Contents:
A jump in the number of eCh0raix ransomware attacks on the systems of QNAP NAS devices has been reported by users. The ransomware is also known under the name of QNAPCrypt.
It seems that the cybercriminals behind eCh0raix started to increase their activity a week before the Christmas holidays. They are targeting devices with admin privileges to take control over them.
The Number of eCh0raix Cyberattacks Hitting QNAP NAS Devices on the Rise
According to BleepingComputer, users of the publication’s forums who manage QNAP and Synology NAS systems have started to report more eCh0raix attacks around the 20th of December.
The ID ransomware service also confirms the increased number of cyberattacks between December 19 and December 26.
Some users say that they did not keep their devices properly secured, others are of the opinion that the QNAP’s Photo Station’s vulnerability permitted the attacks on NAS devices to intensify. However, currently, the initial infection vector is not clear.
How the eCh0raix Attack Unfolds
As per the same publication mentioned above, the threat actors behind eCh0raix ransomware manage to perform file encryption on the NAS systems by means of a user they create in the admin group. QNAP users say that pictures and documents were encrypted.
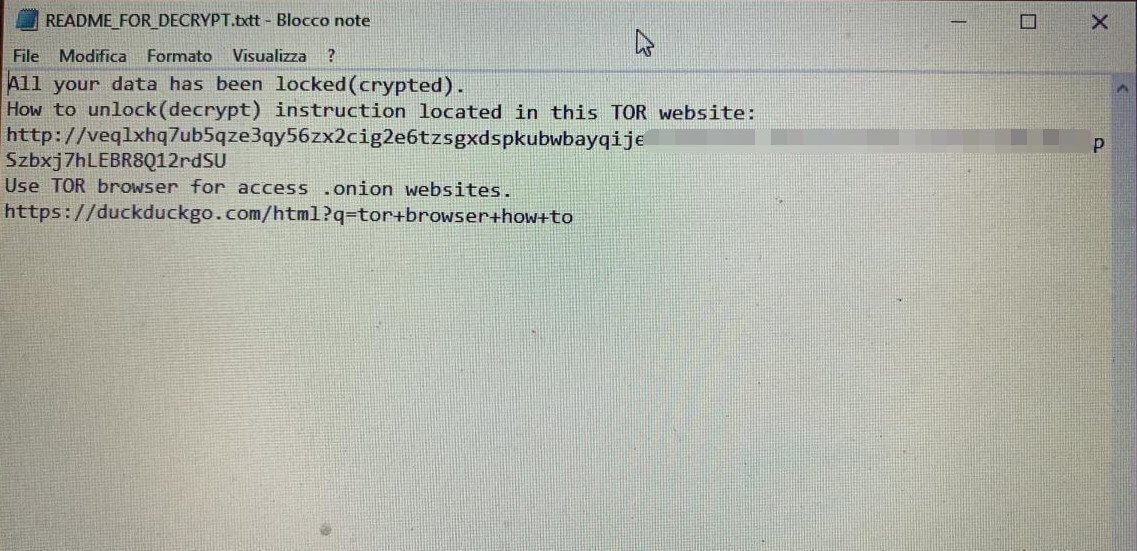
Another particularity of this malicious campaign lies in the fact that the extension related to the ransom note seems to be mistyped, as the “.TXTT” extension was used. This extension does not affect the display of the instructions, however, some users might have to open the ransom note with certain programs like Notepad.
BleepingComputer says that the hackers have required in these recent cyberattacks payments from 024 ($1,200) to .06 bitcoins ($3,000). Since not every user had a backup solution put in place, some had to pay the ransom to have their files back.
Files locked with a version of this ransomware strain before July 17th, 2019 have a free decryptor available, but for the latest versions of eCh0raix (1.0.5 and 1.0.6), there is currently no free decryptor released.
About eCh0raix Ransomware
eCh0raix ransomware has been targeting NAS devices over time and it was first noticed in July 2019, operating as a ransomware-as-a-service model.
In May this year, QNAP published an advisory informing users about this ransomware strain impacting its devices, especially those that ran outdated QTS firmware or had weak passwords.
Then, in August 2021, a new eCh0raix ransomware version was discovered impacting Synology and QNAP devices. This variant abused a vulnerability under the CVE dubbed CVE-2021-28799, using a backdoor account to gain access to hardcoded credentials through brute-force attacks.
Mitigation Measures Provided by QNAP
QNAP has a guideline on its website with general measures for enhancing NAS security. Among these, the company recommends that unknown or suspicious devices or applications should be removed, the auto-router configuration should be disabled, opening default port numbers to the Internet should be avoided, and passwords for all accounts must be changed. Besides, the organization also advises that installed QTS applications should be updated to the latest version. The steps on how to do these actions to keep QNAP devices well safeguarded are provided in the same post.
If you liked this article, follow us on LinkedIn, Twitter, Facebook, Youtube, and Instagram for more cybersecurity news and topics.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security








