Contents:
The traditional approach of individual system administration is no longer enough due to the complexity and variety of devices, each with its own strengths, weaknesses, and vulnerabilities. Unified Endpoint Management (UEM) has emerged as a solution, offering a centralized platform to manage these diverse endpoints efficiently.
Key Takeaways:
- Evolution of Endpoint Management;
- Definition and Role of UEM;
- Distinction Between UEM, MDM, and EMM;
- Benefits of UEM;
- Choosing the Right UEM Solution.
What Is Unified Endpoint Management (UEM)?
Unified endpoint management (UEM) is a collection of technologies that allow you to protect and manage a variety of devices and operating systems from a single dashboard.
U.E.M is, was, and will be the next evolutionary step of endpoint management, and it represents a brand-spanking-new approach to granular, multi-device control and management.
For an enterprise (or SMB or startup), “endpoint” can have any number of meanings – PC, Mac, laptop, tablet, wireless printers, smartphones, IoT devices, and anything in between.
Businesses have gone beyond using desktop PCs or laptops for every day, work-related tasks. At the same time, the need for extra…surveillance has increased exponentially. BYODs are great, but they can also become gateways for threat actors who would like nothing better than to sink their teeth into your company’s valuable data.
Endpoint management is the answer to closing all those security gaps, evaluating your cyber-resilience factor, and ensuring that the data stays where it’s supposed to. How does Unified Endpoint Management help?
Imagine being the curator of an enterprise ecosystem; spanning hundreds, maybe thousands of these endpoints. Believe it or not, system admins tend to lose count (and track) of all the devices hooked up to corporate.
In fact, according to a study by identity and access management company LogMeIn, 88% of system administrators couldn’t tell how many devices could access the company’s secure network.
Of course, the findings of this study should be taken with the proverbial salt grain – LogMeIn pooled data from the responses of 1,000 sysadmins, scattered through North America and Western Europe. Still, it does make a valid point, one that I will expand upon through this article.
Now, how does one tackle a complex corporate network? Well, the safest approach would be to deploy an endpoint management tool or software. On top of that, you will also need some sort of MDM to sort out mobile devices and an EMM (Enterprise Mobility Management) tool to, well, manage all the corporate assets. Did you think that I was done with the list?
Hardly – you will also require a client management system for stuff like client retention, remote diagnosis, operating system deployment, patching, and updating. Three different kinds of software just to eyeball that tangled web of devices. Naturally, each solution has its own quirks and strengths.
So, how is a Unified Endpoint Management system any different from MDM or EMM?
The Difference between UEM, MDM and EMM
The elephant in the room, in this case, is Mobile Device Management. UEM handles mobile devices (i.e. smartphones, tablets, and wearables running Android or iOS) and MDM handles mobile devices too.
Unified Endpoint Management is a critical tool for managing and securing the diverse range of devices in today’s IT environment. It simplifies the management of multiple device types, bringing them under a single management umbrella.
