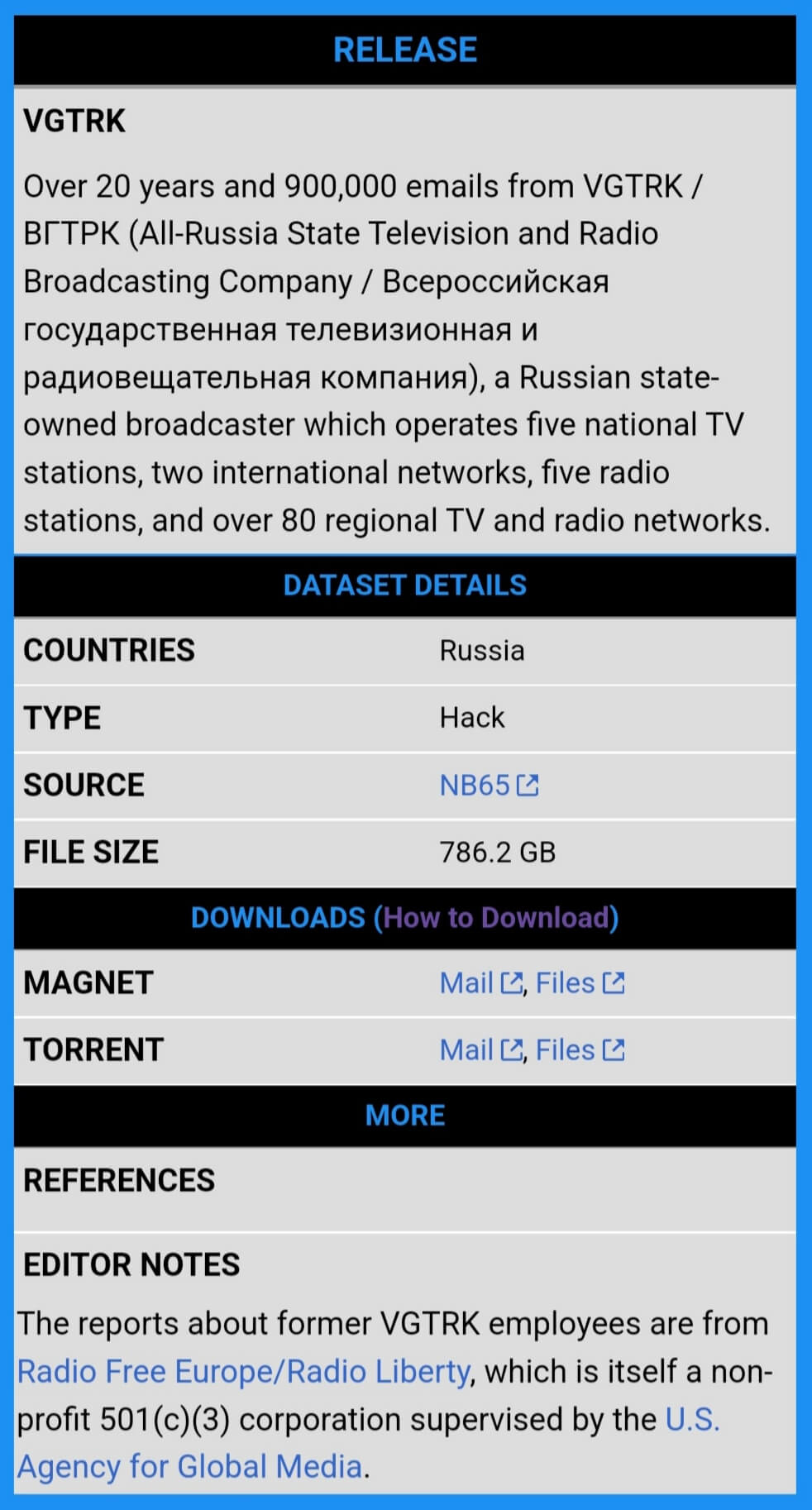
It is especially noteworthy that the assault on VGTRK resulted in the claimed theft of 786.2 GB of data, which included 900,000 emails and 4,000 files, which were then made public on the DDoS Secrets website after being published on the Dark Web.
More recently, the NB65 hackers have adopted a new strategy, launching ransomware assaults on Russian firms beginning at the end of March, according to the FBI.
More noteworthy is the fact that the hacker gang developed their ransomware using leaked source code from the Conti Ransomware operation, which is a Russian threat actor organization that forbids its members from targeting organizations located inside the country of the Russian Federation.
Moreover, according to BleepingComputer, the ransomware will also generate ransom notes, which will be titled R3ADM3.txt, and spread across the encrypted device, with the threat actors accusing President Vladimir Putin of invading Ukraine to carrying out the assault.
A representative of the NB65 hacking group told BleepingComputer that their encryptor is based on the Conti source code that was previously leaked, but they customized it for each victim so that any existing decryptors would not work.
After Bucha we elected to target certain companies, that may be civilian owned, but still would have an impact on Russias ability to operate normally. The Russian popular support for Putin’s war crimes is overwhelming. From the very beginning we made it clear. We’re supporting Ukraine. We will honor our word. When Russia ceases all hostilities in Ukraine and ends this ridiculous war NB65 will stop attacking Russian internet facing assets and companies.
Until then, fuck em.
We will not be hitting any targets outside of Russia. Groups like Conti and Sandworm, along with other Russian APTs have been hitting the west for years with ransomware, supply chain hits (Solarwinds or defense contractors)… We figured it was time for them to deal with that themselves.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security