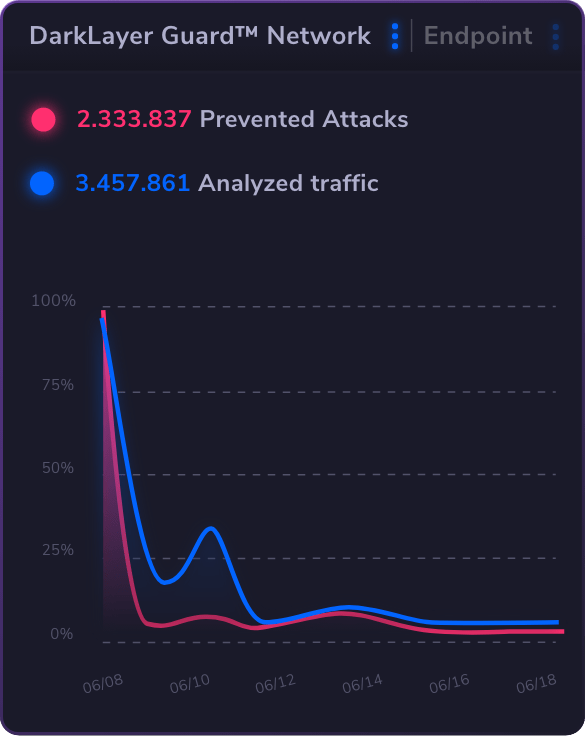
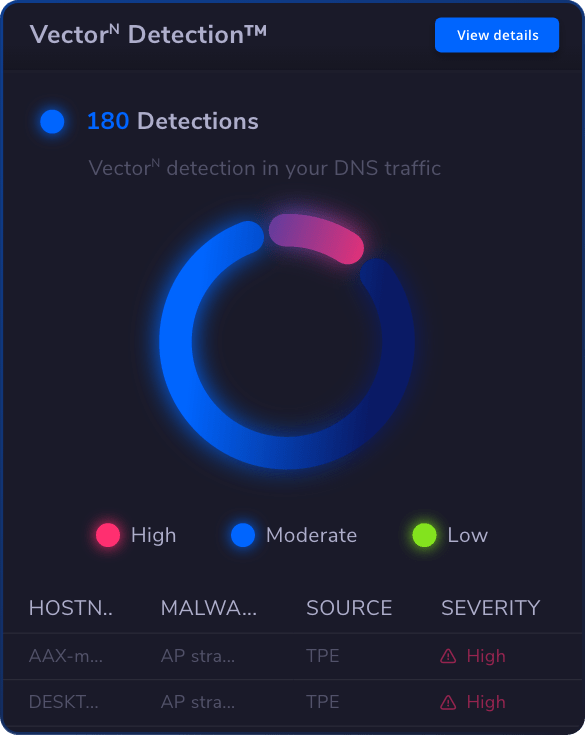
Heimdal’s DNS Security is the world’s first cybersecurity product supporting true DNS over HTTPS filtering, encrypting domain traffic through secure sessions. This feature mitigates Man-in-the-Middle attacks and DNS spoofing while maintaining system performance and user privacy.
Advanced features include customizable block pages with organizational branding, category-based blocking with scheduling, comprehensive investigate functionality, and VPN compatibility. The system provides detailed logging, supports IPv4 and IPv6 protocols, and integrates with existing infrastructure. Unlike traditional filtering that blocks known threats, Heimdal combines real-time intelligence, predictive analytics, and process correlation for comprehensive protection.