Steve Bigelow, TechTarget
So, what’s the difference? Why not stick with MDM? There’s no easy way of saying this, but the “M” in the acronym spells it very clearly – MDM covers ONLY mobile devices (BYODs, COPEs, and COBOs). MDM includes:
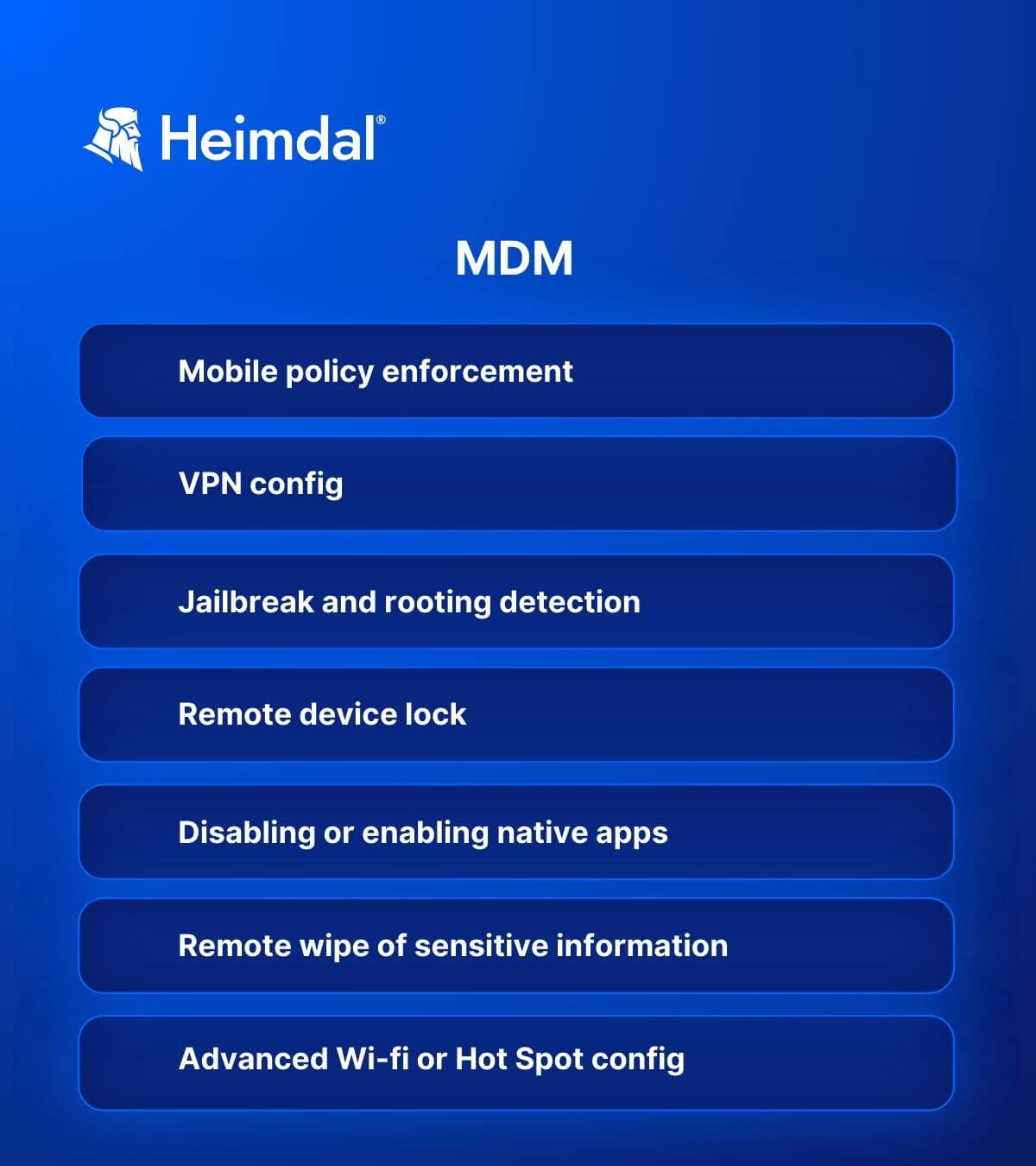
More to the point – MDM is good for mobile devices and bad for other endpoints (i.e. laptops, desktop computers, servers, etc.). With MDM out of the unification equation, what is the next option? EMM, of course.
Compared to MDM, EMM (Enterprise Mobility Management) is a little more inclusive. More specifically, EMM solutions can curate some endpoint-like components (e.g. wireless access points) and, of course, IoT devices.
