Contents:
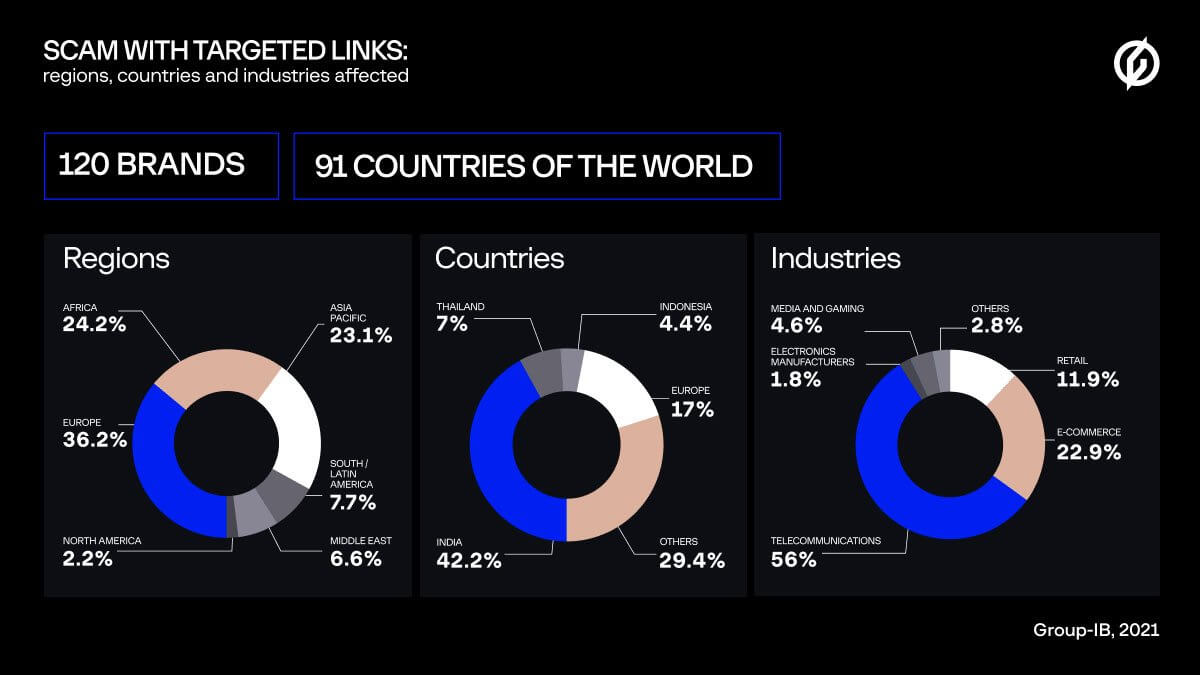
Hackers impersonate popular brands and trick victims from the United States, Canada, South Korea, and Italy to provide them with personal and financial information, new research from Group-IB says. According to experts, cybercriminals have made almost $80 million monthly employing these scams, money obtained from 10 million people in 91 countries.
How These Types of Scams Work
Experts have described which tactics scammers use to fool victims. Thus, targeted users normally receive an invitation to be part of a survey that comes with an alleged prize. In the received offer, there’s a link that redirects to the website where the survey can be found. To attract victims, from a marketing point of view meaning to “generate leads”, scammers use all kinds of methods like contextual advertising, SMS, mailouts, or pop-up notifications.
To attract users to the final scam websites, scammers register look-alike domain names to the official ones. Less frequently, they were also seen adding links to the calendar and posts on social networks. After clicking the targeted link, a user gets in the so-called traffic cloaking, which enables cybercriminals to display different content to different users, based on certain user parameters.
The download for this “brand survey” page takes a lot of time, while users are redirected to various pages, a tactic that facilitates time for hackers to collect personal user data like time zone, language, IP address, and so on. This helps them customize the final content in relation to what they discovered about the user. The final malicious link is tailored per user and the victim will be required to answer some questions in order to obtain a prize from a supposedly popular brand and then to fill out a form with personal data like full name, email address, phone number, postal address or credit card info in order to receive the so-called prize.
What Can Scammers Do with All This Data?
The research underlines the fact that after obtaining this kind of private data, hackers can buy things online, register false user accounts or the victim’s information could be sold on the black market. Basically, the victims’ data will be made public and they can even be required to pay a tax in order to receive the prize.
Statistics on This Scam Operation
The Group-IB researchers say that 60 known scam networks use at the moment targeted links posing as no less than 121 popular brands to perform their giveaways.
For every network, an average of 70 different Internet domain names are used, however, some of these malicious campaigns seem to work with fewer domains too.
How to Recognize a Scam
Since brands normally organize giveaways during holidays, no wonder scammers have found this method to impersonate them and go phishing!
However, you should be vigilant and check on the official website or social media page of a brand if there’s such a giveaway or survey with prizes ongoing and that if the website address associated with the email account really belongs to an official brand.
Nevertheless, what definitely should make you raise an eyebrow is the simple question: why would a popular brand ask for your card payment info like CVV or the expiration date if you’ve won a prize since for its delivery the company only needs a name, a phone number and a postal address to send the gift to you?
How Can Heimdal™ Help?
Phishing it’s all around these days and you should take into consideration to protect your business with efficient tools like our E-Mail Fraud Prevention as well as Email Security. The first keeps Business Email Compromise (BEC) and CEO Fraud away through its 125 analysis vectors, effectively protecting your critical business assets and e-mail accounts. The second product combines proprietary e-mail threat prevention with Office 365 support to fight against threats delivered on the email.
If you liked this article, follow us on LinkedIn, Twitter, Facebook, Youtube, and Instagram for more cybersecurity news and topics.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security








