Contents:
The web surfing history of millions of people was intercepted yesterday in a huge data leak. Large Swedish companies, such as Volvo, SAS, Ericsson, Husqvarna, and SKF have been affected, as originally reported by the Swedish newspaper Dagens Nyheter. About 40,000 people involved in the cyber incident allegedly are Swedes.
Spyware in Browser Extensions Enabled the Attack
The data spill was caused due to a spy code installed in Chrome and Firefox add-ons, which allowed the browsing history of millions of users to be harvested and sold.
A part of the leaked data comes from some of the largest organizations in Sweden. The database contained information such as discussions between employees, downloaded files, and internal confidential information. More precisely, it was possible to see exactly what people did online and although the information was considered to be anonymous, their identity could be confirmed.
The Failure of a SpaceX Rocket Engine Was Also Leaked
According to security engineer Sam Jadali, other major international companies have been involved as well. For instance, information from the space company SpaceX regarding the failure of a rocket engine was revealed. The vehicle was used to transport astronauts to and from the International Space Station (ISS).
The Company Behind the Data Leak
The information was collected and sold by Nacho Analytics, which is ending its activity now that the leak has been brought to light.
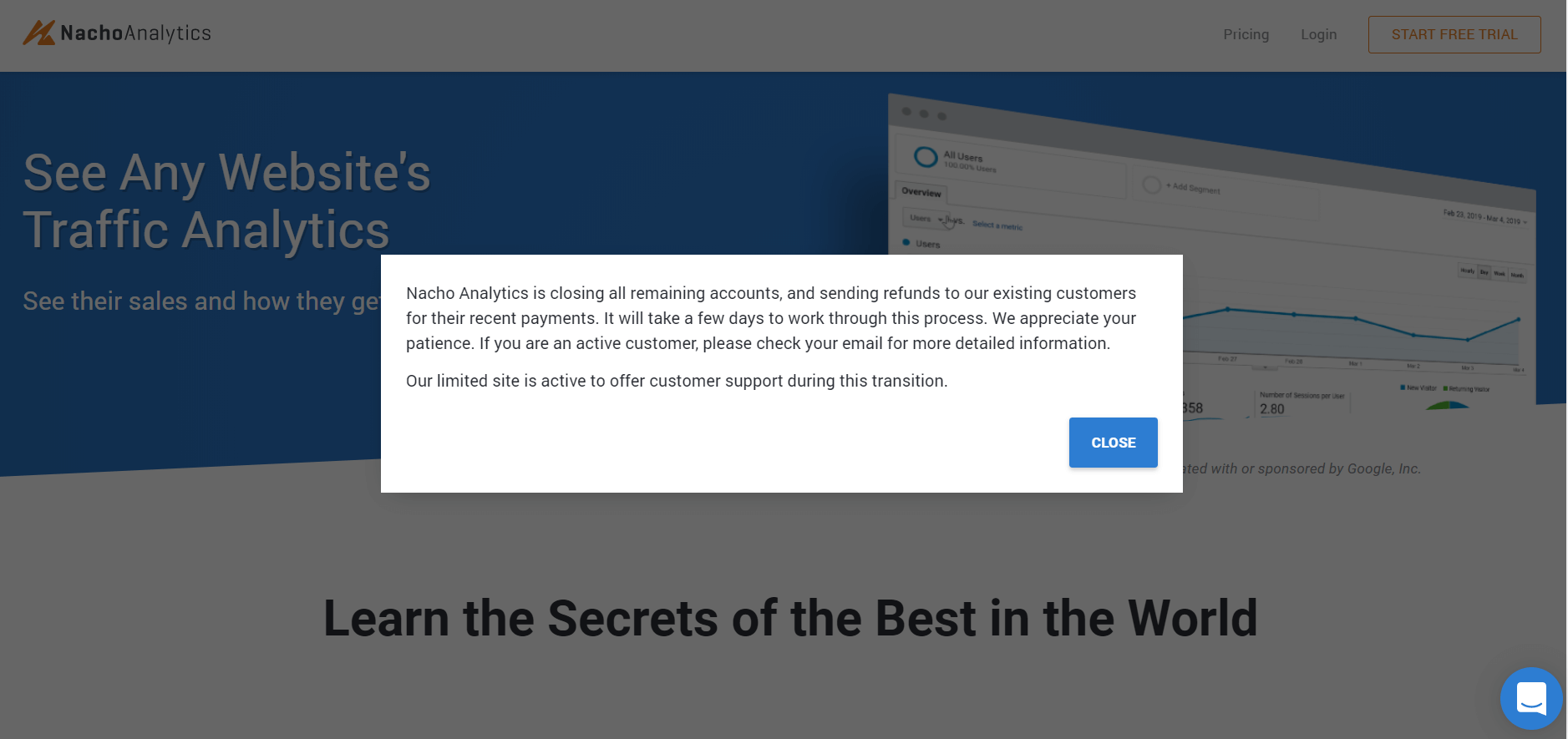
This is the pop-up message that is currently being displayed on their website:
“Nacho Analytics is closing all remaining accounts, and sending refunds to our existing customers for their recent payments. It will take a few days to work through this process. We appreciate your patience. If you are an active customer, please check your email for more detailed information.
Our limited site is active to offer customer support during this transition.”
Browsing habits are a method of studying customer patterns and monitoring competitors. This leak is similar to the one we’ve seen in the Cambridge Analytica scandal, which could abuse Facebook data to be used in political campaigns, writes SVT.
Why Did the Data Leak Happen?
The reason is that many companies use browser-based tools. And if an employee accesses a browser extension compromised by spyware, the activity within the tool can also be intercepted by cybercriminals.
Our CEO, Morten Kjaersgaard, has spoken with IT-Kanalen about how serious the problem is.
In his view, the issue seems to be greater than we realize. Specifically, any extension could be used by cybercriminals to access sensitive data. The reason is that these add-ons are not part of a company’s internal system, but developed by third parties. When users install a plugin in a browser, a port opens to the underlying engine – in this case, Chrome or Firefox – where it gets access to data other than it should have access to.
On a more positive note, the issue was discovered early, and this way we can get the chance to better understand it and find solutions. We should somehow be glad that the attack did not hit IE, which is more commonly used because this way the damage would probably have been significantly higher, says Morten Kjaersgaard.
How can we reduce the risks?
The simple answer would be to disable all plugins. But since this is rarely a viable solution, here are the recommendations for companies and consumers.
Advice for Companies
Companies should follow several steps. First of all, their IT department should design some form of policy-based system for deciding which add-ons should be installed and also know how they should be handled and monitored. There are existing solutions that are partially already integrated into Chrome.
Secondly, traffic should be monitored in real-time. This way, companies can detect early on whether systems connect and send data to suspicious locations. If this practice is combined with DNS protection and IP filtering, then you will have a great security foundation for your company.
Advice for Consumers
The most obvious recommendation would be not to install any extensions. But if you need to do it, always make sure you only have installed a few add-ons that you really depend on. What’s more, browser extensions should come from trusted, reputable sources and not from any unknown sites or companies.
By using DNS and IP filtering in combination with traffic monitoring and firewalls, both consumers and companies will play their part in the fight against cybercriminals. And this is something that we must all start with as soon as possible, Morten Kjaersgaard concludes.
Swedish speakers can read the full interview with Morten Kjaersgaard, Heimdal Security’s CEO, here.
Does your company need a cybersecurity solution to prevent Spyware and the most advanced types of malware?
Get in touch today to learn how we can help you.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security








