Contents:
A new phishing campaign was discovered as it tried to deliver the BazarBackdoor malware by using the multi-compression technique and masking it as an image file.
Even if the multi-compression, also called the nested archive method, is not new it recently became popular as it is able to trick email security gateways into mislabeling malicious attachments as clean.
This technique consists of placing an archive within another, and according to the researchers at Cofense this method is able to bypass some secure email gateways (SEGs) that might operate with a limit regarding how deep they do a check on a compressed file.
It looks like this new BazarBackdoor campaign was deployed earlier this month and managed to lure enterprise recipients with an “Environmental Day” theme.
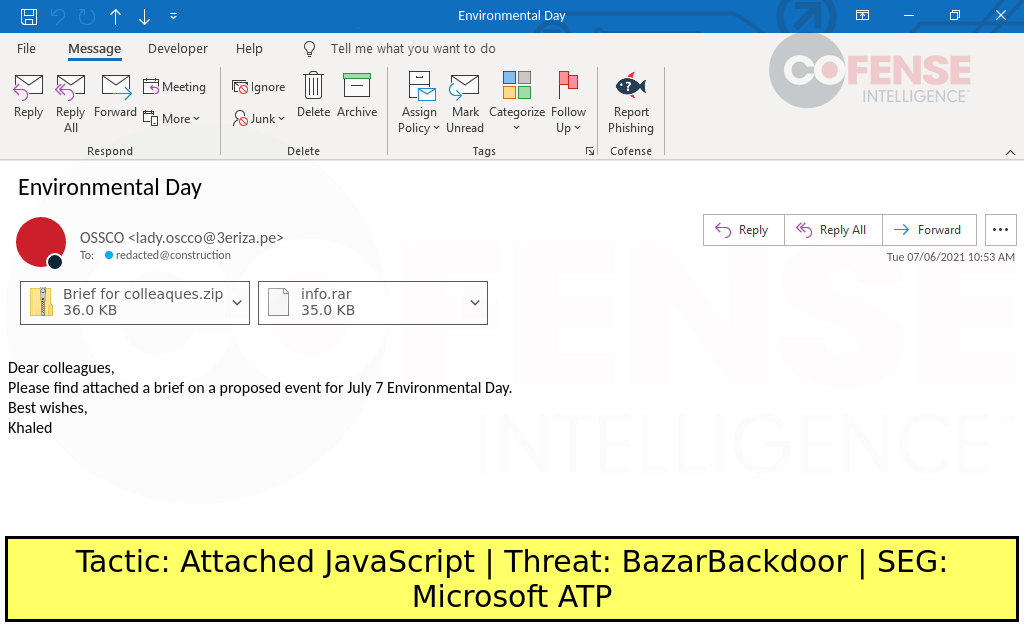
In the attachment were found both nested ZIP and RAR archives that contained a JavaScript file ultimately able to deliver Trickbot’s BazarBackdoor malware.
Trickbot’s BazarBackdoor is a stealthy backdoor that is typically used on corporate targets to provide remote access to the threat actor.
TrickBot malware targets the user’s financial information and usually spreads through malicious spam emails.
Originally a banking Trojan, TrickBot has evolved “into highly modular, multi-stage malware that provides its operators a full suite of tools to conduct a myriad of illegal cyber activities.”
It is known to use man-in-the-browser attacks to obtain information like login credentials and can use macros in Excel documents for downloading and deploying malware on the users’ devices.
The researchers at Cofense analyzed this malspam campaign and discovered that the role of the highly obfuscated JavaScript file was to download a payload with an image extension.
Nesting of various archive types is purposeful by the threat actor as it has the chance of hitting the SEG’s decompression limit or fails because of an unknown archive type.
This is important as obfuscated files can pose problems to a SEG if there are several layers of encryption for the payload, in this way increasing the chances of the malicious file passing undetected.
Once executed, the obfuscated JavaScript would download a [BazarBackdoor] payload with a .png extension via an HTTP GET connection.
BazarBackdoor works by downloading and executing the Cobalt Strike, a legitimate toolkit designed for post-exploitation exercises, to spread laterally in the environment.
Once they obtained access to high-value systems on the network, threat actors are able to launch ransomware attacks, steal sensitive information, or sell the access to other cybercriminals.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security