Contents:
On today’s episode of „Digital Hoarders”, I share how we can all make our PCs more organized and less insecure.
Seriously now, if it were a real show, probably over 70% of Internet users (personal estimate) would be contenders for “who has the most apps installed.” I don’t have an official statistic for it, but if your desktop looks like this:
Then you may have some work to do behind the scenes. A messy desktop can be the sign you need to get on with digital spring cleaning.
A cluttered PC is a vulnerable PC
Curious by nature, us Internet users have turned into digital hoarders, installing apps and all kinds of software that would make our work easier, faster or our lives more fun. And, just like an uncleaned fridge may start to smell at some point, some of these apps can go bad as well. Not in the sense that they’ll turn into weapons of cyber attack overnight, but in the way that they’ll become vulnerable to attack.
Cybercriminals frequently and automatically scan websites and PCs with different types of malware to see if there are any vulnerabilities they can use to penetrate that website or system. And they find these backdoors a lot more often than you can imagine.
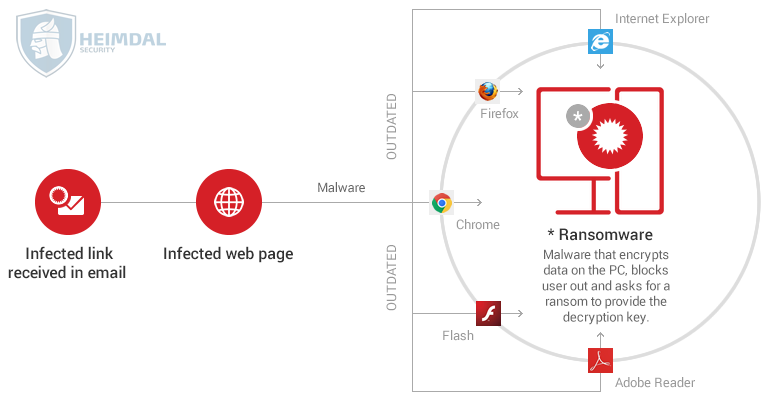
For example, here’s how ransomware can exploit security holes in your outdated browsers/apps to infiltrate your PC:
All it takes is clicking on an infected link in a spam email that will redirect you (invisibly) to an infected website, where the ransomware will be downloaded from. Fast forward a couple of minutes (or less, if you don’t have that many files), and all your data is encrypted, while attackers await their ransom to give you the decryption key. This can also happen to your smartphone.
And mind my words: this is not an unlikely scenario.
What are software vulnerabilities?
This is a perfectly legitimate question. You’ll hear and read a lot about them, so it’s time you found out what they really are.
In order to take advantage of this flaw to infiltrate your PC, an attacker will have to gain access to the flaw and have the capability to exploit it.
An example of a software vulnerability is buffer overflow. This is a very common weakness, where a data input uses up more space than it’s given, so it spills over into different locations, causing an app to crash or giving cyber attackers a way into your PC.
Buffer overflow is also a method that cybercriminals can use to gain administrator right to your system. Once that happens, they can run malware on your PC without you knowing it. They can also turn off your antivirus protection without your knowledge, leaving you even more vulnerable. Moreover, they can gather data such as details about your PC, email addresses stored locally in your apps and more, and send it to the servers they control. Data harvested from victims of cybercrime is often dumped on the dark web, where it’s sold to other attackers who can use it in subsequent attacks.
If, at this point, you’re saying to yourself:
We can’t blame you. But it’s not about theatrics. It’s about how things actually happen, most often unseen. This is because all this stuff cannot be observed with the naked eye unless you’re a really good hacker (the white hat kind, not the evildoer type).
And all that can start with an outdated app I forgot I had installed?
Yup, that’s right!
But it can also come from applications you use more frequently, but don’t update when you should, such as browsers (Chrome, Firefox, Edge, etc.), browser plugins (Adobe Flash, Silverlight, screenshot tools, PDF readers, etc.) and other types of software (instant messaging apps, email apps, games, etc.). Even your operating system is included in this category.
