Contents:
The BlackCat ransomware group launched a malvertising campaign to push Cobalt Strike. They put up advertisements to attract people to fake WinSCP pages. Instead of the application, the victims download malware.
WinSCP (Windows Secure Copy) is a well-known SFTP, FTP, S3, SCP, and file manager that supports SSH file transfers. It is free and open-source software, 400,000 people download it every week from SourceForge alone.
Threat actors target system administrators, web admins, and IT professionals through this campaign. Hackers can use their machines as an initial point of access to corporate networks.
Details About BlackCat’s Malwetising Campaign
This is a new infection vector for BlackCat ransomware, recently discovered by researchers at Trend Micro.
The fake websites are promoted on Google and Bing search pages. When victims search for “WinSCP Download” malicious results from the malvertising campaign will appear ranked above the safe WinSCP download sites.
Once victims click on the ads, they will land on a page with tutorials about performing automated file transfers with WinSCP. This is not a malicious site and will bypass detection. Nevertheless, users are redirected to a copy of the official WinSCP page including a download button. The clones will even have a similar domain name to the legitimate one, such as winsccp[.]com.
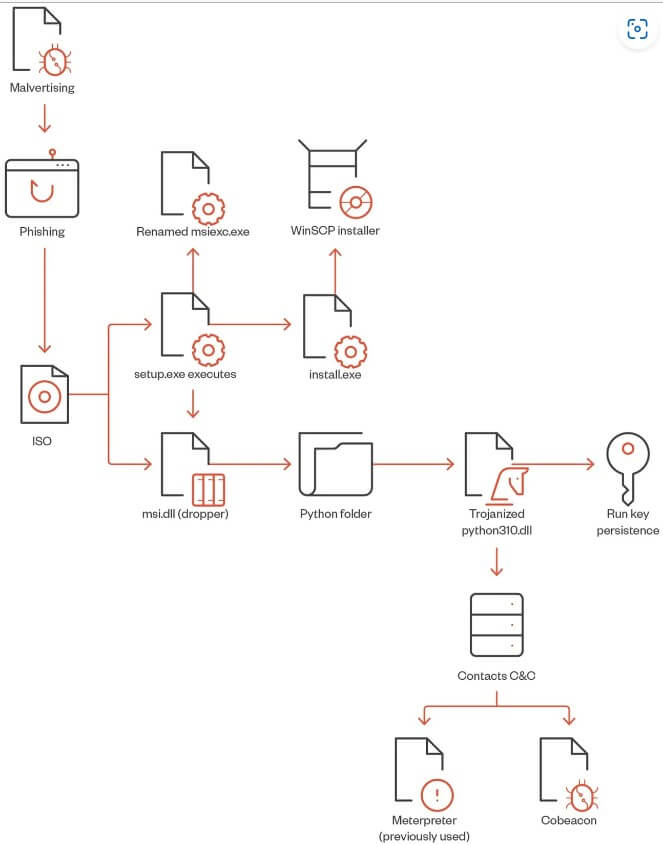
The download will include an ISO file containing “setup.exe” – the bait for the users – and “msi.dll” – the malware dropper.
Once setup.exe is executed, it will call the msi.dll that will later extract a Python folder from the DLL RCDATA section as a real installer for WinSCP to be installed on the machine. Two installations of Python3.10 will be created — a legitimate Python installation in %AppDataLocal%\Python-3.10.10 and another installation in %Public%\Music\python containing a trojanized python310.dll. Finally, the DLL will create a persistence mechanism to make a run key named “Python” and the value C:\Users\Public\Music\python\pythonw.exe.
The pythonw.exe loads a modified, obfuscated version of python310.dll with a Cobalt Strike beacon that establishes a connection to a command-and-control server address.
Additional Tools Employed by BlackCat
It is simple to launch more scripts, get tools for lateral movement, and generally deepen the compromise when Cobalt Strike is running on the system.
Threat actors employed the SpyBoy “Terminator,” an EDR and antivirus disabler, to elevate their privileges on the machine and deactivate multiple Windows security mechanisms by employing a “bring your own vulnerable driver” (BYOVD) technique. Threat actors advertise “Terminator” for up to $3,000 on the Dark Web.
BlackCat’s operators also used the following tools in the next stages of the infection:
- AdFind: Active Directory (AD) information can be retrieved using this command-line tool.
- PowerShell commands: for collecting user information, extracting ZIP archives, and running scripts.
- AccessChk64: a command-line tool used for user and groups permissions.
- Findstr: a command-line tool used for finding passwords within XML files.
- PowerView: PowerSploit script used in AD reconnaissance and enumeration.
- Python scripts: executing the LaZagne password recovery tool and getting Veeam credentials.
- PsExec, BitsAdmin, and Curl: perform lateral movement.
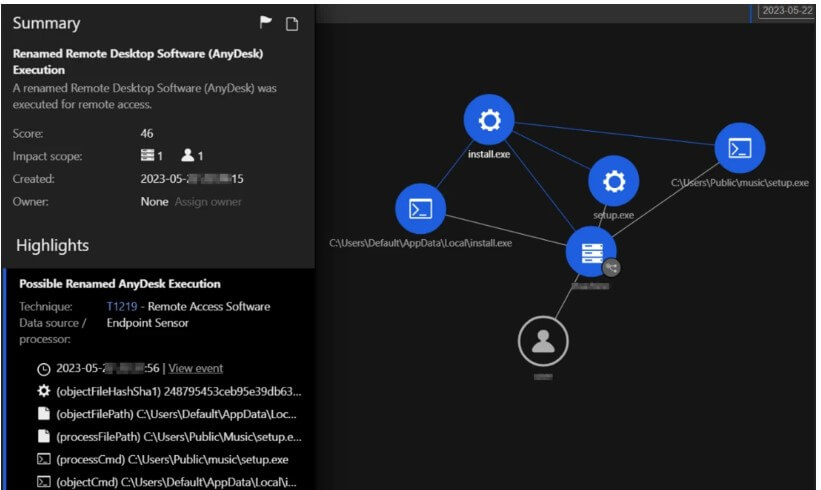
- AnyDesk: an abused legitimate remote management tool used to maintain persistence.
- KillAV BAT script: bypasses antivirus and antimalware software.
- PuTTY Secure Copy client: exfiltrating information.
If you liked this article, follow us on LinkedIn, Twitter, Facebook, and YouTube for more cybersecurity news and topics.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security