Contents:
After a popular hacker advertised data from over 700 million LinkedIn users for sale last month, it was revealed that the vast amount of stolen information is being put together and filtered to identify specific targets.
The Threat Post reporter Becky Bracken believes this is probably the beginning of a series of LinkedIn-fueled attacks.
As reported by my colleague Antonia last week, it is still uncertain what the origin of the data is but it is believed that the scraping of public profiles might be the starting point. That was also the generator behind the collection of 500 million LinkedIn data records that were advertised for sale in April 2021.
LinkedIn stated that it contained an aggregation of information from several sites and organizations as well as publicly viewable member profile details. The platform stated that no breach of its networks has occurred this time, either.
In total, there are around 1.2 billion personal and professional records waiting to be turned against users in future phishing, ransomware, display-name spoofing, or other attacks.
A few days ago, a database containing the personal information of 88,000 U.S. business owners gleaned from the latest LinkedIn breach was shared on RaidForum. The database includes full names, email addresses, work details, as well as other information publicly listed on LinkedIn.
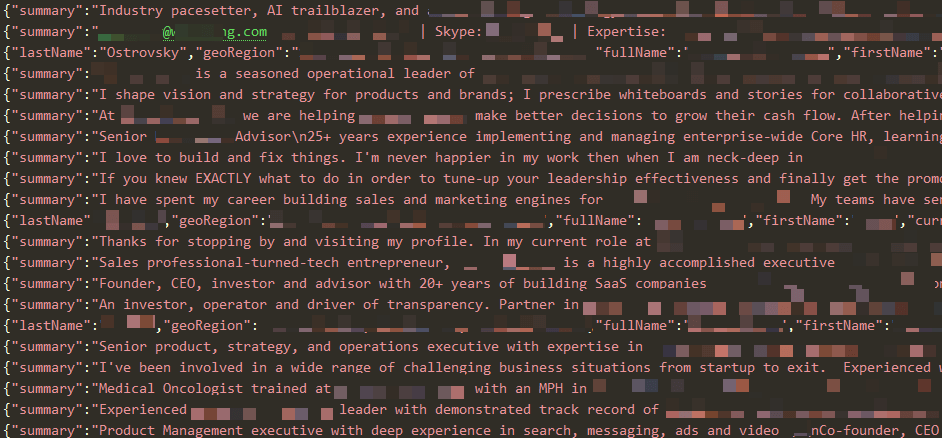
Image Source: CyberNews
LinkedIn: This Is Not A Data Breach
The company confirms the abuse of LinkedIn data but says that the incident is not technically a breach since the information was public.
In an update on the report of scraped data, LinkedIn stated:
Our teams have investigated a set of alleged LinkedIn data that has been posted for sale. We want to be clear that this is not a data breach and no private LinkedIn member data was exposed. Our initial investigation has found that this data was scraped from LinkedIn and other various websites and includes the same data reported earlier this year in our April 2021 scraping update.
LinkedIn isn’t alone. In April, a user from a low-level hacking forum published the phone numbers and personal data of hundreds of millions of Facebook users for free. The data that was leaked includes personal information belonging to over 533 million Facebook users from 106 countries, such as phone numbers, Facebook IDs, full names, locations, birthdates, bios, and email addresses.
However, LinkedIn’s public data is more valuable to threat actors, since the business intelligence can be drawn from users’ LinkedIn profiles.
What Is Data Scraping?
According to Technopedia,
Data scraping is commonly defined as a system where a technology extracts data from a particular codebase or program. Data scraping provides results for a variety of uses and automates aspects of data aggregation.
However, when used by cybercriminals, data scraping can allow threat actors to use this data to spearhead further cyberattacks and can give hackers the ability to perpetrate very effective spear-phishing attacks.
The data gathered from data scraping can help attackers collect vast amounts of information on how a business operates and how they can exploit it.
Members trust LinkedIn with their data, and any misuse of our members’ data, such as scraping, violates LinkedIn terms of service. When anyone tries to take member data and use it for purposes LinkedIn and our members haven’t agreed to, we work to stop them and hold them accountable.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security