You’ll often read that software such as Java or Adobe Flash is cyber criminals’ sweet spot. These two seem to be plagued by vulnerabilities, which is why most malware targets them, to begin with. Unfortunately, few users are aware of this, and even fewer do something about it (i.e. remove the software or use adequate protection).
And this brings us to your next question, which I’m sure popped up in your mind by now:
What’s all the fuss about software updates, anyway?
Software updates do not include only performance improvements and new features. Almost every time you receive an update, you can be sure that it packs security fixes as well. That’s why updates are crucial and you should install them as soon as they become available: because they can put a plug in the security holes in your PC and make your system safer.
In the spirit of keeping things real, you should understand that updates can’t fix all of your security problems. There are glitches in the software that even the software makers aren’t aware of. Sometimes, cybercriminals will discover these weaknesses on their own and start exploiting them until the makers can release an update. That’s how Zero Day vulnerabilities are born (these are the worst kind because the bad guys get to be the first to make the call).
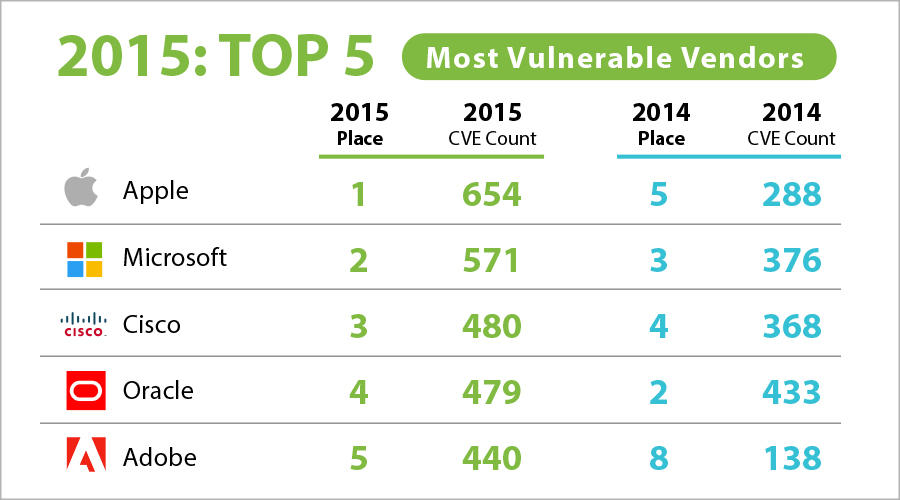
Maybe you’ll be surprised to find out that the most vulnerable software vendor in 2015 was…. Apple! The CVE count you see in the table is the number of vulnerabilities that the software makers had in 2015 and the places they had in the general vulnerabilities chart called CVE details.
Software is mind-blowingly complex and its interaction with hardware even more so. This goes both for PCs and smartphones, tablets and other devices. So in order to ensure your system is as safe as possible, we always advocate for a multi-layered approach to online security. But first, let’s start cleaning out your digital closet.
The great app purge of spring, 2016
Get into the spring cleaning mood, because we have just the toolkit your need!