In a nutshell, EMM will allow you to:
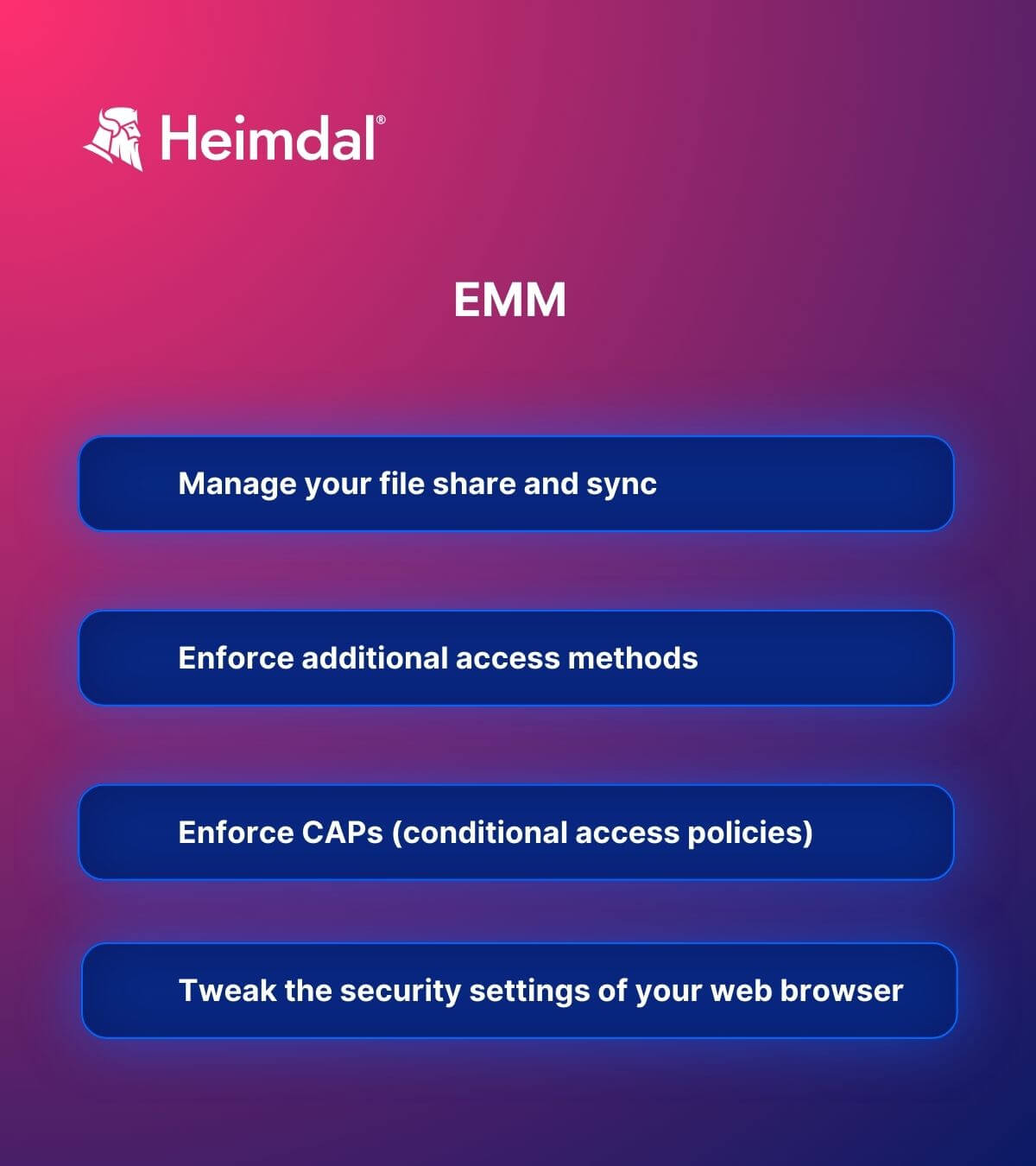
Even with an EMM solution in place, you’ve still failed to cover the endpoint part. What’s there to be done? Well, the obvious solution is to use some kind of tool, software, or solution that covers both issues (mobile + endpoint). In this case, the solution is a unified endpoint management tool.
Why Do You Need Unified Endpoint Management?
At a glance, a UEM can help you tackle both mobile and ‘non-mobile’ issues. Besides, Unified Endpoint, as a management methodology, can greatly increase the accuracy of your reporting and backlog analysis.
