Contents:
A threat actor claimed to have hacked Taiwanese multinational hardware and electronics business Acer, prompting the company to declare a data breach. The hacker announced the breach on a popular cybercrime forum, claiming to have stolen nearly 3,000 files of sensitive information.
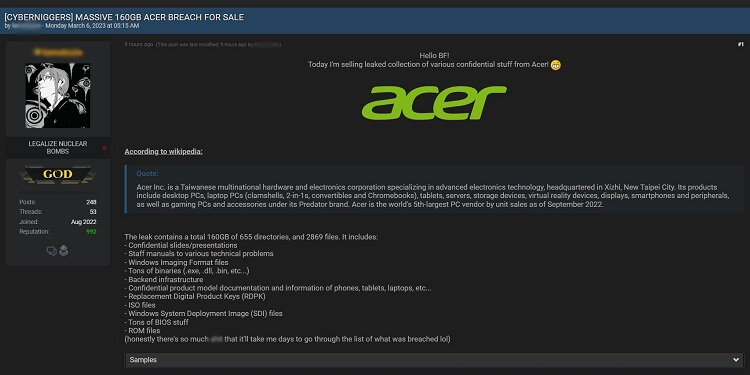
Acer Leak Announcement Spotted on Cybercrime Forum (Source)
What Data Was Stolen?
The leak contains 160GB of data consisting of 655 directories and 2,869 files, and it includes:
- Confidential slides/presentation
- Backend infrastructure
- ISO files
- ROM files
- BIOS information
- Windows Imaging Format files
- Windows System Deployment Image (SDI) files
- Replacement Digital Product Keys (RDPK)
- Staff manuals for various technical problems
- Confidential product model documentation and information on phones, laptops, tablets, etc.
Cybernews reached out to Acer to find more information on the leak. An Acer representative declared the following:
We have recently detected an incident of unauthorized access to one of our document servers for repair technicians. While our investigation is ongoing, there is currently no indication that any consumer data was stored on that server,
Acer representative on the leak (Source)
The seller is a respected user on the forum that only accepts payments in the cryptocurrency Monero and will only conduct escrow sales. The threat actor behind the post claims that the leak dates to February 2023. If confirmed, the post would point to a breach separate from the one Acer had in 2021, when REvil ransomware attacked the company and demanded $50 million in ransom.
Acer is one of the largest hardware and electronics companies in the world. Based in Taiwan, it employs over 7,800 people. In 2021, Acer’s reported revenue was over NT$10 billion.
If you liked this article, follow us on LinkedIn, Twitter, Facebook, and Youtube, for more cybersecurity news and topics.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security