Contents:
Cryptocurrency is not exactly a newfangled contraction; the idea of a decentralized digital asset was coined in the late ‘80s by David Chaum, the American cryptographer whose works ignited the computer science revolution that gave birth to Bitcoin, Blockchain, Altcoin, and a whole new way of looking at monetary transactions.
But cryptocurrency fraud is one of the looming dangers of this new digital opportunity.
Scammers often exploit crypto assets through various fraudulent schemes, such as high yield investment programs and phishing scams. Fortunately, crypto recovery firms play a crucial role in assisting individuals who have lost their crypto assets to such illicit activities. Here’s how you can make sure you don’t fall for it.
The Birth of Bitcoin
Ecash, the first form of cryptocurrency and Chaum’s brainchild, was launched in 1983 as an alternative to paper money. Digicash, the company regulating this novel ‘non-corporeal’ monetary asset, managed to raise over $10 million in a span of a decade.
The concept was sound and the idea of getting rid of traditional money appealed to the general public. And in 2009, a group called Satoshi Nakamoto launched Bitcoin, which was unanimously considered the first (and true) decentralized digital currency.
With the advent of a new era of non-bank-dependent digital currency, numerous Bitcoin alternatives were seeded on the market. Altcoins they’re called and, at the moment, there are over 4,000 of them in use.
Living the dream, right? Well, not my intention of casting a dark cloud over this brave new world, but wherever money’s involved, there’s bound to be someone trying to bamboozle a goose.
Cryptocurrency fraud, the subject du jour, has gained quite a foothold, with hundreds of thousands of people being swindled every day. Not exactly breaking news, but the ploys have become so intricate, that it’s increasingly difficult to tell apart the fake from the legit one.
Hence this little handy hand-guide will tell you all about the wondrous world of crypto scams and how to avoid them. Let’s start with a rundown of the most (un)common scams.

Cryptocurrency scams
As a rule of thumb, to prevent falling victim to scams, you should never accept crypto-trading with companies or startups that are not blockchain-powered. In layman’s terms, that means that all transaction data can be tracked and reviewed.
Furthermore, before committing to a company or another, you may want to review their credentials – look for status quo indicators such as adherence to initial coin offerings rules and digital currency liquidity.
That’s about it at a glance. Up next, we’re going to dive into the most common and uncommon cryptocurrency scams. Enjoy (or not).
Fake ICOs (initial coin offerings)
How do they do that, you ask? By promising astronomical gains in the span of a couple of weeks. For instance, by spinning the fake crypto coin’s white paper (that would be the project’s documentation I was telling you about), the fraudster will attempt to lure in investors by promising them astronomical gains (100x or even 1,000x) in a short amount of time – try a couple of weeks or even days.
These scammers exploit the promise of financial gain to attract victims, ultimately seeking to benefit themselves by stealing from their victims.
Fake ICOs count as some of the most common types of cryptocurrency scams. Unfortunately, over the past couple of years, the scales kind of tipped in the ‘favor’ of the fake one.
In fact, according to a Bloomberg study, over 80 percent of ICOs are fraudulent, with less than 8 percent reaching out. Yes, they can be avoided, but we will talk more about that in the third part of this article.
‘Overnight’ exchanges
Another cryptocurrency scam is the so-called shady or overnight exchange. How does that work, you ask? Let’s assume for a moment that you want to exchange your digital token for a better-performing crypto coin.
One would naturally assume that this is what every crypto coin possessor should aim for if he (or she) is looking to increase gains. The best way to go about this would be to exchange your coin with another that outperforms it.
Still, before you go full wolf of Wall Street on this one, consider choosing a legit and regulated cryptocurrency broker or exchange system. Why? Because you would risk losing your entire portfolio by tying them in a venture that simply sounds too good to be true.
Shady exchanges tend to follow a similar pattern – boy has crypto-money, boy finds better price, boy makes deposit coaxed by shady deal-man, boy asks about how the deal’s performing.
Teary-eyed deal-man says that he couldn’t upscale the business, the price dropped, and that the coins are worth zilch. The dénouement – the shady dealer gets your coins and you end up with a dent in your wallet.
Fraudulent wallets
There’s nothing wrong in picking up an app to manage your cryptocurrency portfolio – plenty to choose from and, speaking on behalf of the vast majority, they’re great-look and easy to use.
Yes, I know that you know that there’s a big “but” around the bend, but it is an article on cryptocurrency fraud. Lately, a great deal of fraudulent wallets has been discovered on Google’s Play Store.
