Contents:
Chaos ransomware is an in-development ransomware builder that is being advertised as the latest iteration of Ryuk on underground hacker forums.
Fake Minecraft alt lists published on gaming forums are used by the ransomware gang to encrypt gamers’ Windows devices.’
What Happened?
Minecraft is a wildly popular sandbox video game that is presently played by over 140 million people and is a top-selling title in Japan, according to Nintendo sales figures.
It seems that a newly discovered form of the Chaos ransomware is now being disseminated in Japan, encrypting Minecraft users’ data and dropping ransom letters.
Threat actors utilize ‘alt list’ text files that seemingly include stolen Minecraft account credentials, but are really Chaos ransomware executables.
What Are Alt Lists?
Minecraft users who seek to troll or annoy other players without risking their accounts being banned may occasionally search ‘alt’ lists for stolen accounts to use for bannable actions.
Alt lists are constantly in demand due to their popularity, and they are frequently given for free or through automated account generators that provide the community with “spare” accounts.
Phishing attacks are frequently used to breach accounts. Users enter in their account information on websites claiming to be Mojang.
These lists may be found on numerous pastebin sites all over the internet. Account duplication checks are essential since many people just duplicate such accounts and post them to the site.
.png)
Databases are convenient for users since accounts are tested to determine if they are functional or not, making it easy for alternative users to obtain accounts.
As thoroughly explained by BleepingComputer, when the Chaos ransomware encrypts a victim’s files, it adds four arbitrary characters or numbers as an extension.
The ransomware will also drop a ransom message called ‘ReadMe.txt,’ which demands 2,000 yen ($17.56) in pre-paid cards from the threat actors.
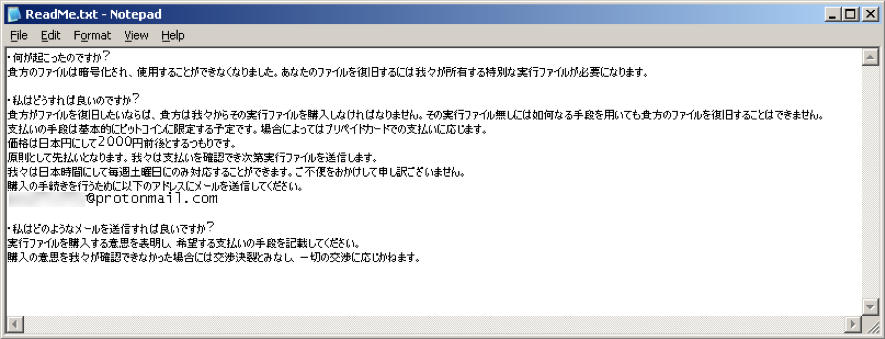
This particular variant of the Chaos Ransomware is set up to look for and encrypt files that are less than 2B onto compromised systems.
If the file is greater than 2MB, however, it will insert random bytes into it, rendering it unrecoverable even if a ransom is paid.

Those who pay the ransom may only restore smaller files due to the attack’s damaging nature. The reason for this capability is unknown, however, it might be due to faulty coding, wrong setting, or a deliberate attempt to harm players’ data.
If you liked this article, follow us on LinkedIn, Twitter, YouTube, Facebook, and Instagram to keep up to date with everything we post.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security