Contents:
Linux users should be on guard for the new variant of RansomExx ransomware that was recently presented by threat group Hive0091.
Just like BlackCat, Hive, or Luna, RansomExx2 was rewritten in Rust, which seems to be the trend right now among cyber criminals.
RansomExx2 was developed to run on Linux systems, but will probably soon enough also have, as its predecessor did, a Windows version.
What Made Threat Actors Switch to Rust
Also known as Defray777, RansomExx has been active since 2018 and is responsible for various ransomware attacks on famous corporations and government agencies from all around the world.
Switching to Rust language is not about achieving new functions, but rather aligning with a new trend of developing ransomware in programming languages that are not that famous. The trend has gained popularity among malicious actors because malware written this way is harder to detect and provides better cross-platform flexibility.
Malware written in mainstream languages appears to be easier detected by antiviruses and cybersecurity researchers assume that this is the main reason threat actors are now turning to employ languages like Rust.
Malware written in Rust often benefits from lower [antivirus] detection rates (compared to those written in more common languages) and this may have been the primary reason to use the language
How Does Ransomexx2 Work
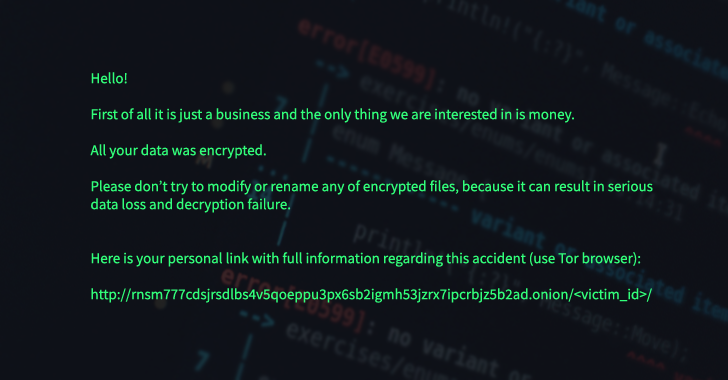
The new Rust version is actually very much like the C++ older one, and it first has to get a list of directory paths to encrypt. It goes through each directory, enumerates, and encrypts the files. In the process, each one of the encrypted files gets a new file extension. In the end, the ransom note is dropped in the encrypted directories.
Even if functionality was not significally upgraded by the rewriting of RansomExx in Rust, the effort points to a focus of this notorious ransomware family to developing and searching new ways of avoiding detection.
If you liked this article, follow us on LinkedIn, Twitter, Facebook, Youtube, and Instagram for more cybersecurity news and topics.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security