Though Google is making efforts to root these posers, their efforts are hindered by malicious developers which seed them by the hundreds. Anyways, the latest crypto-wallet apps to be cloned was Trezor. So, what happens when you use one of these apps to manage your portfolio? Money goes in and, poof, it melts into nothingness. User beware!
Pyramid schemes (Ponzi)
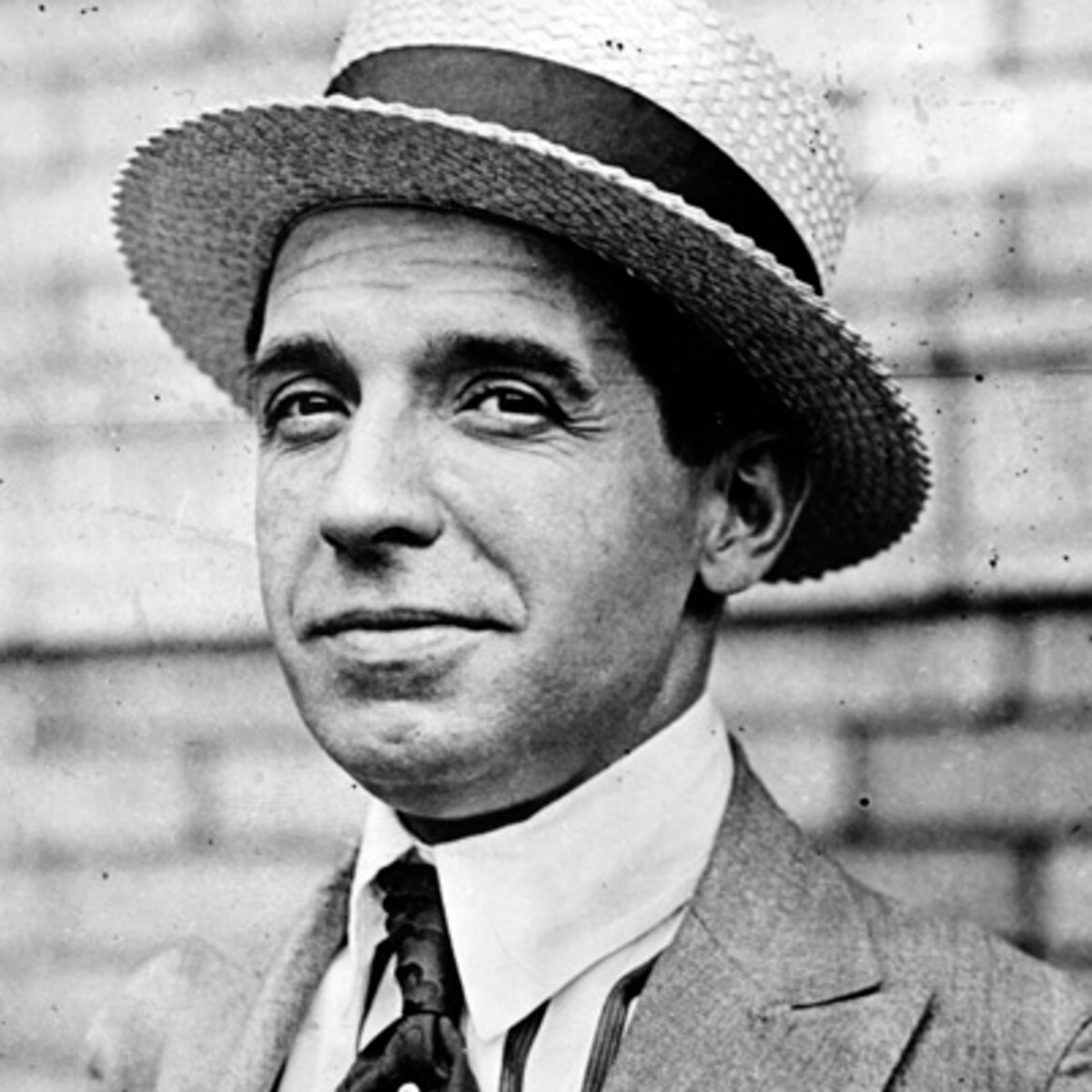
Handsome son of a gun, isn’t he? Meet Charles Ponzi or the reason why the dictionary people added a new entry under the word “pyramid”. Yup, he’s the mastermind behind the eponymous lurk. Never heard of it? That’s all right; it just means you haven’t had any dealings with hedge funds and private equity.
Pulling this off is does not require a Ph.D. in rocket science; just the right amount of guile. The idea is to coax as many people as possible to invest in, well, something.
