Contents:
The Tennessee-based company Forward Air has revealed a data breach following a ransomware incident that occurred last year. During the attack, cybercriminals managed to access and steal confidential information belonging to the organization’s employees.
A Quick Look into the Forward Air Ransomware Attack
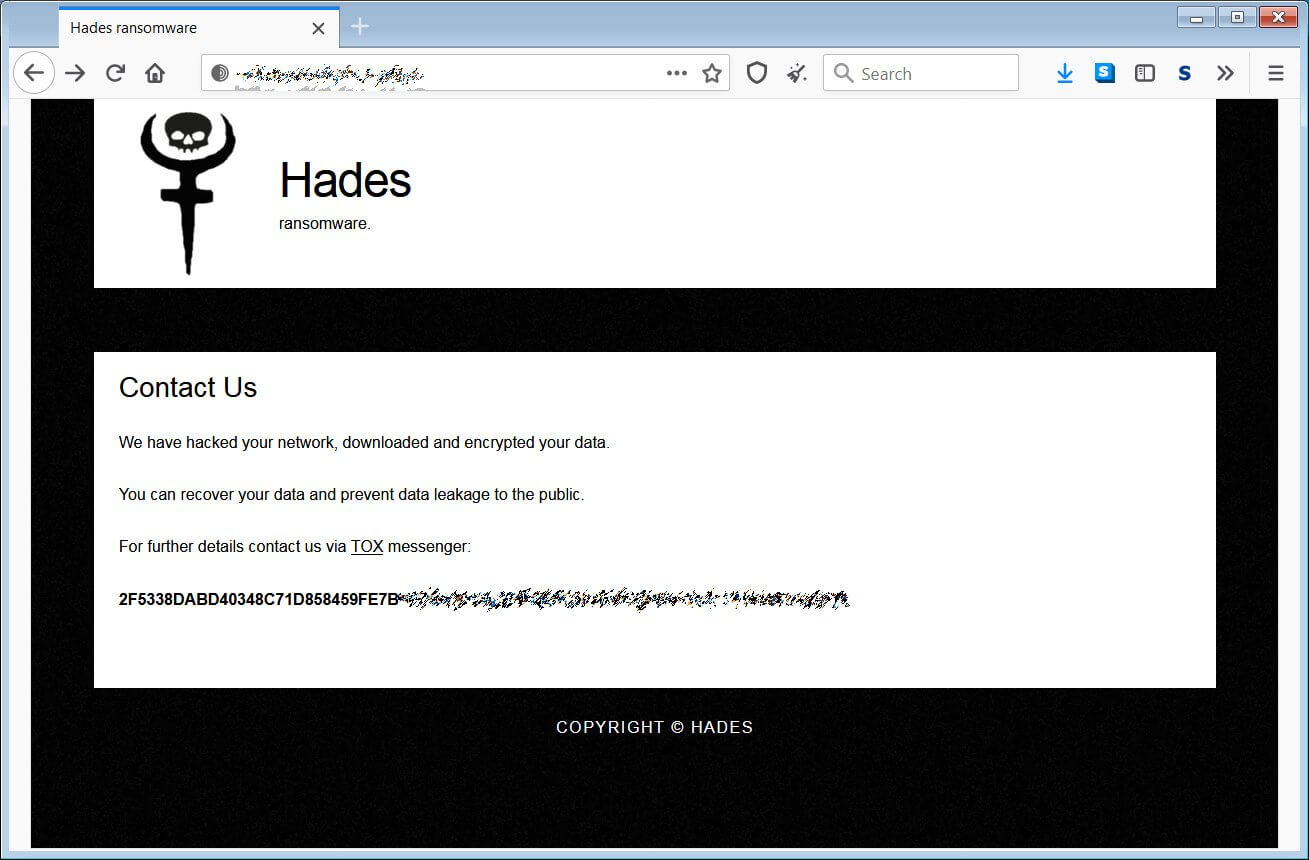
The ransomware attack was made public on December 15th, 2020 and, even though the organization never said anything about the incident, it is believed to have been orchestrated by the Hades ransomware gang.
According to a filling, the attack impacted Forward Air’s operational and information technology systems, forcing it to shut down. As a consequence, the company experienced disruption and was unable to release cargo for transportation.
The same filing says that Forward Air lost an estimated $7.5 million of LTL revenue as a result of the incident “primarily because of the Company’s need to temporarily suspend its electronic data interfaces with its customers”.
According to BleepingComputer, cybersecurity specialists came to the conclusion that the group behind the Forward Air attack was indeed the Evil Corp (aka the Dridex gang or INDRIK SPIDER).
The cybercrime gang conducts attacks under the Hades ransomware name to dodge sanctions applied by the Treasury Department’s Office of Foreign Assets Control (OFAC).
Even though the hackers threatened to leak all of the Forward Air stolen information on a Twitter account specially created for this purpose, this never happened.
A year later, the shipping company reports that sensitive information belonging to its employees has been accessed during the ransomware attack.
The impacted employees received a notification from the company saying:
On December 15, 2020, Forward Air learned of suspicious activity occurring within certain company computer systems. Forward Air immediately launched an investigation to determine the nature and scope of the incident.
The investigation determined that certain Forward Air systems were accessible in November and early December 2020 and that certain data, which may have included your personal information, was potentially viewed or taken by an unknown actor.
What Information Has Been Leaked?
The hackers behind the attack allegedly managed to obtain access to sensitive employee data, including personal (names, addresses, date of births, Social Security numbers, driver’s license numbers, passport numbers) and financial information (bank account numbers).
Recommendations for the Victims
While declaring that there is no proof that the data has been used fraudulently, the organization provides free credit monitoring service protection to the potentially impacted individuals.
All the affected employees are advised to keep an eye on their banking operations and stay alert in case of phishing attacks as no one can guarantee the threat actors won’t use the stolen data in the future.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security