1. Uninstall unused apps
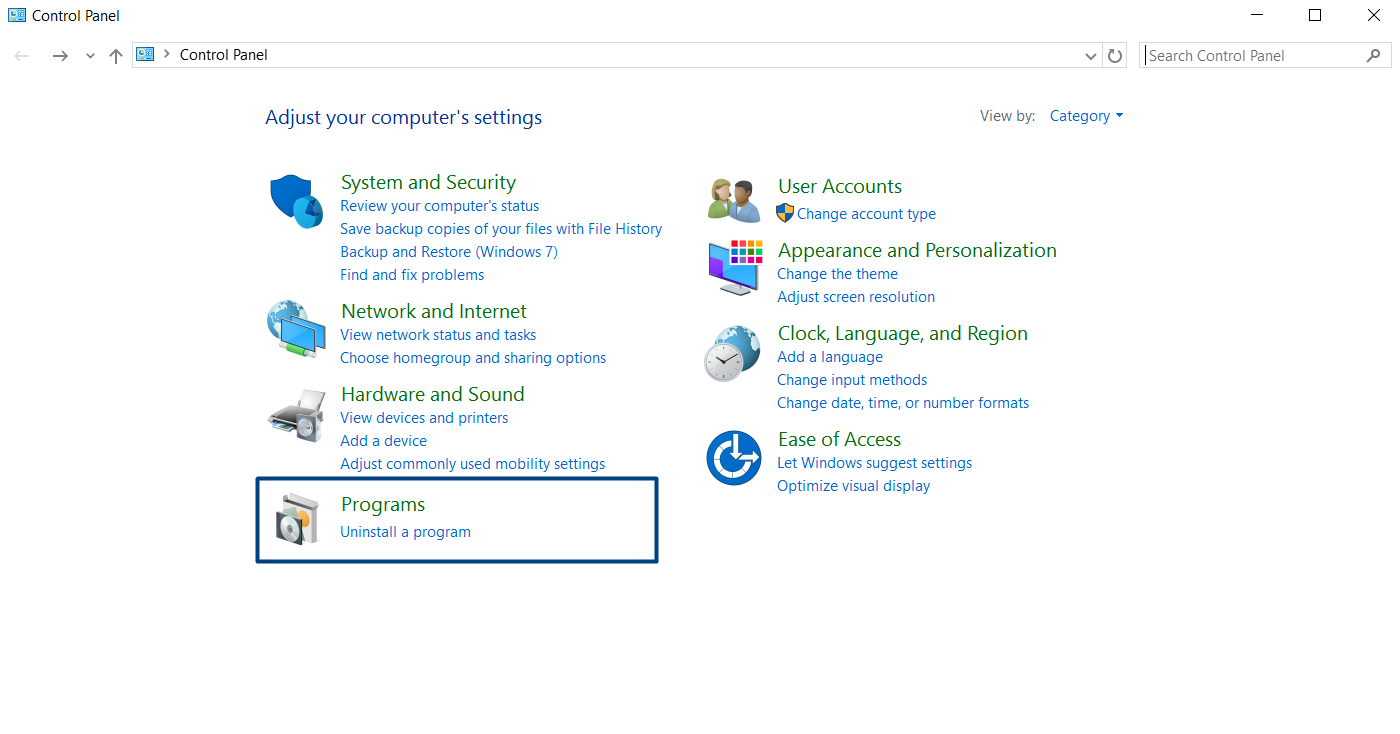
In Windows, go to Control Panel -> Uninstall or Change a Program and click on the “Installed on” column to sort your apps.
This will help you see which are the oldest apps you have installed and sort through them so you can delete what you don’t use constantly.
You can also sort applications by size, so you can clean up space on your PC and maybe even make it run faster. Ah, the benefits of decluttering!
And because the Windows uninstall tool can sometimes leave some elements even when you thought you got rid of an app for good, you can try using CCleaner to delete any traces of your old apps.
And if you’re looking to optimize your PC even further, check out this guide from How to Geek on PC maintenance. I think you’ll find it very helpful.
2. Check your browser plugins
Browser plugins are an insidious security threat. They seem completely harmless, but the truth is that they can hurt both your privacy and your security.
So it’s good to keep things under control, especially because cybercriminals use browsers as the main attack tactic:
Though not in the top five, Google and Mozilla were in the top 10 and the majority of vulnerabilities were from the browsers themselves. Google Chrome with 185 of their total 321 CVEs falls in at No. 8 for products and puts Google at No. 6 on the vendors list. Mozilla Firefox with 177 of their 188 CVEs falls in at No. 9 for products and No.8 on the vendors list.
