Contents:
As you might already know a new covid variant called Omicron has recently started spreading.
On 26 November 2021, WHO designated the variant B.1.1.529 a variant of concern, named Omicron, on the advice of WHO’s Technical Advisory Group on Virus Evolution (TAG-VE). This decision was based on the evidence presented to the TAG-VE that Omicron has several mutations that may have an impact on how it behaves, for example, on how easily it spreads or the severity of illness it causes. Here is a summary of what is currently known.
The Omicron is concerning because of its high transmissibility and the possible ineffectiveness of current vaccines against its alterations.
What Is Happening?
The appearance of the Omicron COVID-19 variant was rapidly exploited by phishing actors, who now utilize it as bait in their malicious email operations. Malicious actors are fast to adapt to the newest trends and popular issues, and instilling fear in individuals is a fantastic technique to get them to open an email without thinking it through.
As BleepingComputer reports, the consumer protection organization ‘Which?’ in the United Kingdom revealed examples of new phishing emails purporting to be from the National Health Service (NHS) warning about the new Omicron version.
How Does the Scam Work?
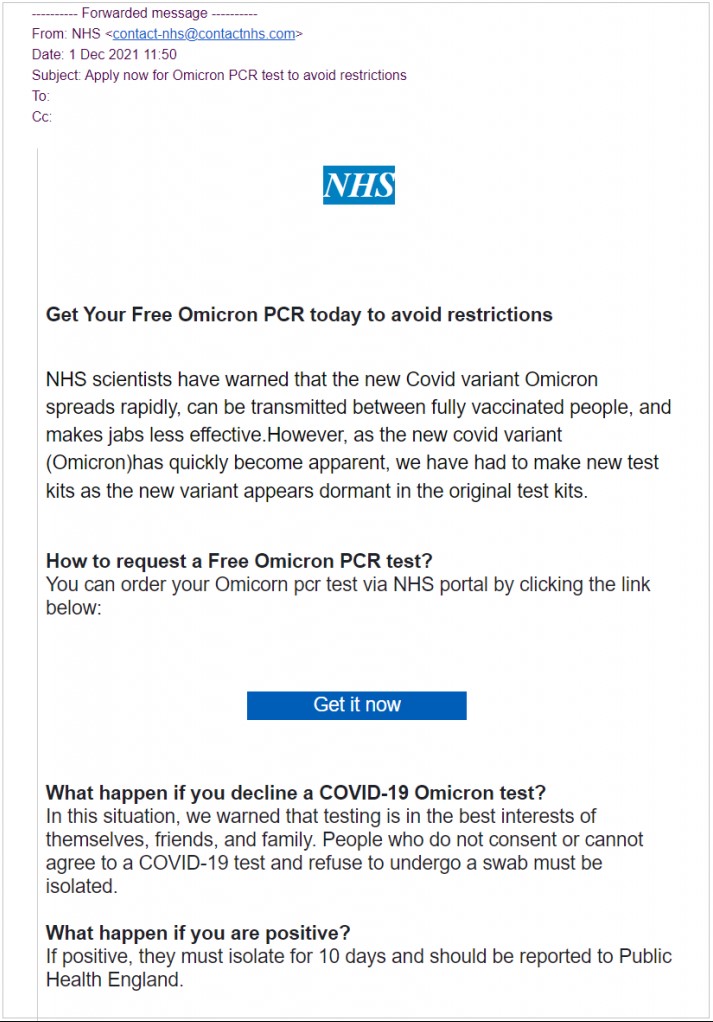
The emails offer recipients a free Omicron PCR test, which they claim will allow them to circumvent limitations.
The emails in question are coming from a malicious address used for distribution is ‘contact-nhs@nhscontact.com.’
If the receiver clicks on the embedded “Get it now” button or taps on the URL in the email body, they are sent to a bogus NHS website that claims to provide the “COVID-19 Omicron PCR test.”
The victims are then asked to give their full name, birth date, home address, mobile phone number, and email address.
Finally, they are asked to pay £1.24 ($1.65), which is meant to cover the cost of the test findings’ delivery.
The goal is not to steal the money itself, but rather the victim’s payment information, such as their e-banking passwords or credit card information.
How Can Heimdal™ Help You?
HeimdalTM Security has developed two email security software aimed against both simple and sophisticated email threats: Heimdal™ Email Security, which detects and blocks malware, spam emails, malicious URLs, and phishing attacks and Heimdal™ Email Fraud Prevention, a revolutionary email protection system against employee impersonation, fraud attempts – and BEC, in general.
For example, you may want to consider HeimdalTM Security’s Heimdal™ Email Fraud Prevention, the ultimate email protection against financial email fraud, C-level executive impersonation, phishing, insider threat attacks, and complex email malware. How does it work? By using over 125 vectors of analysis and being fully supported by threat intelligence, it detects phraseology changes, performs IBAN/Account number scanning, identifies modified attachments, malicious links, and Man-in-the-Email attacks. Furthermore, it integrates with O365 and any mail filtering solutions and includes live monitoring and alerting 24/7 by our specialists.
As Heimdal™ is always updated and keeps pace with the latest cybersecurity trends, you’ll be protected from this type of threat.
Our awarded Threat Prevention Endpoint solution uses Machine Learning, cybercrime intelligence, and artificial intelligence capabilities to help you prevent future threats with 96 % accuracy on your endpoints, a very efficient threat hunting solution that makes malicious URLs, processes, and attacker’s origins no longer anonymous.
If you liked this article, follow us on LinkedIn, Twitter, Facebook, Youtube, and Instagram for more cybersecurity news and topics.


 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management
 Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security