Contents:
Phishing is a type of social engineering where an attacker sends a spoofed message created to trick his victim into revealing private data.
Sent via SMS, social media platforms, or email these messages can trick you into believing they are from a trusted company although most of the time they contain malicious attachments intended to spread malware.
Vishing, short for voice phishing, is a subset of phishing procedures that combines ‘voice’ and ‘phishing’.
In a vishing attack, the scammer still impersonates someone from a trusted organization (your bank or popular online services) but uses a phone call as a weapon in order to steal your personal information.
In some situations, the fraudsters call or leave a voicemail message for the victim. In others, the attacker sends an email with a contact phone number advising the recipient to call that number.
Scammers can send thousands of phishing emails out, hoping that someone will fall for it in operations and blast out thousands of emails all at once, and now, voice over internet protocol (VoIP) technology has enabled fraudsters to do the same, all while spoofing their caller IDs and identities.
In a report published Thursday, a cybersecurity company analyzed two recent vishing campaigns that spoofed Amazon intending to steal customer credit card details.
The first example vishing endeavor tracked to approximately 9,000 email inboxes, was sent from a Gmail account and contained the subject line: “Invoice:ID,” followed by an invoice number and content containing color markers used by Amazon.
This email says that the victim just bought a TV and gaming console that cost a few hundred dollars and recommends the receiver to contact them using a phone number if any mistakes were made.
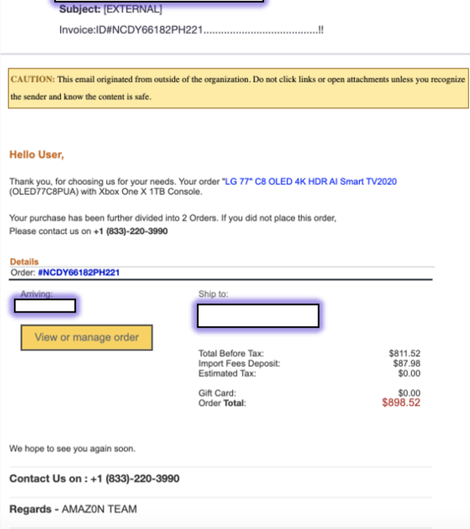
When the cybersecurity company called the number, someone answered impersonating an Amazon customer service agent. The caller was asked to provide the customer’s name and credit card details before ending the call and blocking the number.
According to the researchers, the use of a zero in “AMAZ0N TEAM” helped the message avoid existing spam filters, including Microsoft Exchange Online Protection (EOP) and Microsoft Defender for Office 365 (MSDO). A spam level of “1” was allocated to the email, which means that the message was not considered bogus.
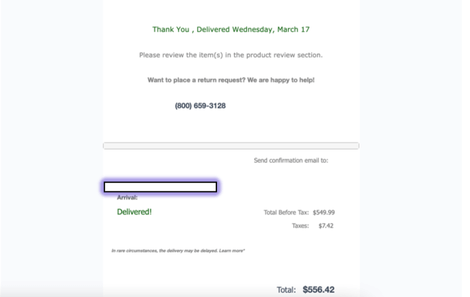
In the second situation, which reached roughly 4,000 inboxes and was also able to circumvent EOP and MSDO, attackers pretended to be Amazon via a spoofed email address — “no-reply@amzeinfo[.]com” — and used the subject line, “A shipment with goods is being delivered.”
In this case, the researchers discovered that the scam seemed to have been stopped as the phone number wasn’t available for use.
In these situations, the alleged loss of money used to scare the victims and the Amazon impersonation were combined in order to persuade victims into calling the scammers. Worst-case scenario, the victims could end up being tricked into giving their personal and financial information to fraudsters, leading to identity theft or fraudulent payments made on their behalf.
Due to our need to keep shopping online as we remain at home because of the pandemic, scammers will not stop trying to find new ways to trick us into stealing our private information.
In August, the FBI and US Cybersecurity and Infrastructure Security Agency (CISA) issued a joint advisory warning of an increase in vishing attacks against the private sector.

Heimdal® Email Security
- Completely secure your infrastructure against email-delivered threats;
- Deep content scanning for malicious attachments and links;
- Block Phishing and man-in-the-email attacks;
- Complete email-based reporting for compliance & auditing requirements;










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security








