Contents:
Update: Microsoft confirmed the fact that one of their employee’s accounts was compromised by Lapsus$, also known as DEV-0537, and in this way, the attackers managed to access the source code repositories.
No customer code or data was involved in the observed activities. Our investigation has found a single account had been compromised, granting limited access. Our cybersecurity response teams quickly engaged to remediate the compromised account and prevent further activity.
Microsoft does not rely on the secrecy of code as a security measure and viewing source code does not lead to elevation of risk. The tactics DEV-0537 used in this intrusion reflect the tactics and techniques discussed in this blog.
Our team was already investigating the compromised account based on threat intelligence when the actor publicly disclosed their intrusion. This public disclosure escalated our action allowing our team to intervene and interrupt the actor mid-operation, limiting broader impact.
Lapsus$, a cyber extortion gang that had previously targeted Nvidia, and Samsung claimed to recently have made a new victim.
In order to steal source code, customer lists, databases, and other important information, Lapsus$ hacks into business systems and compromises their systems. They then try to extort the victim by making ransom demands, otherwise threatening that the information would be made public.
What Happened?
On their Telegram channel, the Lapsus$ gang shared a snapshot of a hacked Microsoft Azure DevOps Server, which contained source code for Bing, Cortana, and various other internal projects, as well as other information.
A torrent for a 9 GB 7zip archive condensing the source code of over 250 projects, which the hacker gang claims are owned by Microsoft, was shared by the group late Monday night.
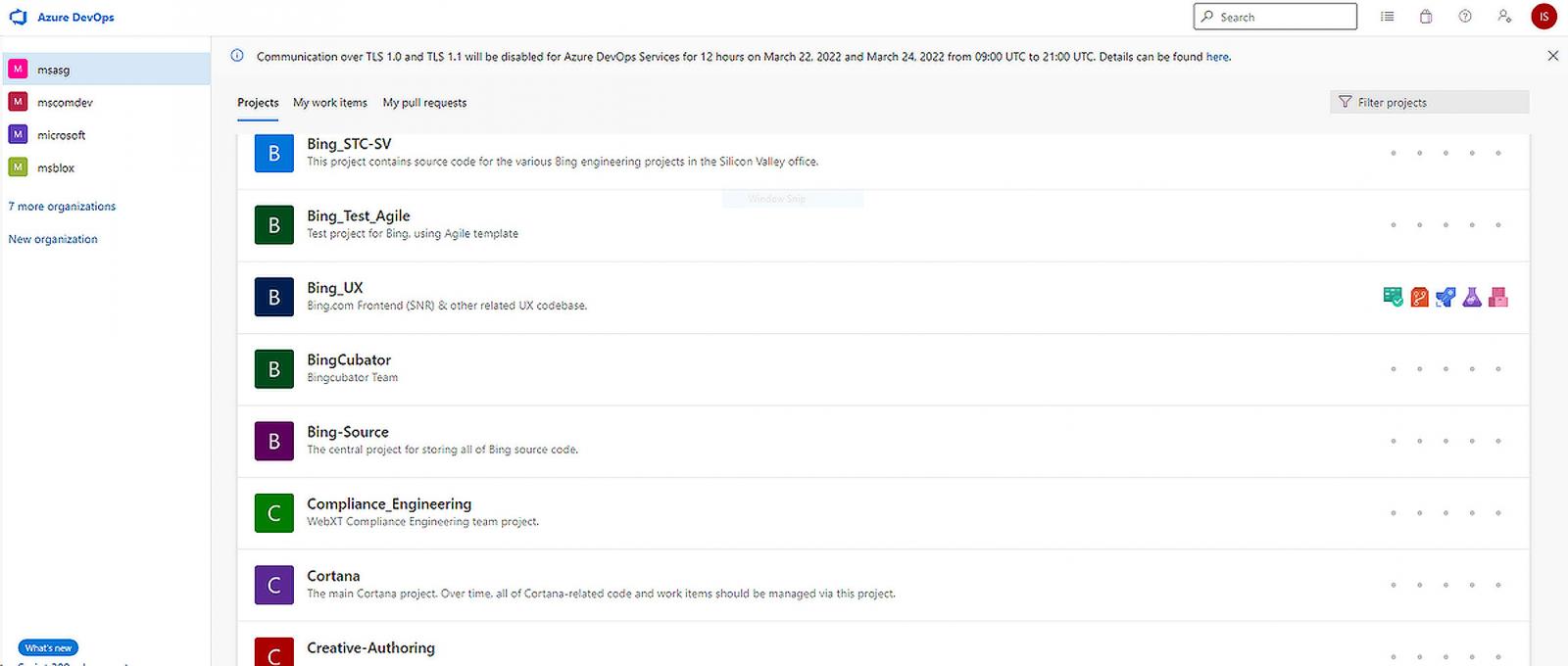
When Lapsus$ posted the torrent, it was communicated that it included 90 percent of the source code for Bing and around 45 percent of the source code for Bing Maps and Cortana, among other things.
As BleepingComputer reports, the uncompressed download has roughly 37GB of source code that, reportedly, belongs to Microsoft, despite the fact that they claim that a portion of the source code was leaked.
The projects seem to be used for web-based infrastructure, websites, or mobile applications, with no source code for Microsoft desktop software, such as Windows, Windows Server, or Microsoft Office, being made available for public consumption.
At this time, it remains unclear how the threat actors are infiltrating these repositories, but some security experts assume that they are bribing company insiders to get access to these databases.
The extortion gang takes advantage of their very busy Telegram channels to announce fresh leaks, assaults, and to communicate with their supporters, and they seem to be enjoying their increased popularity.
If you liked this article, follow us on LinkedIn, Twitter, Facebook, Youtube, and Instagram for more cybersecurity news and topics.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security