Ponzi managed to pull this off with postage stamps, so why wouldn’t it work with cryptocurrency? The pyramid scheme in a nutshell: the scammer comes up with a ‘foolproof’ investment scheme. Enters the goose, just ready to be plucked. The swindler will persuade the goose to tie his money into this outstanding venture, promising higher gains.
The goose will then invest a sum amount in the idea. But that’s not all – the initial investors now have the job to bring in new investors if they want to get a share of that dough or, in this case, digital coins.
Once the new investors step in, the older ones begin getting payouts. And it goes merely on until the new investors well run dry. In the end, the only one who stands to win is the scammer.
Classic phishing
When all else fails, you will always have the ‘classics’ to fall back to. A while back, I wrote an article about just how effective PayPal phishing scams are, even though everyone knows about them and how they work (ironic, isn’t it?).
Pretty easy to imagine how this type of scam works – using psychological manipulation, the scammer will trick you into revealing your username, password, or billing information.
This is a classic example of identity theft, where the scammer wrongfully acquires and uses your personal information for fraudulent purposes. The most commonly used tactics are Punycode and the so-called fake Airdrops. So, how does this work?
Simply put, the scammer sends the user a link that sends him to a fake page. Naturally, this page looks exactly like a legit crypto-trading service. On top of that, the pot is sweetened by a free Airdrop. In most cases, the users are asked to send a certain number of Bitcoins or Ether to a spiked MyEtherWallet.
Impersonation
Considered to be the most devastating weapon in a scammer’s arsenal, impersonation scams are very hard to detect and, therefore, to counter. This is what in cybersecurity lingo is called a multi-vector attack.
First, the impersonator must gather as much information as he can about the victim. Up next, there’s the company on behalf of which he will attempt to contact the victim. Of course, this also involves calling up some vital info.
For instance, in some cases, the scammers posed as the project owner or even the company’s CEO in order to lure the victim with a once-in-a-lifetime offer.
Here’s where the multi-vector attack comes into play – using a combination of social engineering, phishing, and cold-calling, the scammer will coax the victim into investing his crypto coins into his idea.
As I said, impersonation scams are very hard to detect simply because the scammers know how to do their homework. The only possible defense once can think of might be having some inside info on the company.
Unregulated brokers.
Careful who you trust with your cryptocurrency portfolio. There are dozens of unregulated online brokers and exchanges and, like in most scamming schemes, they lure customers with low prices, competitive trading products, and quick returns.
After you make the deposit, it will become increasingly hard to withdraw your money. For instance, they would ask for high commissions or conjure up bogus reasons why you can’t withdraw your funds or gain. Worst case scenario – they stop returning your calls and run away with your money.
Automated trading systems
Given the volatility of crypto coins like Bitcoin, promoters would look by just about any opportunity to make a profit. The general tendency would be to speculate the price differences between various exchanges.
Why is this considered a scam? In most cases, these cryptocurrency exchanges have ludicrously long withdrawal process, not to mention the fact that they tend to charge a lot in order to swap Bitcoins or Ether with fiat currencies (government-issued currency that can’t be backed up by a physical commodity with value, like silver or gold).
Basically, it’s the textbook definition of money). Long story short – crypto coin arbitrage takes a lot, doesn’t guarantee gains, and will more than likely lead to financial loss. I should also add that these types of trades take a long time to settle, which means that anything can happen in the interim. Caveat emptor!
Pump & Dump online groups
P&D scams are not exactly new. In fact, economic analysts argued that this type of fraud goes all the way back to the early 18th century.
Though most of these schemes were conducted by word of mouth, emergent techs such as the Internet, social media, and email servicing made it possible for scammers to attract even more investors.
So, what’s up with this P&D scams? In laymen’s terms, it’s a plot aimed at inflating the stock price of certain commodities in a bid to buy low and sell high. What happens is when the scammers dump their ill-gotten shares, the prices will plummet, leading to investors losing their money fast. The same thing happens with cryptocurrency.
Bear in mind that it takes quite a lot of people in order to pull this off. The scammers usually congregate over social media platforms such as Facebook Messenger, Telegram, Slack, and IRC. On average, such a group would total some 100,000 members.
Each is a vital cog in the effort to manipulate the price of altcoins with low market caps. These groups use various tools to monitor volumes, a vital first step identifying crypto coins with the highest ‘scheming’ potential. After that, it’s all a matter of buying low while watching the prices go down.
Social media engineering
Social media platforms are a great way to get to know investors and people who are willing to trade cryptocurrency. However, at the same time, these platforms are breeding ground for fake cryptocurrency traders, scammers impersonating legit traders, and bots.