 Network Security
Network Security
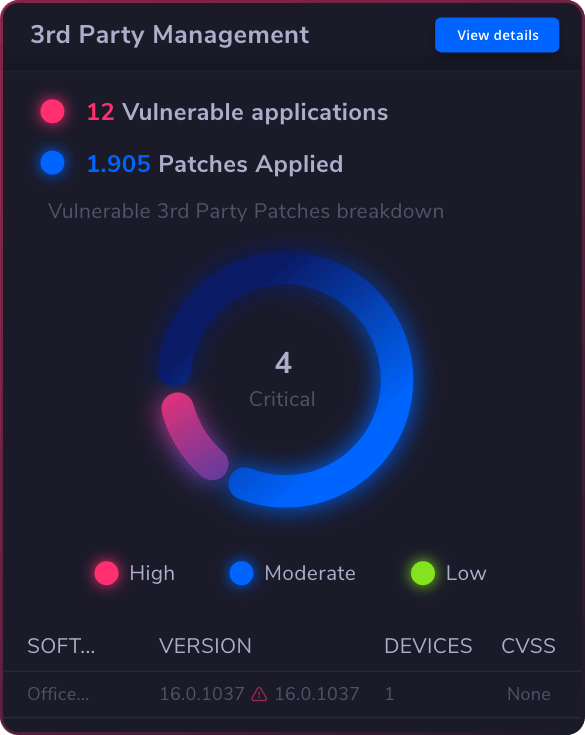
 Vulnerability Management
Vulnerability Management
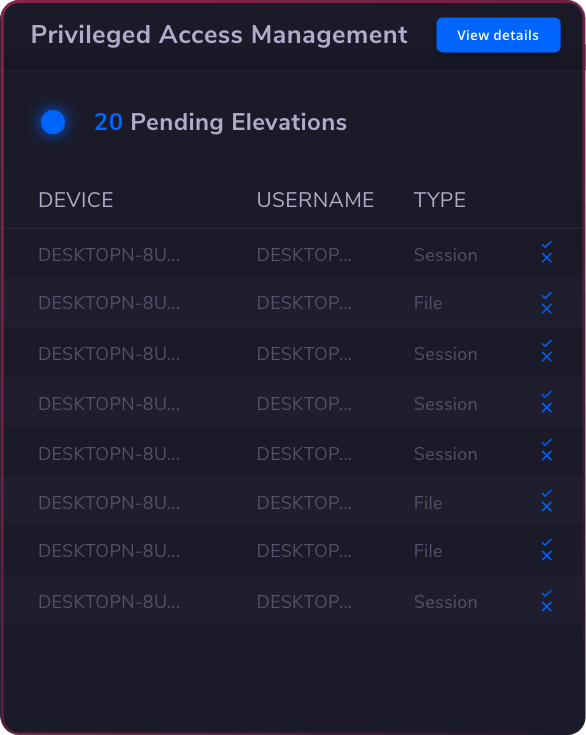