Source: The most vulnerable software vendors of 2015
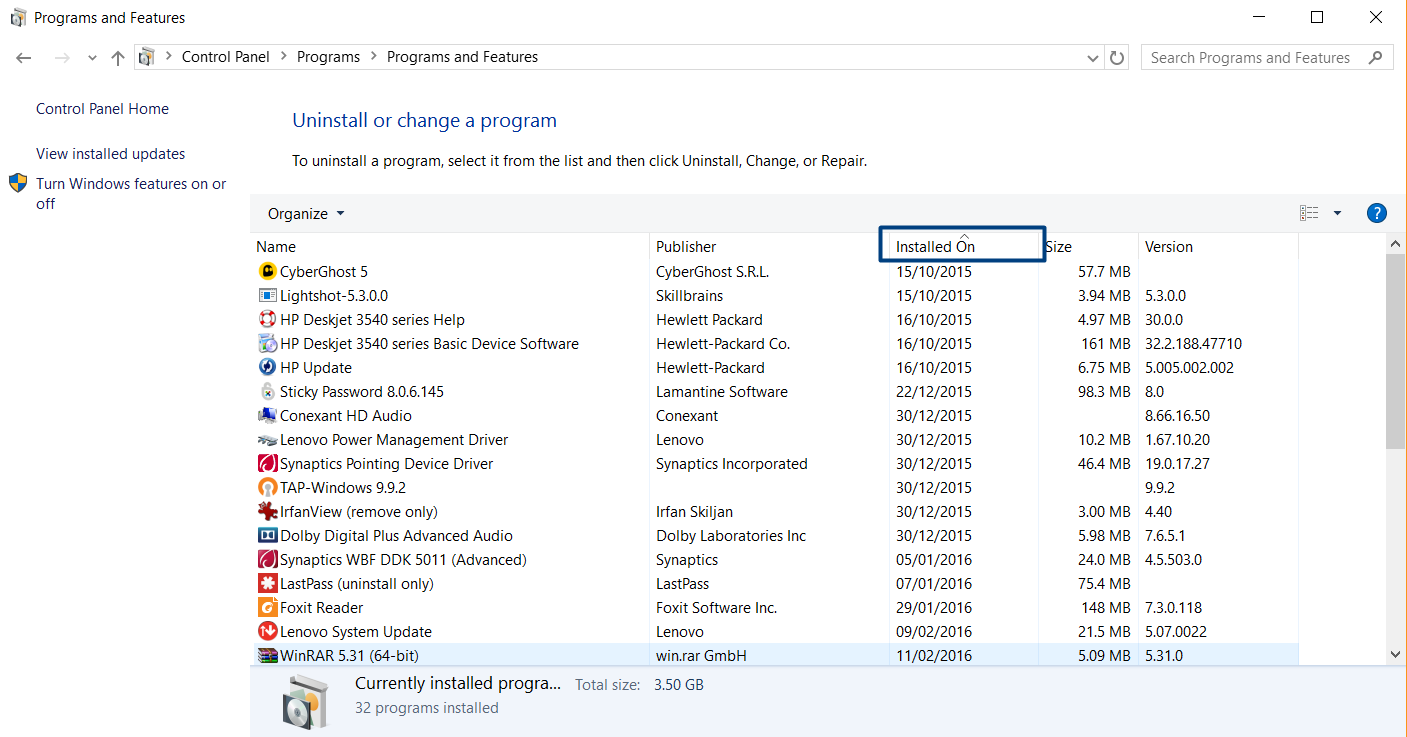
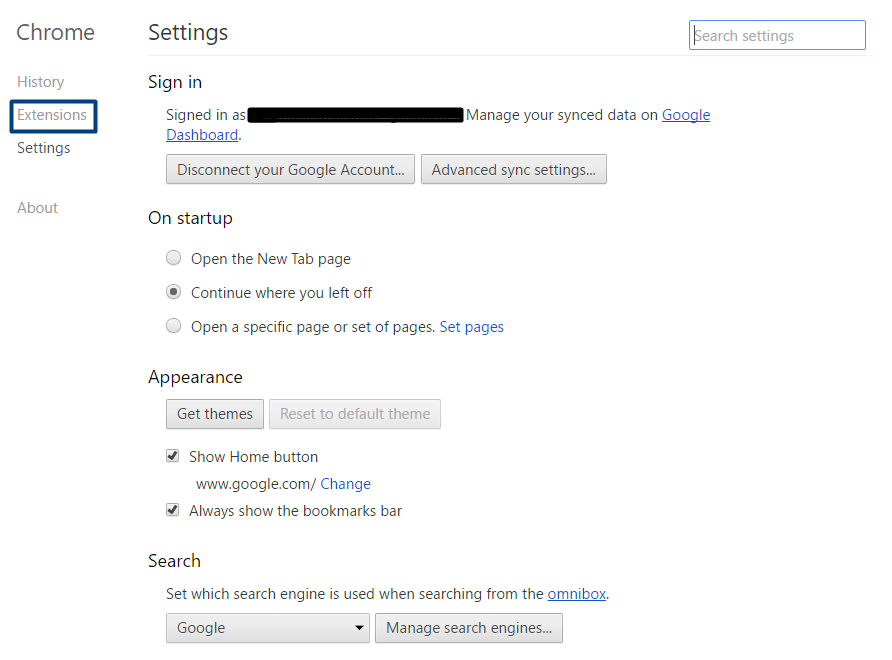
How to clean up your extensions in Chrome:
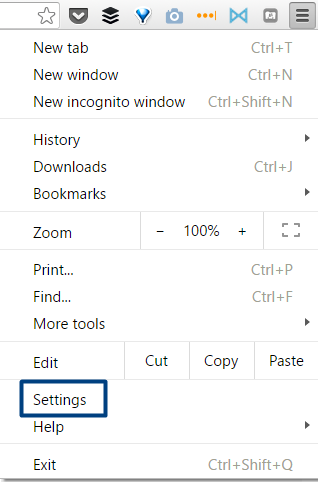
Go to your Chrome menu and go to Settings:
Choose Extensions:
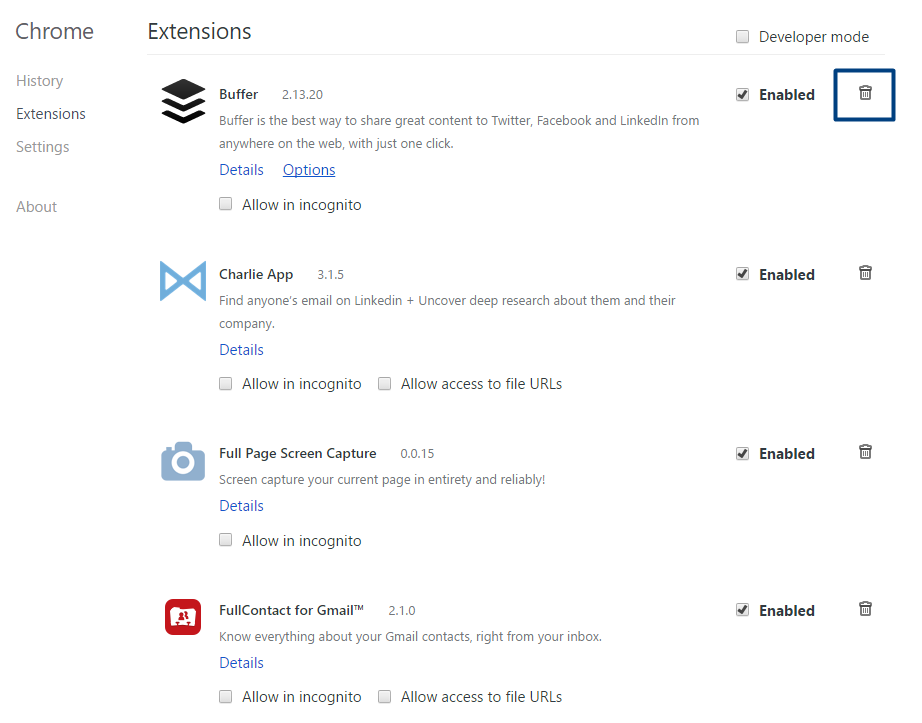
Delete the extensions you don’t need or use anymore:
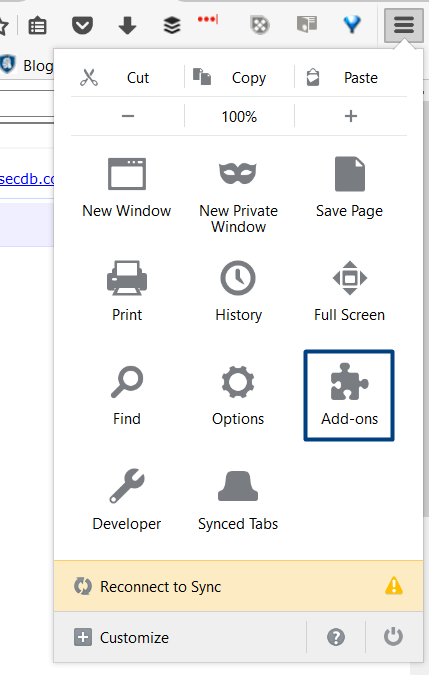
How to clean up your extensions and plugins in Firefox:
Go to your Firefox menu:
