Contents:
QNAP Systems, Inc. is a Taiwanese company that specializes in network-attached storage equipment for applications such as file sharing, virtualization, storage management, and surveillance.
What Happened?
The DeadBolt ransomware organization is encrypting QNAP NAS systems all around the globe, claiming that they are exploiting a zero-day vulnerability in the device’s firmware to do so.
When the attacks began QNAP clients discovered that their files had been encrypted and that their file names had been added with the.deadbolt file suffix.
#QNAP seem to have a new #Ransomware attack: #Deadbolt. What’s the fix, QNAP?
Each customer being asked to pay 0.03 #BTC pic.twitter.com/1XS1liTZn2— Wireless-News (@news_wireless) January 25, 2022
QNAP device’s login page is hijacked, and a message reading, “WARNING: Your files have been locked by DeadBolt” is shown instead of ransom notes being placed in each folder on the device.
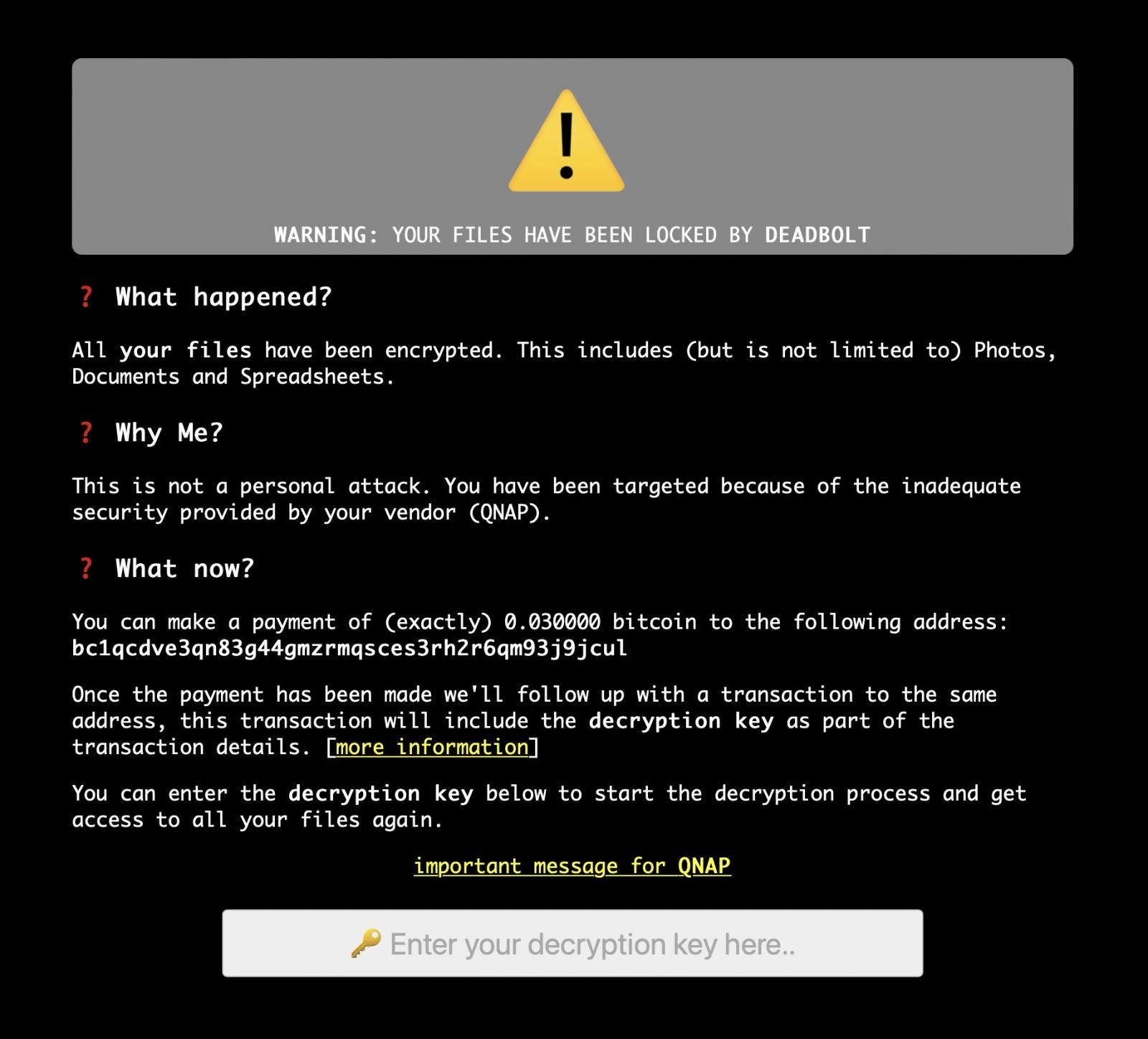
As BleepingComputer reports, the page advises the victim that they should send 0.03 bitcoins (about $1,100) to a Bitcoin address that is unique to each victim, which is provided in the message.
Following compensation being received, the threat actors say that they will conduct a follow-up transaction to the same address that will contain the decryption key, which may be obtained by following the steps provided in this document.
This decryption key may then be typed into the device’s screen to allow the files on the device to be decrypted. At this time, there is no guarantee that paying a ransom would result in the delivery of a decryption key, or that customers will be able to decrypt their data after doing so.
Because the threat actors claim that the assault is being carried out using a zero-day vulnerability, it is highly recommended that all QNAP customers unplug their devices from the Internet and put them behind a firewall as soon as possible.
A message for QNAP may be found on the main ransom note page, and clicking on it will bring up a message from the DeadBolt gang that is tailored exclusively for QNAP and its customers.
Make a bitcoin payment of 50 BTC to bc1qnju697uc83w5u3ykw7luujzupfyf82t6trlnd8.
You will receive a universal decryption master key (and instructions) that can be used to unlock all your clients their files. Additionally, we will also send you all details about the zero-day vulnerability to security@qnap.com.
How Can Heimdal™ Help?
Ransomware is one of today’s most widespread and severe cyber threats, with usually dangerous repercussions. Learning how to avoid it should be a top priority for any business concerned about the safety of its employees, clients, partners, assets, money, and business processes.
In the fight against ransomware, Heimdal Security provides its customers with an exceptional integrated cybersecurity suite that includes the Ransomware Encryption Protection module, which is universally compatible with any antivirus solution and is completely signature-free, ensuring superior detection and remediation of any type of ransomware, whether fileless or file-based (including the most recent ones like LockFile).
If you liked this article, follow us on LinkedIn, Twitter, Facebook, Youtube, and Instagram for more cybersecurity news and topics.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security