 Privileged Access Management
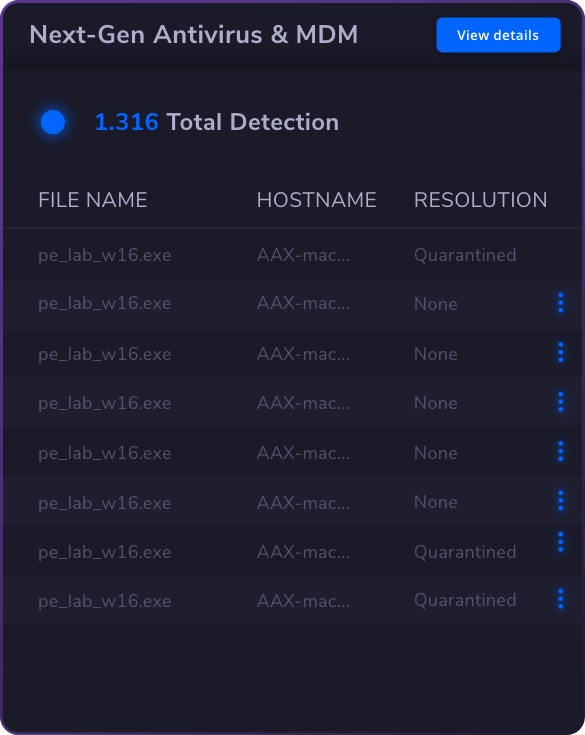
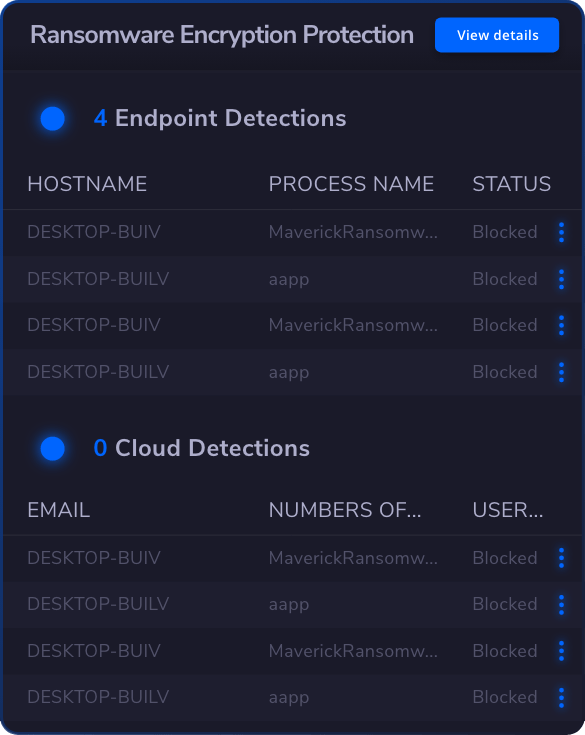
Privileged Access Management  Endpoint Security
