Contents:
XLoader Malware, a popular virus known for stealing private information from Windows systems has been changed into a new strain, which is capable to also target Apple’s macOS operating system.
Cybercriminals are currently selling the XLoader malware on an underground forum as a botnet loader service that can “recuperate” passwords from web browsers and some email clients such as Chrome, Firefox, Opera, Edge, IE, Outlook, and others.
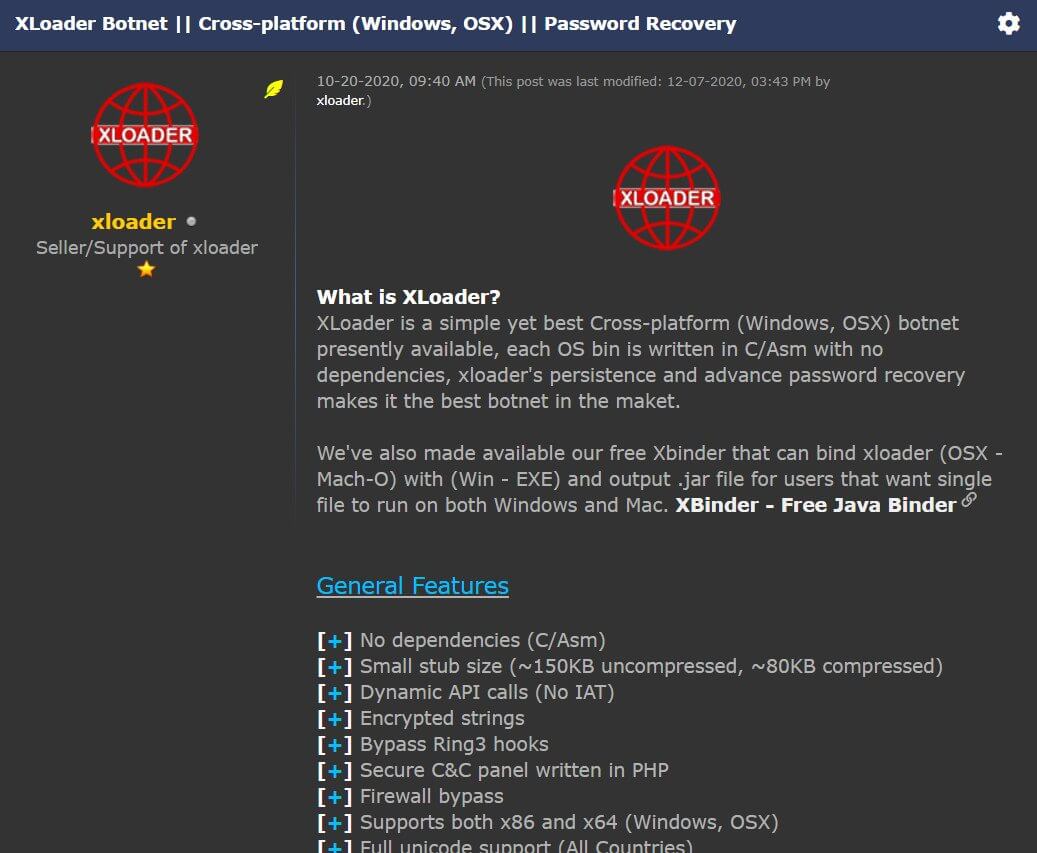
An evolution of the well-known Windows-based info stealer called Formbook, XLoader came out in February 2020 and has grown in popularity, announced as a cross-platform (Windows and macOS) botnet with no dependencies.
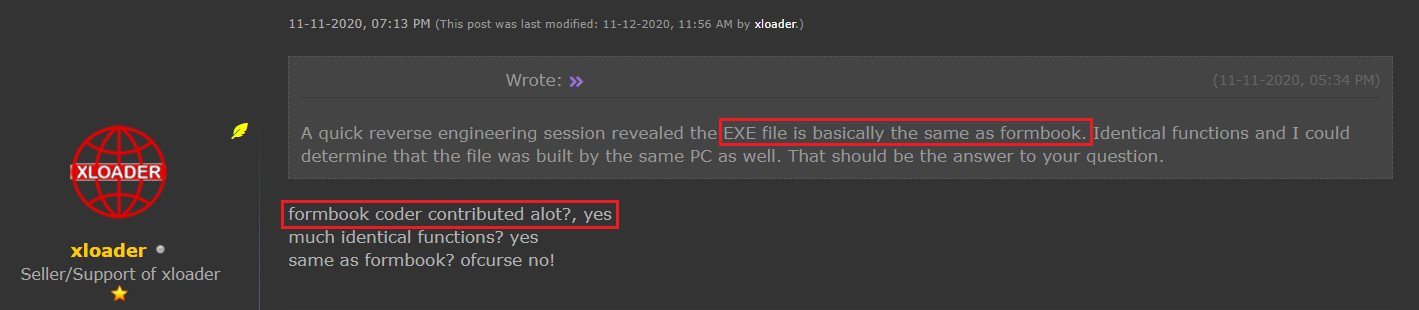
According to BleepingComputer, the connection between the two malware pieces was confirmed after a member of the community reverse-engineered XLoader and saw that it had the same executable as Formbook.
The Formbook’s creator contributed a lot to developing XLoader, and the two malware had similar functionality such as stealing login credentials, capturing screenshots, logging keystrokes, and executing malicious files).
Hackers can buy a macOS malware version on the Darknet for as low as $49 per month. The Windows version is more expensive as the seller asks $59 for a one-month license and $129 for three months.
By keeping a centralized command and control infrastructure, the authors can control how buyers use the malware.
Following XLoader malware 6-month activity up to June 1st, malware specialists at Check Point noticed that individuals from almost 70 countries asked for the malware, showing a significant spread all over the world, with more than half of the targets located in the U.S.
At the moment, Formbook is no longer advertised on underground forums, but it continues to be a powerful threat. It was part of at least 1,000 malware operations in the last three years and according to AnyRun’s malware trends, the malware takes fourth place over the past 12 months, after Emotet.
Check Point researchers state that XLoader malware is surreptitious enough to make it hard for a regular, non-technical user to observe it.
They recommend using macOS’ Autorun to check the username in the operating system and to look into the LaunchAgents folder [/Users/[username]/Library/LaunchAgents] and remove entries with dubious filenames.
According to Yaniv Balmas, Head of Cyber Research at Check Point Software, that XLoader malware “is far more mature and sophisticated than its predecessors [i.e. Formbook].”
macOS’s growing popularity brought it to unwanted attention from hackers, who are now seeing the OS as an attractive target.
While there might be a gap between Windows and MacOS malware, the gap is slowly closing over time. The truth is that MacOS malware is becoming bigger and more dangerous.
With the increasing popularity of MacOS platforms, it makes sense for hackers to show more interest in this domain, and researchers anticipate seeing more cyber threats following the Formbook malware family.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security