Choose Add-ons or Extensions:
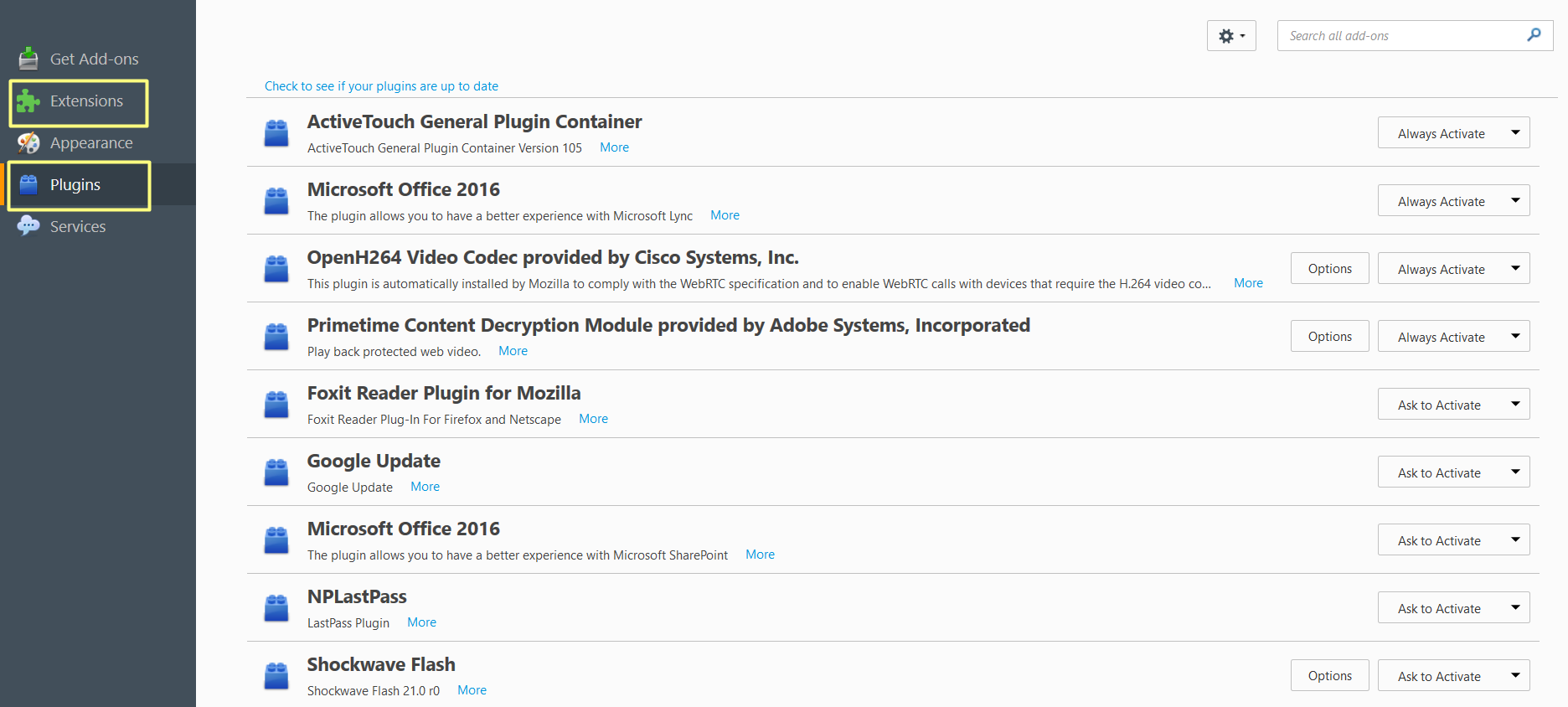
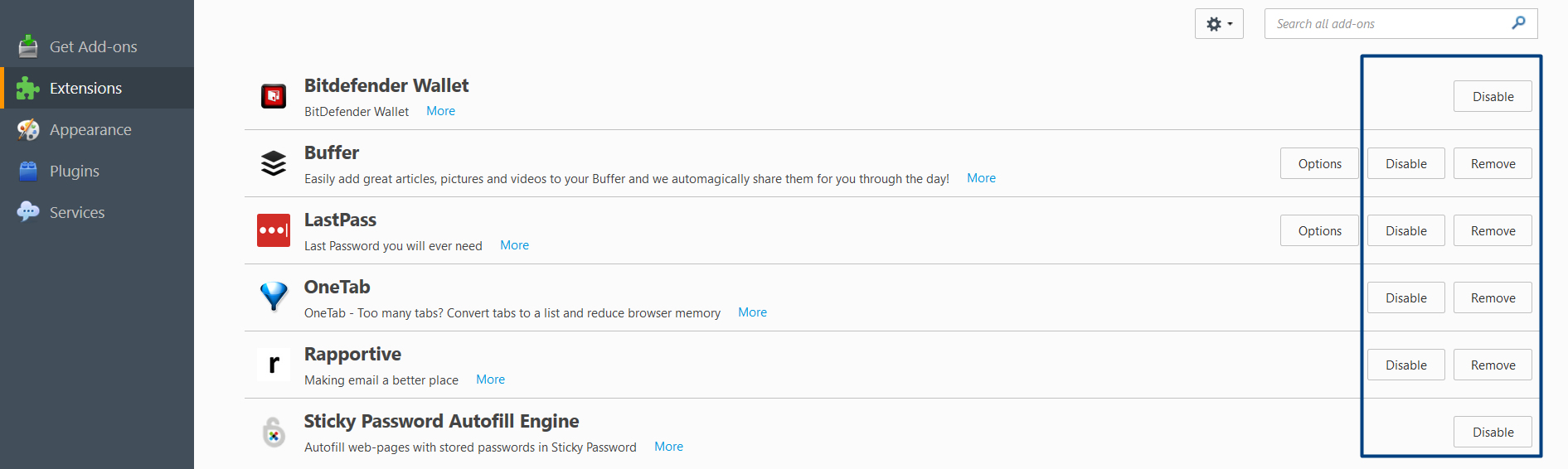
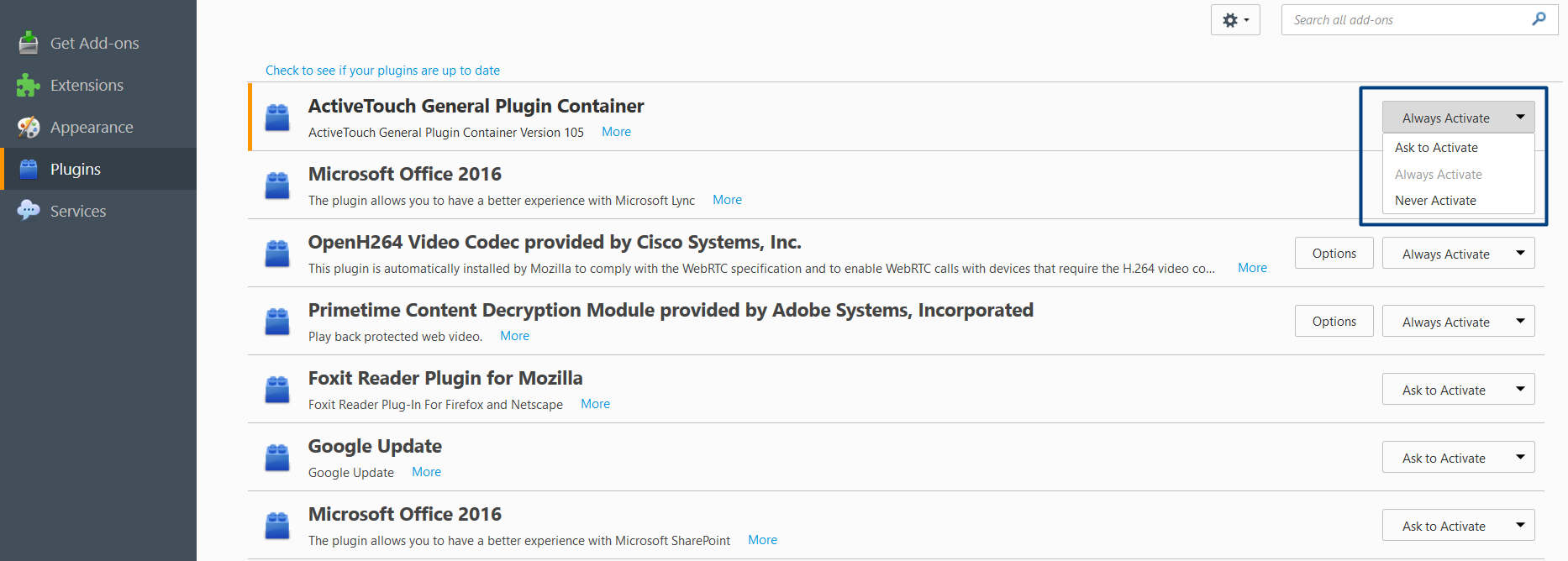
For extensions, choose to disable or remove them:
For plugins, choose either to “Never activate” or “Ask to activate” for those plugins that you know are vulnerable to attack. Or for all of them if you want to be really careful.
You may have toolbars installed or any other type of crapware that comes with shady apps.
3. Delete software installers
Once you’ve used them, there’s no reason to keep them on your PC. If you have them at hand, you may be tempted to install older versions of software, which may be flawed and, consequently, vulnerable.
Also, be very careful where you choose to download software from. Not all download portals are trustworthy and the installers you get from them are sometimes filled with bloatware (or crapware), such as toolbars and other add-ons. The best is to go directly to the software maker’s website and get the installer from there. You can make sure you’re getting the latest version, that the download is secure and that there’s no bloatware involved.
4. Automate your software updates
Now that your PC is clean of old apps and plugins, it’s time you eliminated the hassle of software updates.
The simplest way to do it is to use a free tool, like Heimdal™ Free, that can monitor and update your apps automatically and silently, in the background.
This will save you time and effort, and it’ll make sure that you always have the latest version of your favorite app, both feature-wise, and especially in terms of security.
Conclusion
There’s no time like the present to do this simple spring cleaning that can spare you many headaches down the road. The more organized your digital life is, the fewer backdoors cybercriminals can exploit. And remember that our lives are more dependent on our digital existence than we think.











 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security