Contents:
Last month, security specialists found adware and info-stealing malware on the Google Play Store, with at least five threats still obtainable and with more than 2 million downloads.
Adware infections showing unsolicited ads degrade the user experience, use up the battery, generate heat, and can even lead to fraudulent transactions.
This software typically attempts to blend in by posing as something different on the host machine, and the way it earns money for its developers is by forcing the target to view or click on affiliated advertisements.
Information-stealing trojans, on the other hand, are far more malicious, snatching login information for other websites you visit, such as social media and online banking accounts.
Getting into the Google Play Store
According to security experts at software company Dr. Web, adware applications and information-stealing Trojans were one of the most prevalent threats affecting Android in May 2022.
The stars of their report are spyware apps that can gather data from other apps’ notifications with the goal of stealing one-time 2FA passcodes (OTP) and gaining access to accounts.
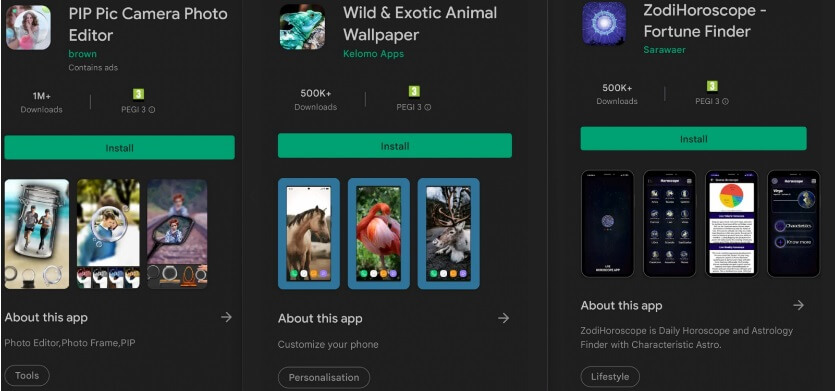
Among the numerous threats that found their way into the Google Play Store, the ones below are still available:
PIP Pic Camera Photo Editor – 1 million downloads, malware disguised as an image-editing application that steals users’ Facebook login credentials.
Wild & Exotic Animal Wallpaper – 500,000 downloads, an adware trojan that changes its icon and title to “SIM Tool Kit” and adds itself to the list of battery-saving exceptions.
ZodiHoroscope – Fortune Finder – 500,000 downloads, malware that steals Facebook login information by deceiving users into entering them, allegedly to remove in-app advertisements.
PIP Camera 2022 – 50,000 downloads, camera effects app that also acts as a Facebook account hijacker.
Magnifier Flashlight – 10,000 downloads, adware app that serves videos and static banner ads.
According to recent user reviews, these apps continue to display malicious behavior and fail to deliver on their feature promises.
Other applications discovered by Dr. Web’s antivirus team on the Play Store in May 2022 include:
- a racing game,
- a deleted image recovery tool,
- a phony state compensation app aimed at Russian users,
- a “free access” app for the Only Fans platform.
Although these apps have been eliminated from the Play Store, users who have them installed on their devices should uninstall them and run a full antivirus scan to remove any remains of the malware.
Hydra Malware, Also Found on Google Play Store
The Hydra malware, which was recently noticed targeting banking customers in Europe, has also been discovered on the Google Play Store, according to researchers at threat intelligence company Cyble.
The banking trojan, which pretended to be a PDF document manager with text-to-PDF and QR code scanning capabilities, received 10,000 downloads.
According to BleepingComputer, the malicious app was available on the Play Store until June 9, 2022, but Google has since removed it. Nevertheless, third-party stores like APKAIO.com and APKCombo.com still have the same PDF app, so be extremely careful.
If you liked this article, follow us on LinkedIn, Twitter, Facebook, Youtube, and Instagram for more cybersecurity news and topics.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security








