Contents:
The software development service CircleCI has disclosed a security incident and urged users to rotate their secrets.
Over one million engineers rely on the CI/CD platform for the “speed and reliability” of their builds, according to its website.
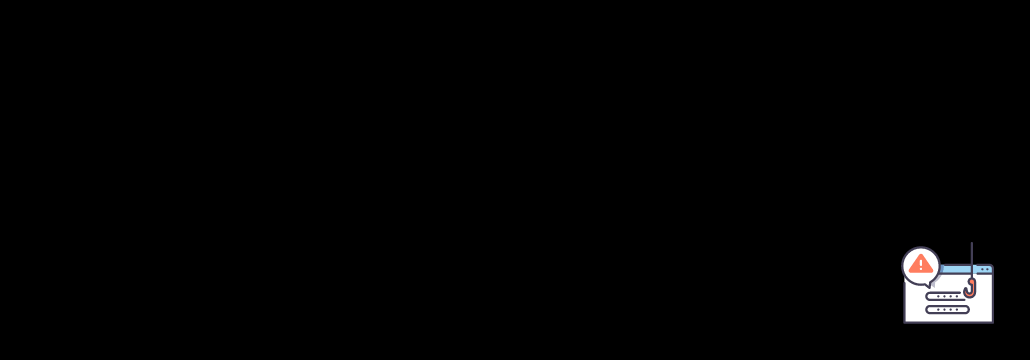
As per email notifications received by CircleCI users, CircleCI is investigating a security incident. Therefore, CircleCI encourages users to rotate any secrets stored there until the company completes its investigation.
In a brief advisory published Wednesday, the CircleCI CTO, Rob Zuber, states:
We will keep you updated as more information becomes available about this incident and our response to it. At this point, we are confident that no unauthorized actors are active in our systems; however, we want you to take specific preventative measures to protect your data.
Customers are advised to rotate secrets stored in project environment variables and contexts.
Moreover, CircleCI has invalidated API tokens for projects using API tokens, and users will need to replace them.
Daniel Hückmann, a security engineer, reported seeing one of the IP addresses associated with the attack (54.145.167.181). This information could potentially assist incident responders.
CircleCI’s ‘Reliability’ Update Follows Breach
The wording suggests CircleCI was breached on December 21st, the same day it published a “reliability update” that reinforced its commitment to improving its service.
CircleCI admitted in April of 2022 that its reliability had not been up to user expectations, which led to said reliability update.
Our mission at CircleCI is to manage change so software teams can innovate faster. But lately, our reliability hasn’t met customer expectations.
CircleCI issued another such update in September 2022, following the unavailability of the pipelines page “for a significant portion of a day.”
Over the past few years, CircleCI has experienced several security problems.
As a result of a third-party vendor compromise in mid-2019, CircleCI suffered a data breach. Moreover, user data such as usernames, passwords, email addresses, IP addresses, organizations, repositories, URLs, and others associated with the users’ GitHub and Bitbucket accounts were compromised.
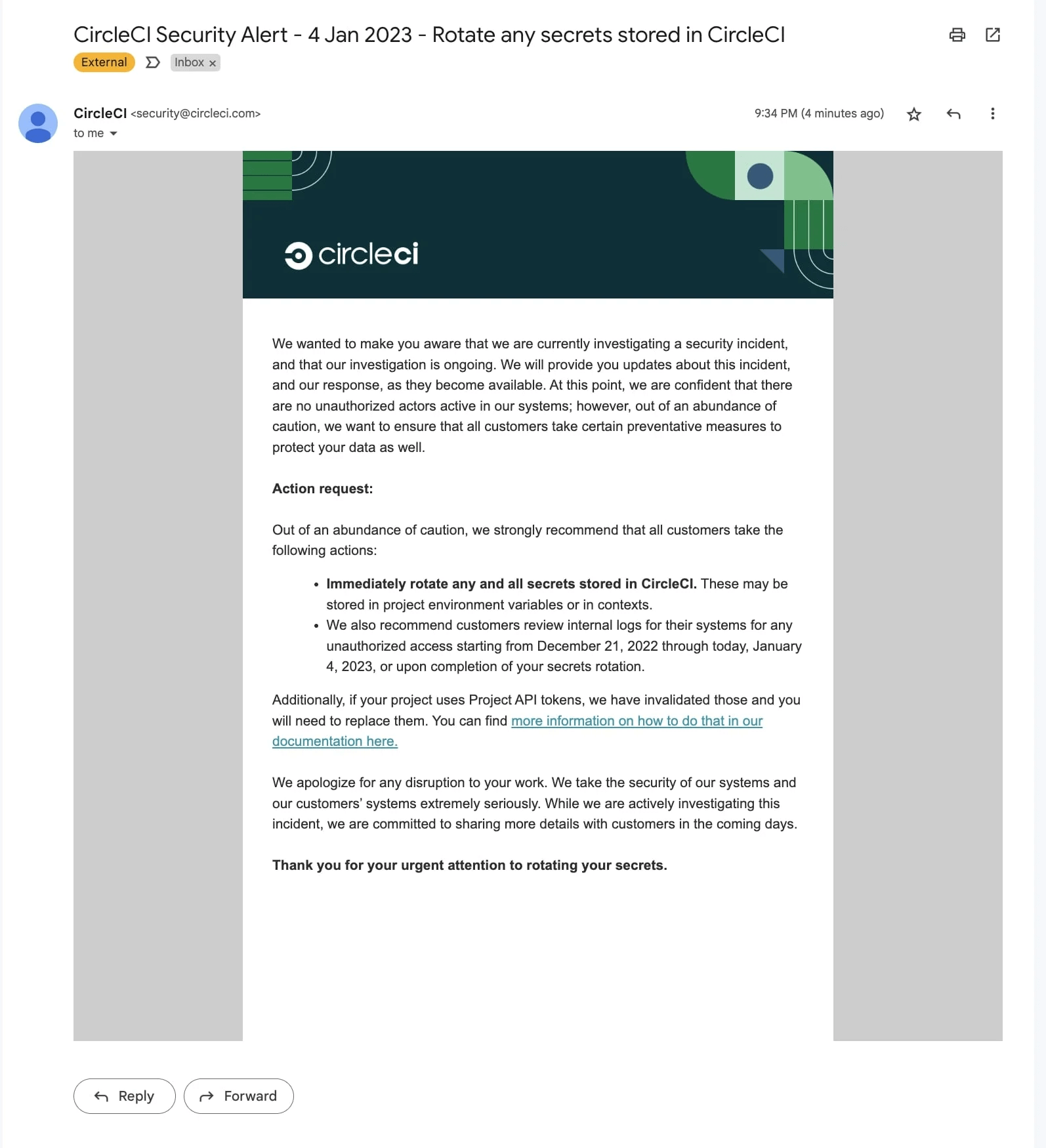
Threat actors stole GitHub accounts in 2022 by sending fake CircleCI email notifications to users:
As CircleCI reassured customers at the time that it remains secure, these phishing attempts were not necessarily the result of a new compromise.
However, threat actors often use phishing attacks to target customers of an affected company using email addresses obtained from earlier breaches (e.g., the 2019 breach).
Regarding Wednesday’s security incident disclosure, CircleCI apologizes for any inconvenience this may have caused. The company plans to share more details once the investigation is complete.
If you liked this article, follow us on LinkedIn, Twitter, Facebook, Youtube, and Instagram for more cybersecurity news and topics.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security