Contents:
OpenSea is a non-fungible token (NFT) marketplace based in New York City, operated by a group of American entrepreneurs, Devin Finzer and Alex Atallah.
On the Ethereum blockchain, OpenSea provides a marketplace that allows non-fungible tokens to be traded directly at a set price or via an auction. The platform is built on the ERC-721 standard and the layer-2 scaling solution for the Ethereum Polygon network.
What Happened?
It seems that the attackers managed to steal hundreds of NFTs from OpenSea users, generating panic among the site’s large user base. During the hack, according to a spreadsheet collected by the blockchain security firm PeckShield, 254 tokens were taken, including tokens from Decentraland and the Bored Ape Yacht Club.
32 users were targeted by the attack, which happened between 5 pm and 8 pm Eastern Time, and according to Molly Whit the author of blog Web3 is Going Great, the stolen tokens were worth more than $1.7 million.
Panic erupted on February 19 as a few users saw their wallets emptied of valuable NFTs without knowing why, and many others feared the same could happen to them. Early explanations blamed a new contract that OpenSea had rolled out, or an airdrop from a new NFT marketplace called X2Y2. People urged NFT owners to revoke permissions for both the OpenSea contract and for X2Y2 until more was known, although one of the most popular websites helping people do so went down shortly after from the high traffic.
An hour and a half after users began to report missing NFTs, OpenSea finally acknowledged the issue. They tweeted that they were “actively investigating rumors of an exploit associated with OpenSea related smart contracts”, and wrote that they believed it was a phishing attack coming from outside of OpenSea, rather than an issue with their contract. It was later determined that an attacker had successfully phished 32 OpenSea users into signing a malicious contract, which allowed the attacker to take the NFTs and then flip them. Bizarrely, the hacker returned some of the NFTs to their original owners, and one victim inexplicably received 50 ETH ($130,000) from the attacker as well as some of his stolen NFTs back. The attacker later transferred 1,115 ETH obtained from the attack to a cryptocurrency tumbler, worth around $2.9 million.
The Wyvern Protocol, which is the open-source standard that underpins most NFT smart contracts, including those created on OpenSea, seems to have been targeted by the assault because of its flexibility.
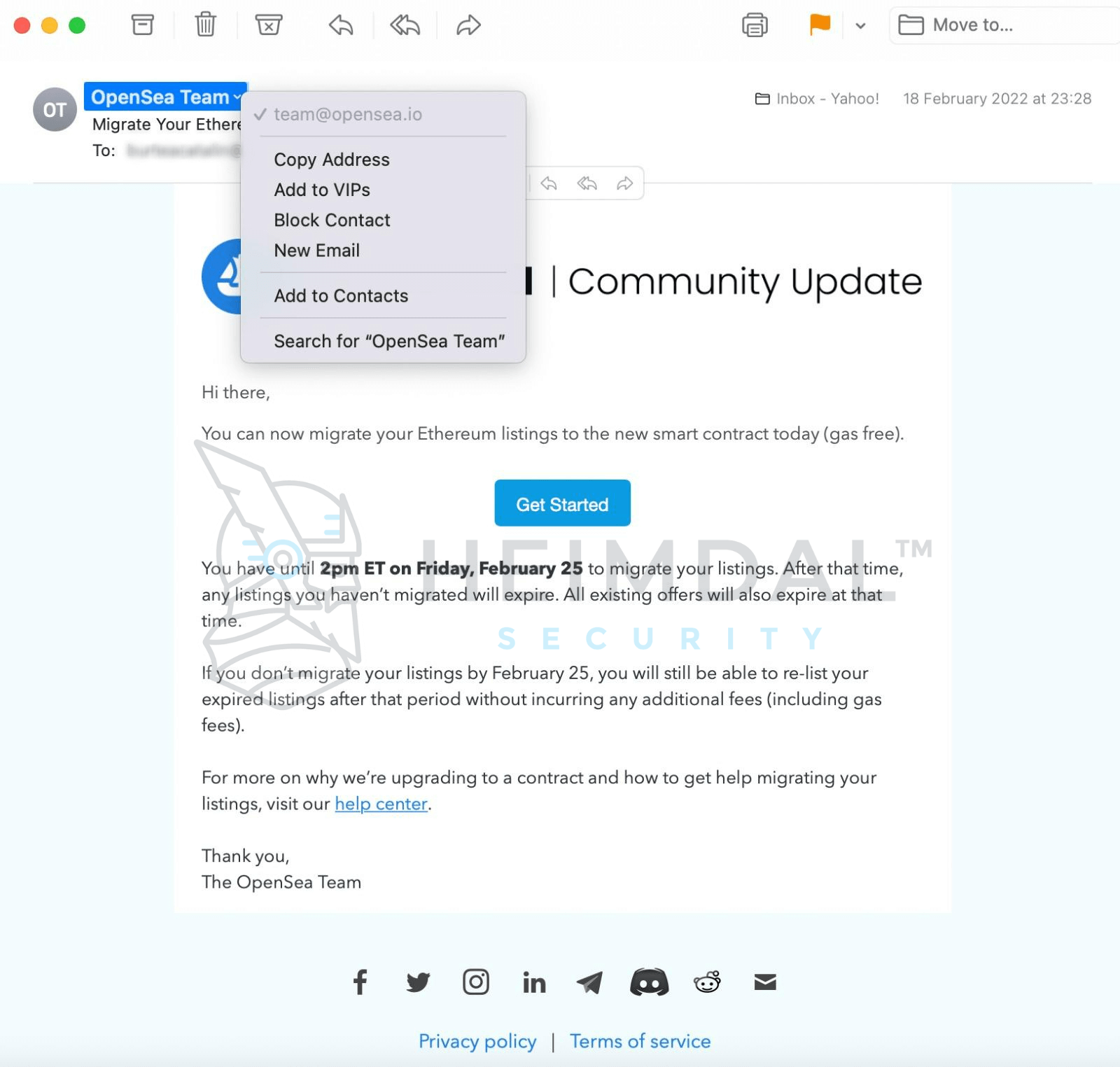
As explained by The Verge, the attack was split into two parts: the first had as a target the signing of a partial contract by using spoofed emails, with a general authorization and large portions left blank.
Having this signature in place, attackers were able to complete the contract with a call to their own contract, which transferred ownership of the NFTs without payment.
A description of the assault was provided on Twitter by CEO Devin Finzer:

Many aspects of the assault remain a mystery at this point, but it seems that this attack couldn’t have come at a worse time for OpenSea, as on Friday, the company introduced a new smart contract, and asked people to migrate their assets.
If you liked this article, follow us on LinkedIn, Twitter, Facebook, Youtube, and Instagram for more cybersecurity news and topics.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security