Remember the golden rule – if it sounds too good to be true then it’s most definitely a scam. It would also be in your best interest to stick to legit communication channels and avoid private messages received on Facebook, Twitter, or Instagram.
Fake emails
Fake emails are, by far, the most ‘popular’ way of luring potential investors. What’s even more unnerving is the fact that they really look like legit emails piped through by legit company – logos, headers, names, addresses, social media handles.
Don’t fall for it; if you ever receive such an email, check every bit of information before acting. For instance, if the email contains phone numbers or physical addresses, you should consider calling the trader.
Try to gauge the offer’s genuineness: are the numbers doable? How about initial coin offerings? Does the trader operate over a regulated cryptocurrency exchange? Has he informed you about liabilities? And, most importantly, see how confident he is about the plan itself. The scammer will always try to boast the plan.
Cryptocurrency fraud – Case Studies
Now that you got the hang of what to look out for, here are some cryptocurrency fraud cases. Enjoy, but watch your back.
The BITPoint Hacking: Stolen Bitcoin
On the 12th of July, BITPoint, a Japanese cryptocurrency exchange, reported that over $28 million were stolen in a massive hack attack. It was later revealed that the losses amounted to $19.3 million, but that didn’t make things any better.
The official report revealed that the funds were stolen mostly belonged to the company. The looted assets included Bitcoin, Litecoin, Bitcoin Cash, XRP, and Ether. This incident resulted in significant lost funds for both the company and its customers.
Since the company’s cybersecurity safeguards were inefficient, BITPoint decided to postpone withdrawals and deposits for the time being. In addition, Asahi Shimbun, BITPoint’s CEO, has announced that the company will return the assets to the customers affected by the attack.
Binance May Heist
In late May, Binance, one of the largest cryptocurrency exchanges, suffered a $40 million loss in the wake of a “perfectly-orchestrated” hacking attack. The authorities pointed out that among the assets stolen by hackers were 2FA codes and API Tokens.
A total of 7,000 Bitcoins were stolen, marking a significant case of stolen bitcoin. Several high net-worth accounts were compromised. That did not put the company out of business, of course, since the stolen assets were roughly two percent of all of Binance’s holdings. The exchange announced that it will be using part of its self-insurance funds in order to cover for the losses.
Typosquatting Scam
What happens when six hackers get together? They steal $27 million worth of Bitcoins. According to a Europol press release, in late June, five men and one woman were detained following a 14-month-long investigation which involved law enforcement agencies from the United Kingdom and the Netherlands.
The report revealed that the six suspects were part of a criminal ring responsible for the theft of $27 million from 4,000 people. The method used was typosquatting, which involves the use of clandestine cryptocurrency exchanges in a bid to tap into the victim’s cryptocurrency wallet.
Fall of the Kraken.
Earlier this year, Kraken, one of Bitnance’s competitors, was hit by a cryptocurrency price drop last year. This flash-crash resulted in the coin’s price plummeting from $8,400 to a mere $75. At the time, the company believed that the sudden crash might have been caused by a glitch in the system.
However, that didn’t account for a high-profile’s wallet being hacked and emptied. The subsequent investigation revealed that glitch and hacking were related. Furthermore, the suspect managed to obscure 1,200 bitcoins or the equivalent of $10 million before being apprehended by law enforcement authorities.
GateHub XRP Heist
On June the 6th, a group of cybercriminals managed to steal $10 million worth of XRP coin from cryptocurrency exchange GateHub. The authorities revealed that the amount was stolen from 100 compromised Ledger wallets.
Although the account holders were contacted and reimbursed, the investigators have yet to produce any suspects. In addition, out of the $10 million that was stolen from GateHub, only $200,000 were retrieved.
Bitrue Hack Attack
During the same month, another cryptocurrency exchange has been hit by a hacking attack – Bitrue, a Singaporean crypto company, lost over $4 million.
According to the authorities, sometime in June, the unauthorized access occurred. At around the same time, Bitrue’s platform reported that 9.3 million XRP and 2.5 million ADA were transferred to an unknown wallet.
The subsequent investigation revealed that the cybernetic attack was possible due to a system vulnerability that surfaced after the company’s Risk Control Team performed a 2nd review process. Although the assets are irretrievable, the company has reimbursed all the affected parties.
Tips to avoid cryptocurrency fraud and ensure Cryptocurrency Recovery
Quite a lot to take in, isn’t it? What can I say? The world’s a wonderful place; the question is now how can one protect himself against these threats. To this end, I would advise you to consider partnering with a reputable cyber security company. Such companies play a critical role in boosting online security, recovering lost cryptocurrency, and navigating the complexities of online fraud. Check out these awesome tips.
