Contents:
Avaddon ransomware group made its appearance in 2019 for the first time, serving as a ransomware-as-a-service model (Raas) where 65% of ransomware for affiliates were negotiable, as stated in a report from eSentire. Now the threat group sent to Bleeping Computer a ZIP file with the decryption keys for all victims affected. It seems that the group is shutting down its operation.
2934 Decryption Keys Released by Avaddon Ransomware Group
On the 11th of June morning, Bleeping Computer, a website and forum covering ransomware topics since 2016, announced that they received a file named “Decryption Keys Ransomware Avaddon” on a link. This came alongside a password, claiming to be from the FBI.
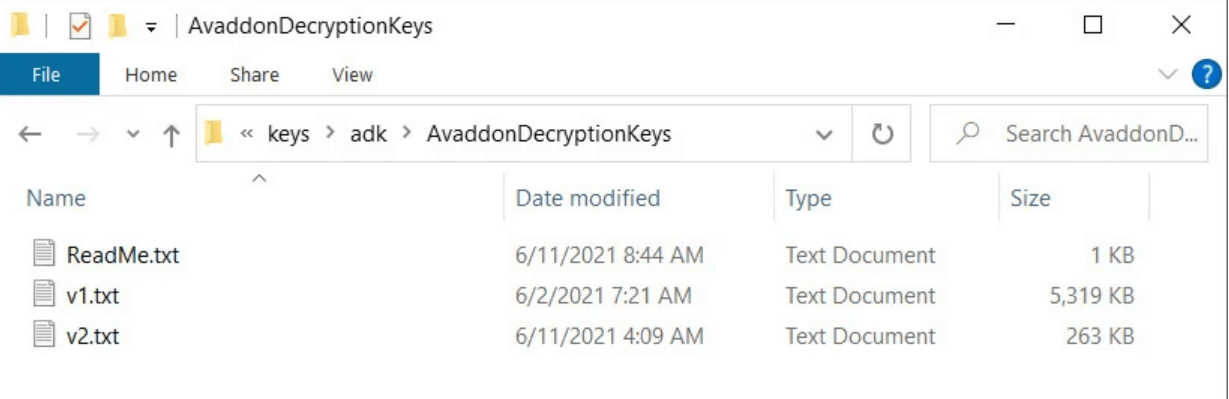
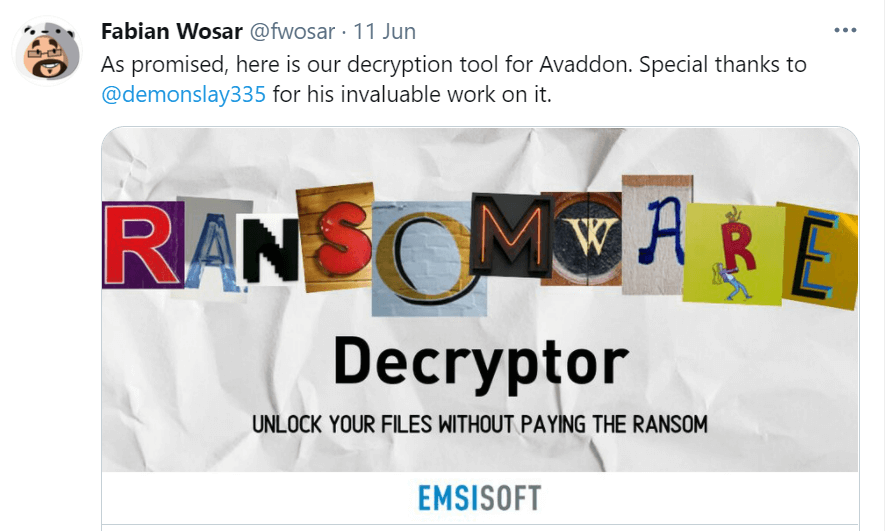
The matter was investigated by Michael Gillespie from Coveware and by the chief technology officer Fabian Wosar from Emsisoft. They confirmed the reliability of the files. Avaddon ransomware group released 2394 decryption keys for each of their cyberattack victims. Bleeping Computer shared the keys with Emsisoft, the latter providing the victims with a free decryption tool to help them recover their lost data.
Among the affected companies were also: EVGA (computer hardware company), Vistex software company, Henry Oil & Gas, PT Angkasa Pura I Indonesian government’s airport company, European insurance company AXA, New Jersey Bridgeway Senior Healthcare, and many more, according to ZDNet.
What Is The Reason Behind This Act of Goodwill?
Avaddon ransomware group’s gesture took everyone by surprise. However, this is not something actually new. Bleeping Computer reported in the past to have received decryption keys from threat actor groups. TeslaCrypt, Crysis, AES-NI, Shade, FilesLocker, Ziggy, and FonixLocker decryption keys have previously been made available. It often happens when these groups are about to release a new version or just close down their activity.
It is not clear the reason behind Avaddon’s disappearance, though, it is thought to be either law enforcement and government pressure or rebranding.
Recent cyberattacks came to American president Joe Biden’s attention, thus, they will be discussed at the June 16th Gevena summit with Russian President, Vladimir Putin.
Law enforcement institutions had previously issued warrants about multiple cyber-attacks. The Securityaffairs website stated that the Australian Cyber Security Centre (ACSC) and the Federal Bureau of Investigation (FBI) warned in May against the Avaddon ransomware campaign.
The targeted countries included Germany, France, China, Brazil, India, Spain, UK, countries from the US, and many more. The Avaddon ransomware group cyberattacks were intended for a variety of industries such as energy, healthcare, finance, government and manufacturing.
The Australian Cyber Security Centre (ACSC) is aware of an ongoing ransomware campaign utilising the Avaddon Ransomware malware. This campaign is actively targeting Australian organisations in a variety of sectors.
Others say that maybe the Avaddon ransomware group is just experiencing a rebranding phase, as threat actor groups did in the past. For example Nemty-to-Nefilim and Gandcrab-to-REvil.
Threat analyst Brett Callow also told Bleeping Computers:
Recent law enforcement actions have made some threat actors nervous – here’s the result. One less, and let’s hope others drop as well.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security