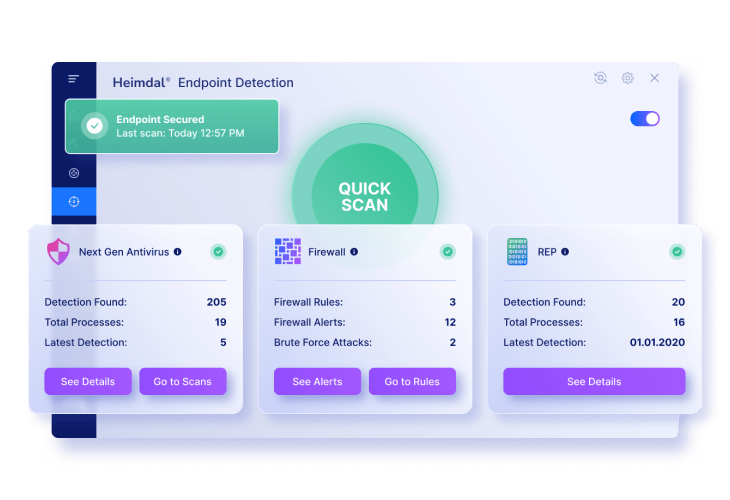
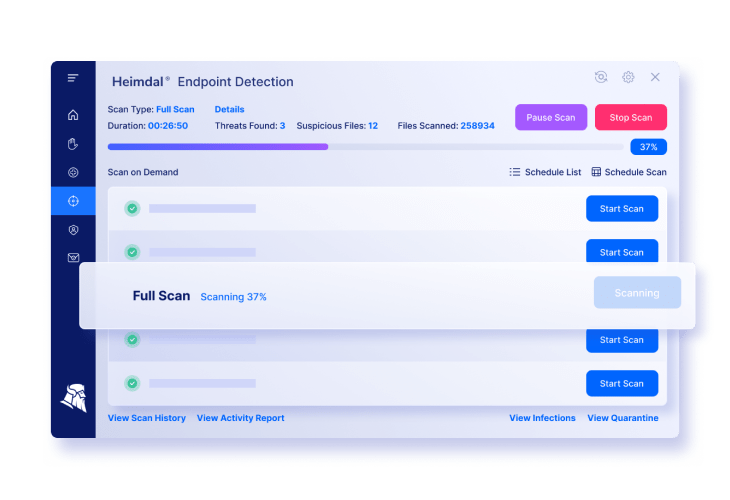
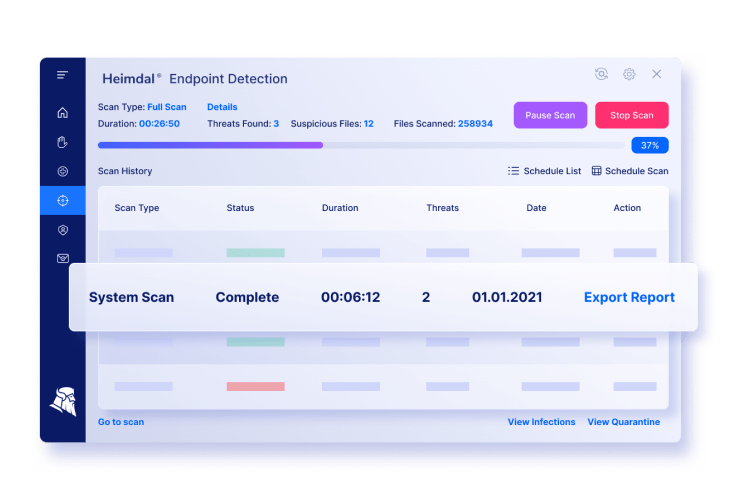
Endpoint Security
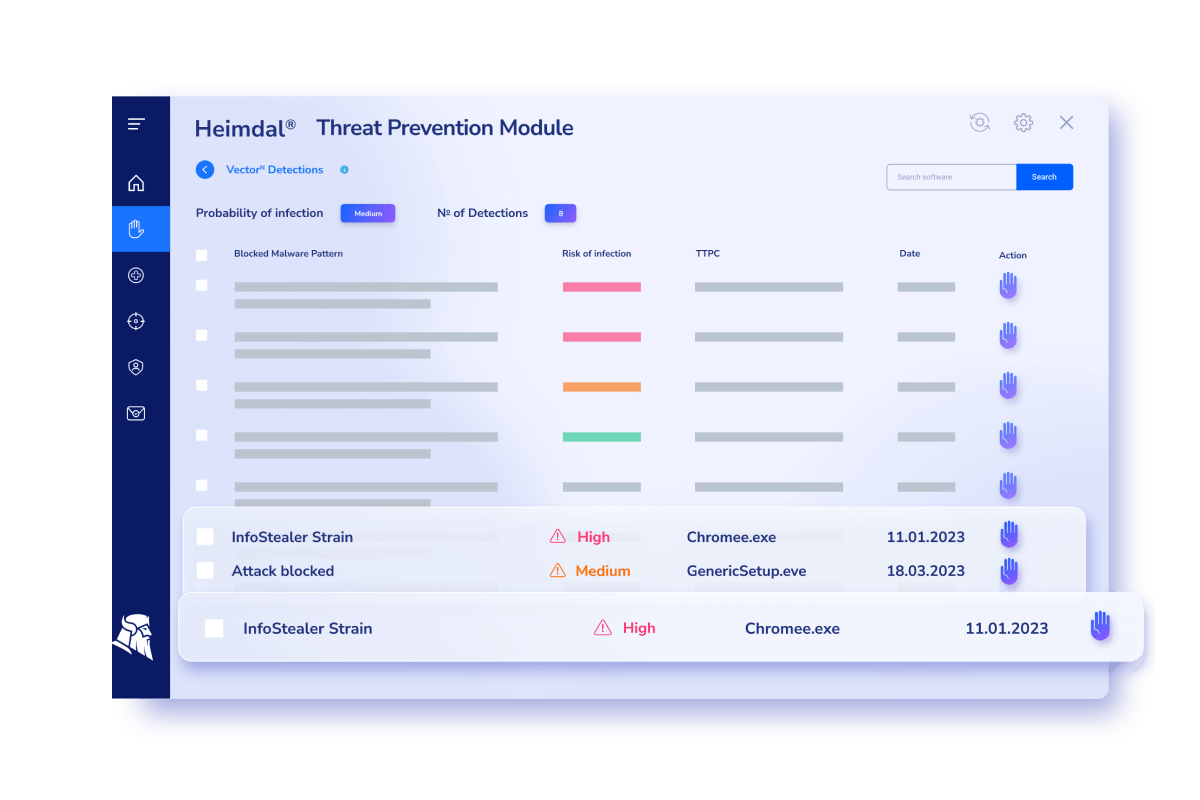
