Contents:
On November 16, 2021, The US Department of Homeland Security’s Cybersecurity and Infrastructure Security Agency (CISA) published the Cybersecurity Incident & Vulnerability Response Playbooks: Operational Procedures for Planning and Conducting Cybersecurity Incident and Vulnerability Response Activities in FCEB Information Systems.
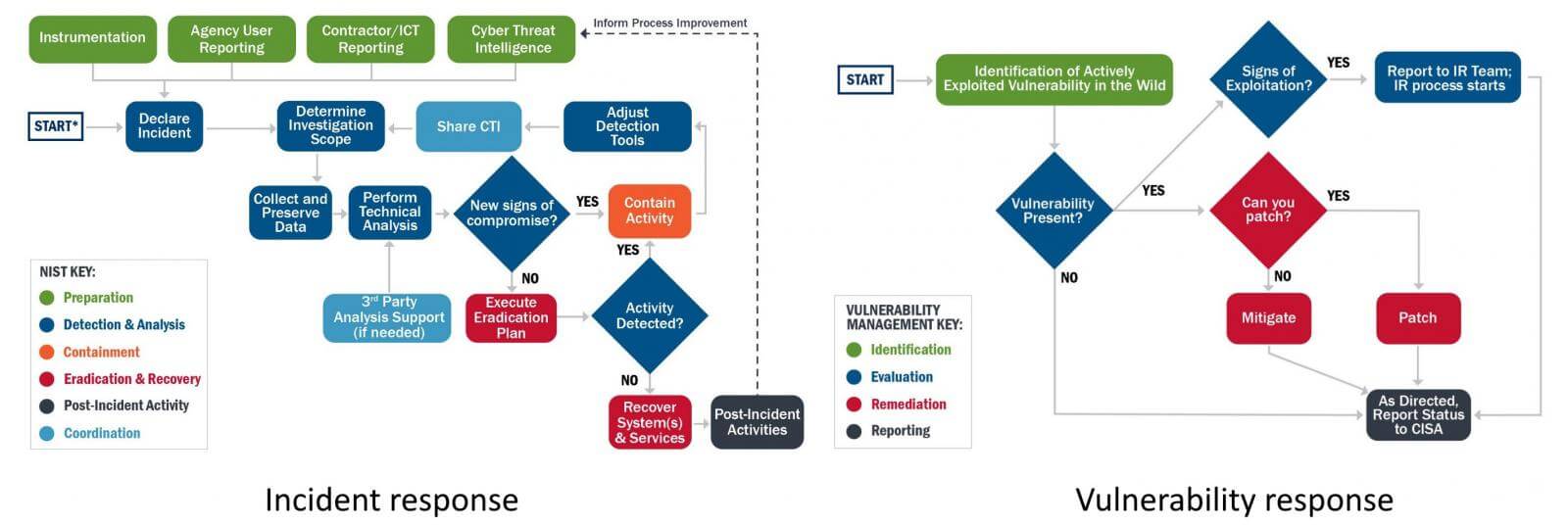
The new guidance is created to help Federal Civilian Executive Branch (FCEB) Information Systems agencies in adopting a standard set of incident and vulnerability response procedures. The playbooks are intended to minimize threats across the federal government, private, and public areas.
These playbooks provide FCEB agencies with a standard set of procedures to identify, coordinate, remediate, recover, and track successful mitigations from incidents and vulnerabilities affecting FCEB systems, data, and networks.
In addition, future iterations of these playbooks may be useful for organizations outside of the FCEB to standardize incident response practices.
The release of the two playbooks set the wheels in motion by President Biden’s Executive Order 14028, “Improving the Nation’s Cybersecurity,” signed on May 12th to streamline the federal government’s cybersecurity defenses against cybercrime.
Biden’s executive order came after a slew of attacks against US public and private sector entities in the previous year, including the SolarWinds supply chain attacks from December.
Source: BleepingComputer
The purpose of the two programs is to help federal agencies and governmental entities keep up with constant threat activities by minimizing their vulnerability to cyberattacks.
While the initiative focuses on government agencies, CISA recommends that public and private sector companies analyze it to improve their incident and vulnerability response strategies.
Matt Hartman, Deputy Executive Assistant Director for Cybersecurity declared:
The playbooks we are releasing today are intended to improve and standardize the approaches used by federal agencies to identify, remediate, and recover from vulnerabilities and incidents affecting their systems.
We encourage our public and private sector partners to review the playbooks to take stock of their own vulnerability and incident response practices.
If you liked this article follow us on LinkedIn, Twitter, YouTube, Facebook, and Instagram to keep up to date with everything cybersecurity.


 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management
 Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security