Research, research, and even more research
The best way to avoid cryptocurrency fraud is to do your homework before investing your crypto coins. There’s plenty to choose from – in fact, there are over 500 online exchanges.
So, in order to avoid being scammed, take your time to research the exchanges: read their blogs, look at the conversion rates, gains, ICOs, over-the-web security protocols. For extra safety, you could shoot an email to support or a company’s representative to ask about the exchange.
Figure out a way to store your cryptocurrency
Buying and trading crypto coin is only the first step. Next along the line would be figuring out a way to store your digital assets. In the digital realm, securing these assets poses significant challenges due to the complexities and anonymity of digital currencies. So far, there are two ways to store cryptocurrency: working through exchanges and digital wallets.
Exchanges work very much like traditional banks: they offer deposits, accounts, and, of course, charge fees for deposit management and transactions.
As for the second storage method, digital wallets are to cryptocurrency what Revolut and Payoneer are to fiat currencies. Evidently, the decision’s entirely up to you.
Know the tell-tale signs of fraudulent ICOs
As you might have figured out by now, fake ICOs are a scammer’s weapons of choice. Of course, none of this would be possible without someone naïve enough to believe this stuff.
Anyway, in the case of ICOs, you can easily figure out if the project’s legit or fake by taking a closer look at the white paper for signs of forgery. These include:
Less-than-original whitepapers
Fraudsters are more likely to copy an entire whitepaper and pass it as their own rather than writing the whole thing from scratch. Just copy-paste the whole things into Google and the search button. If you see the same thing elsewhere, it’s more than likely that you’re dealing with scammers.
No team members
Most exchange presentation websites feature a media section that contains info about the members of the team. Look for any inconsistencies: incomplete descriptions, stock photos, odd-looking contact details.
Incomplete pages
The websites would look like they were made in a hurry. You know what I’m talking about.
Text inconsistencies
Since these websites were made for one purpose and one purpose only, it’s obvious that the person or persons behind the scheme won’t spend time worrying about details such as blog posts, landing pages, or newsletters. Take some time to read a post or two. Lack of proofreading alone should be a major red flag, one that may point out that the website is, indeed, fake.
Staff reluctant to answer tough questions
Even the most experienced scammer cannot dupe a crypto-savvy user. So, if you decide to get in touch with a member of staff, start asking questions. The more technical they are, the better. A legit employee will be in the position to answer every question related to the product, whereas a scammer might eschew them.
Boost your online security with a Cyber Security Company
While it’s always a good idea to beef up your online security, now more than ever you should take the time to review your cybersecurity habits. I know it’s convenient to trade or buy crypto on the fly, but sloppy practices usually result in compromised personal data.
To this end, I would advise you to conduct every transaction from a secured endpoint. Our Heimdal™ Threat Prevention Home product can safeguard your computer and cryptocurrency account against all types of online attacks such as malware, ransomware, cryptojacking, and even bitcoin miners. Additionally, in the unfortunate event of compromised digital assets, understanding cryptocurrency recovery can be crucial. Specialists in cryptocurrency recovery can help navigate the complexities of reclaiming lost or stolen funds, providing both technical expertise and emotional support.
On that note, you should definitely consider running a quick scan of your system in order to root out lingering bitcoin miners.
The easy way to protect yourself against malware
Here’s 1 month of Heimdal™ Threat Prevention Home, on the house!
Use it to: Block malicious websites and servers from infecting your PC Auto-update your software and close security gaps Keep your financial and other confidential details safe

Know thine enemy: Collaborate with Law Enforcement Authorities
Each day, the list of shady cryptocurrency exchanges gets bigger. So, before you choose an exchange, make sure it’s not on the blacklist. Here are the platforms’ names you should look out for:
- Ydconsultant
- Patrimoirecrypto,
- Nettocrypto
- Mycrypto24
- Good-Crypto.
- Gmtcrypto
- Gme-crypto.
- Finance-mag.
- Eurocryptopro
- Ether-inbest.
- Cryptos-currency.
- Cryptos.solutions.
- Crypto-infos.
- Crypto-banque.
- Cryptavenir.
- Coinquick.
- Capital-coins.
- Btc-cap.
- 01crypto.
Wrap-up
Remember that a fool is born every minute. Don’t be one – read, research, get your act straight and always pay attention to your cybersecurity habits. Hope you’ve enjoyed my article. As always, for questions, rants, comments, coffee and beer donations, shoot me an email.










 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security







