Contents:
Conti ransomware is an extremely damaging malicious actor due to the speed with which it encrypts data and spreads to other systems. To penetrate a victim’s systems Conti ransomware operators will employ a wide variety of tactics.
The hackers will usually begin by trying to persuade an employee to hand out credentials, usually using a social engineering approach.
Sometimes they might also attempt to exploit vulnerable firewalls or attack the internet-facing RDP (Remote Desktop Protocol) servers.
The cyber-crime action is thought to be led by a Russia-based group that goes under the Wizard Spider pseudonym.
What Happened?
The Health Service Executive (“HSE”) is a large geographically spread organisation which provides all of Ireland’s public health services through hospitals and communities across the country. The HSE consists of approximately 4,000 locations, 54 acute hospitals and over 70,000 devices (PCs, laptops, etc). Services are provided through both community delivered care and care provided through the hospital system as well as the national ambulance service. Corporate services and other services that support healthcare delivery are provided through the national centre
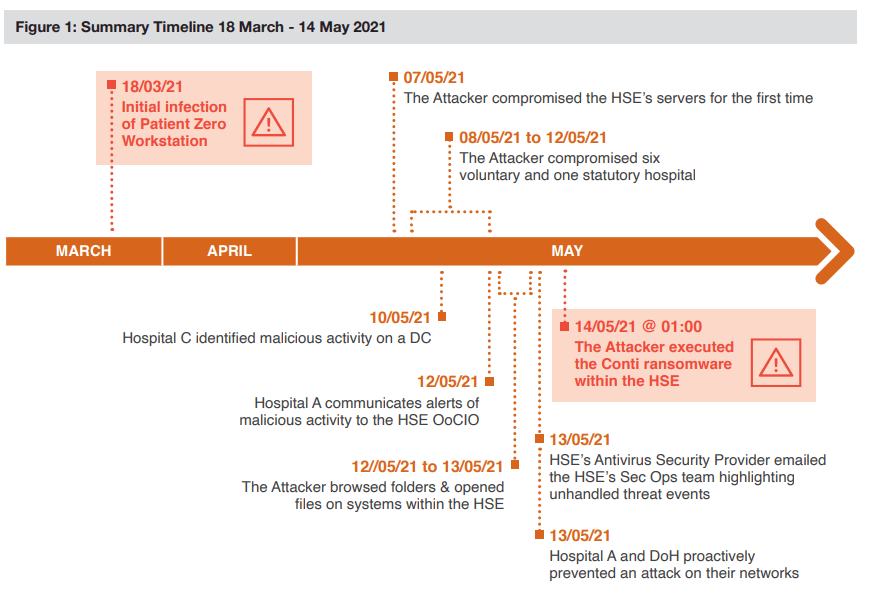
Back in May 2021, Ireland’s Health Service Executive, the country’s publicly funded healthcare system, had to shut down all of its IT systems after suffering a Conti ransomware attack.
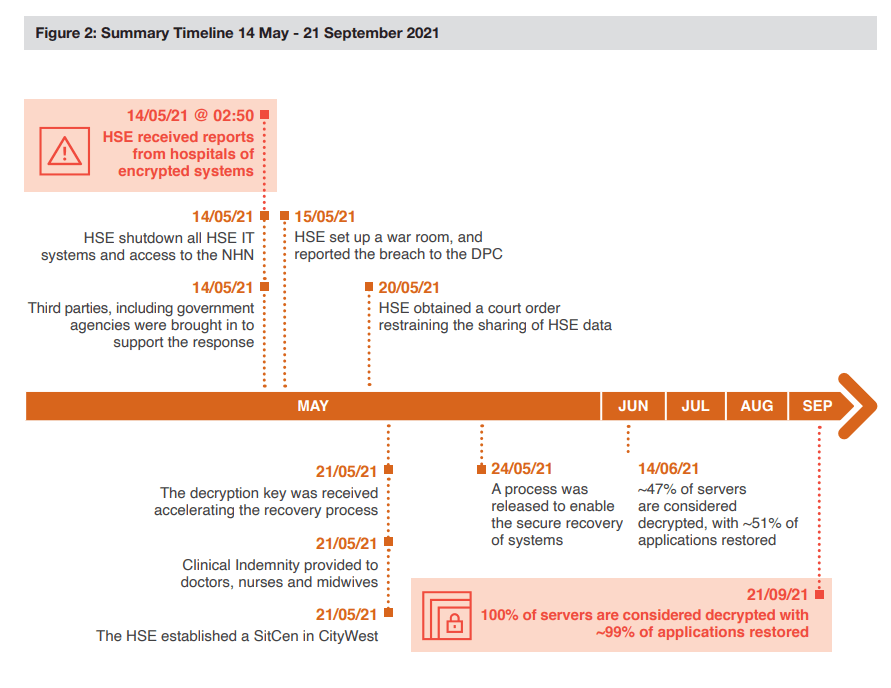
According to ZDNet, the country’s healthcare sector would have to pay more than $48 million to recover after a broad ransomware assault by the Conti gang last year.
Health Service Executive interim chief information officer Fran Thompson stated in a letter obtained by RTÉ that the costs associated with the ransomware attack include $14.2 million for ICT infrastructure, $6.1 million for outside cybersecurity assistance, $17.1 million for vendor support, and $9.4 million for Office 365.
The HSE forecasts that the overall cost could be in the region of €100 million and further to this, the implementation of the recommendations of the PWC report into the Conti will require a separate investment case which is being commissioned by the HSE.
According to RTÉ and the BBC, hundreds of outpatient sessions were canceled, a Covid-19 immunization gateway was stopped, and the government spent weeks attempting to restore its healthcare IT infrastructure.
Irish Foreign Minister Simon Coveney described it as an “extremely severe assault,” while Irish State Minister Ossian Smyth described it as “perhaps the most major cybercrime attack on the Irish State.”
Emergency services continued to function, although many radiological appointments were canceled. There were delays in the reporting of COVID-19 test results, as well as delays in the issuance of birth, death, and marriage certificates. According to The Journal, the assault impacted pediatric services, maternity services, and outpatient visits at select hospitals.
How Can Heimdal™ Help?
In the fight against ransomware, Heimdal™ Security is offering its customers an outstanding integrated cybersecurity suite including the Ransomware Encryption Protection module, that is universally compatible with any antivirus solution, and is 100% signature-free, ensuring superior detection and remediation of any type of ransomware, whether fileless or file-based (including the most recent ones like LockFile).
If you liked this article, follow us on LinkedIn, Twitter, Facebook, Youtube, and Instagram for more cybersecurity news and topics.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security