Contents:
LinkedIn Smart Link feature is used by threat actors to launch a phishing campaign with the purpose of stealing credit card details from the victims.
Abusing this feature, cybercriminals managed to bypass email security and skillfully divert subscribers to a phishing page.
Smart Link enables business users to send large documents in a single link, also providing analytics about who opened the documents, for how long, etc.
This means that the same attributes can help hackers to optimize their phishing campaign, making it more efficient.
How the Phishing Email Works
The campaign was noticed by Cofense Phishing Defense Center which has discovered false postal service messages aimed at Slovakian users.
The phishing email pretended to be sent by the country’s postal service, Slovenská pošta, announcing to the receiver that there is a remaining shipment cost to pay.
Using email header trickery, the address appears legitimate to the recipient, but if examined closely, it becomes clear that the sender is actually “sis.sk@augenlabs.com”, entirely unrelated to the postal service.
The “confirm” button from this email redirects the user to a phishing page using a LinkedIn Smart Link URL with additional alphanumeric variables at its end.
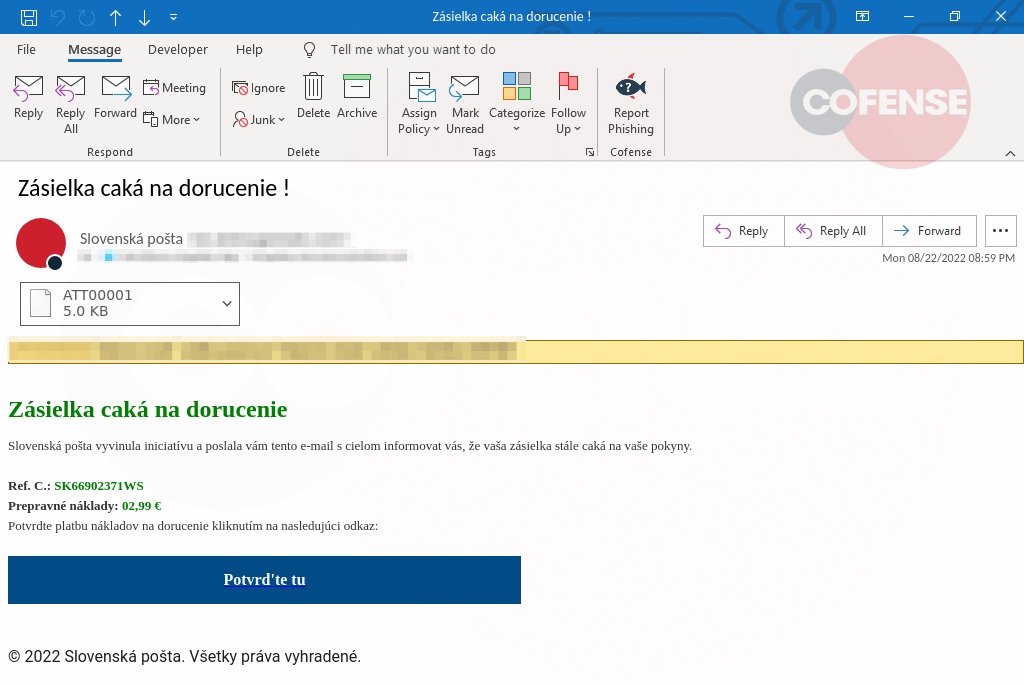
The value of the shipping cost mentioned in the bogus email is €2.99, but the real purpose of this campaign is to steal victim’s credit card details like:
- Card number
- The name of the cardholder
- Expiration date
- CVV
Visitors who enter the information and click on “submit” will be informed that their payment has been received and eventually redirected to a final SMS code confirmation page with the sole purpose of sprinkling legitimacy in the process.
LinkedIn representatives have declared for BleepingComputer that they “work to take action against those who attempt to harm LinkedIn members through phishing.”, and encourage users to protect themselves by adopting basic cybersecurity measures like two-steps authentication and a strong password.
If you liked this article, follow us on LinkedIn, Twitter, Facebook, Youtube, and Instagram for more cybersecurity news and topics.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security