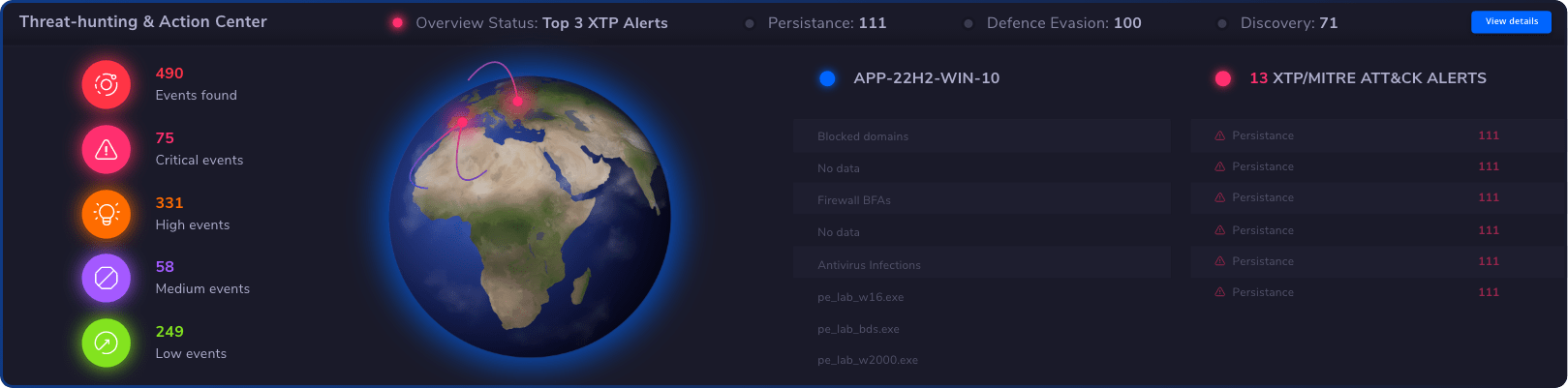
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
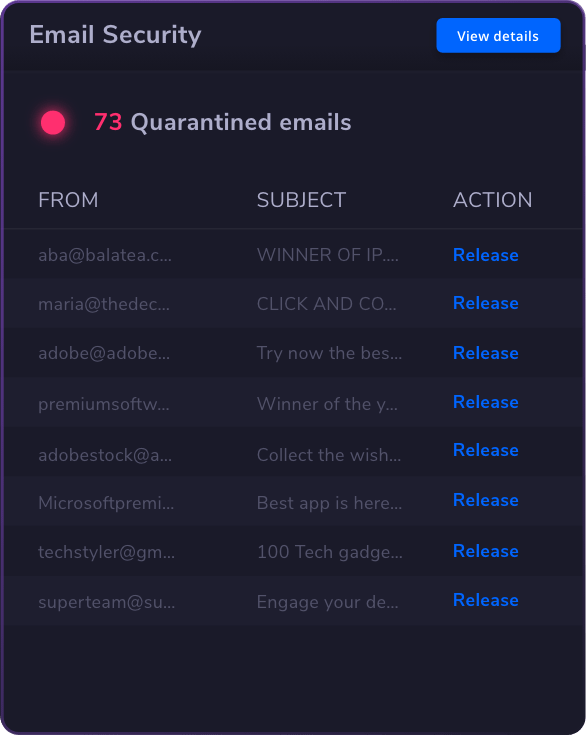
 Email & Collaboration Security
Email & Collaboration Security