Contents:
Globant is an information technology and software development company with more than 16,000 workers globally and projected sales of $1.2 billion in 2021.
Globant, which was founded in Buenos Aires, Argentina, and now has its headquarters in Luxembourg, has a long list of well-known customers, including the Metropolitan Police, SmileDirectClub, Autodesk, Electronic Arts, Santander, Interbank, Royal Caribbean, and many others. Globant is a global provider of payment solutions.
What Happened?
A 70GB collection of data obtained from Globant, which was described as “some customers’ source code” by the hacker collective was leaked by Lapsus$.
Globant published a press statement after the leak from Lapsus$ stating that parts of the company’s source code had been disclosed to an unauthorized person.
NEW YORK, March 30, 2022 /PRNewswire/ — We have recently detected that a limited section of our company’s code repository has been subject to unauthorized access. We have activated our security protocols and are conducting an exhaustive investigation.
According to our current analysis, the information that was accessed was limited to certain source code and project-related documentation for a very limited number of clients. To date, we have not found any evidence that other areas of our infrastructure systems or those of our clients were affected.
We are taking strict measures to prevent further incidents.
Among the information made available by Lapsus$ is a snapshot of what the organization claims to be an archived directory from Globant, which contains folder names that seem to be those of the company’s clients.
Abbott, apple-health-app, C-span, Fortune, Facebook, DHL, and Arcserve are just a few of the source code folders displayed in the snapshot.
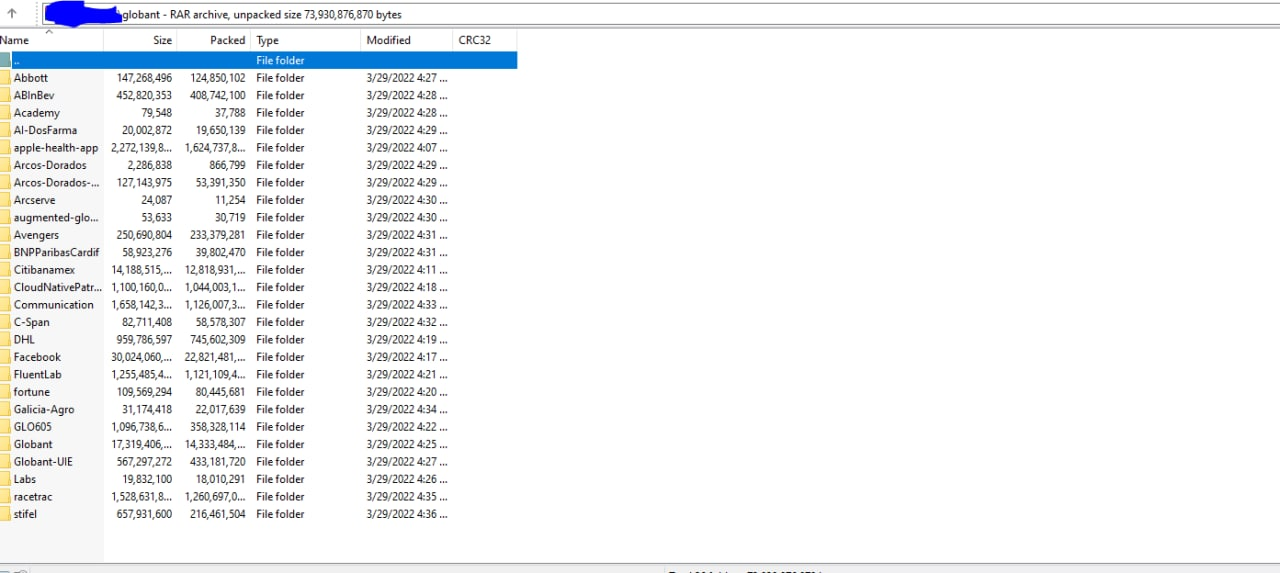
Data theft may have occurred on March 29th, according to the metadata associated with the entries, which might reveal when the information was taken.
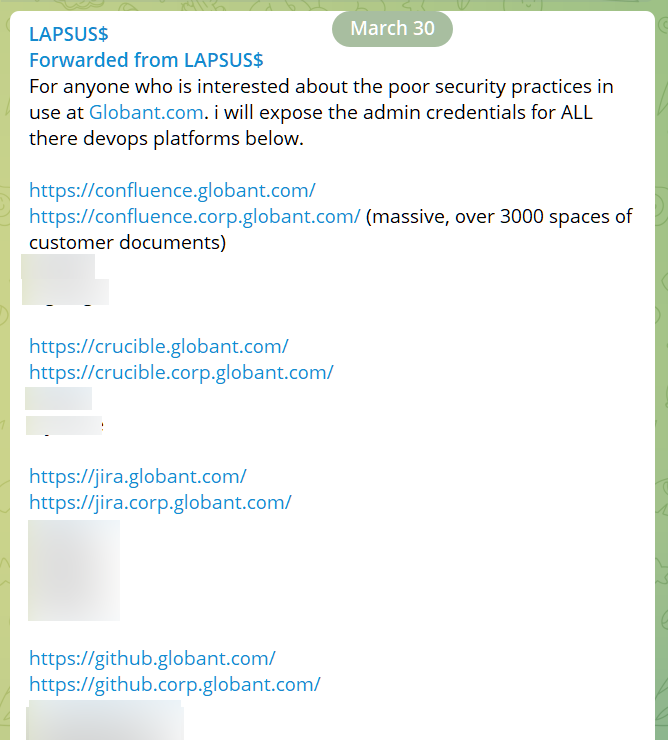
As BleepingComputer explained, Lapsus$ has disclosed a set of credentials that they claim would provide administrators access to multiple platforms used by Globant for development, review, and collaboration on client code (Jira, Confluence, GitHub, Crucible).
The extorsion group has been on the radar of law enforcement for some time, and many people suspected to be related to Lapsus$ have been apprehended in the United Kingdom in recent months.
The FBI is also looking into the actions of the organization and has appealed to the public for any information that may lead to the identification of Lapsus$ members who were engaged in the hack of computer networks belonging to corporations situated in the United States.
The Federal Bureau of Investigation (FBI) is asking the public for assistance in an investigation involving the compromise of computer networks belonging to United States-based technology companies.
On March 21, 2022, individuals from a group identifying themselves as Lapsus$ posted on a social media platform and alleged to have stolen source code from a number of United States-based technology companies. These unidentified individuals took credit for both the theft and dissemination of proprietary data that they claim to have illegally obtained. The FBI is seeking information regarding the identities of the individuals responsible for these cyber intrusions.
On the other hand, it is not known how many active members there are in the organization, or what functions each of them plays.
It is thought that Lapsus$ has affiliates all over the globe, as shown by the fact that some of their Telegram conversations seem to indicate that they speak English, Russian, Turkish, German, and Portuguese.
If you liked this article follow us on LinkedIn, Twitter, YouTube, Facebook, and Instagram to keep up to date with everything cybersecurity.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security