Essentially, you will have gained the ability to introduce a more granular, ‘EMMesque’ control over your desktop computers and similar devices, manage Internet-of-Things devices, and, of course, upgrade/update/patch both mobile and desktop apps – the process is simultaneous.
With a unified (and united) endpoint management system, you will be able to:
- Control, configure, and monitor all types of devices (i.e. Mac, Windows, Android, Linux, etc.) from a single (and unique) dashboard;
- Update, downgrade, and patch from a single console;
- Push security policies to every device, regardless of the operating system;
- Simplify the BYOD enrollment process;
- Achieve better control over the user-requested installation and uninstallation processes (e.g. system administrators can prevent users from installing a specific category of software on all devices hooked up to the corporate network);
- Identify the underlying condition. Without a centralized dashboard (and powerful analytics), we sometimes fail to identify the root issue. UEM’s reports can help you quickly figure out the root of the issue, deal with it, and figure out how to prevent future occurrences;
- Achieve an unprecedented level of automation. Speed, volume, and quality are vital to any business environment. Automation is the key to all three. As in the case of UEM, having all of your eggs in the same basket will certainly help with piecing together functional flows.
- Have increased visibility. The best analogy I can come up with is the Mind-map chart; UEM is one gigantic mind map with interwoven flows, endpoints lighting up like Christmas lights, and aggregated reports.
How to Choose the Best Unified Endpoint Management Solution for Your Company
Implementing and deploying a UEM solution is the first step towards increasing your cyber-resilience factor and, of course, achieving an unprecedented level of control over what happens inside (and outside!) your corporate network. In not so many words, it’s your go-to solution when everything goes boom around you.
Here’s what you need to look for when choosing the best UEM system for your company and the questions you should be asking before making a decision:
- OS support: Can it manage endpoints with different operating systems? Windows? ioS, Android? macOS?
- BYOD support: Will it support Bring-Your-Own-Device programs?
- Endpoint security policies: Will this UEM system respect security policies regarding password setting, jailbreaking, malware detection, (mobile) threat detection, and so forth?
- Remote work support: Can it support a remote or hybrid workforce?
- Automation: How much of this UEM solution is automated? How much time will my administrators spend on deployment and management?
- Integration with other solutions: How well will this system integrate with other IT solutions we use?
- Compliance: Does this UEM system come with compliance certifications with regulations like GDPR, HIPAA, and so on?
How Can Heimdal™ Help
Heimdal Security’s EDR/ EPDR suite is the closest you can get to authentic Unified Endpoint Management and it consists of:
- Heimdal Threat Prevention, the company’s DNS traffic-filtering solution makes sure that malware doesn’t set foot in your endpoints;
- Our Next-Gen Endpoint Antivirus, with four layers of impeccable detection powered by Heimdal™ Security’s unique intelligence, will help you detect and mitigate even the most complex threats;
- Heimdal Patch & Asset Management, our automatic patching, and updating engine keeps all your favorite apps and software up to date, regardless of the machine’s status, time zone, or package size. The updating/patching module also allows your system admin to deploy proprietary software on all the machines;
- Last, but not least, Heimdal Privileged Access Management, our Privileged Access Management (PAM) solution will help you get rid of creepers, increase your UA hygiene, and take full control of what goes on inside your machine.
As a bonus, Heimdal™ Privileged Access Management is the only PAM solution on the market that automatically de-escalates user rights on threat detection.
It is worth mentioning that all Heimdal cybersecurity solutions are unified under a single dashboard, and any of the modules can be used as stand-alone or bundled, as needed.
Wrapping Up
Unified Endpoint Management is poised to be the next best thing that happened to sysadmins since cloud computing. Has your company adopted UEM? If so, hit the comments and let me know what you think about this amazing piece of technology.
If you liked this article, follow us on LinkedIn, Twitter, Facebook, and YouTube for more cybersecurity news and topics.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security










