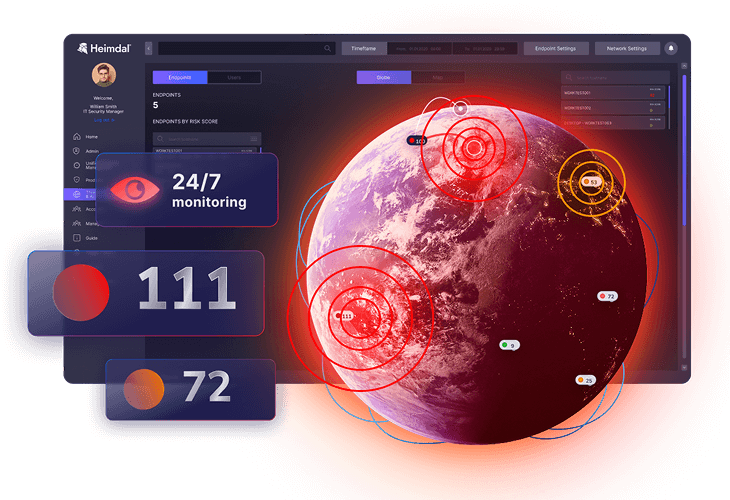
Heimdal ITDR (Identity Threat Detection and Response) gives you continuous visibility and control over identities across your organisation, limiting identity-based threats.
It monitors how users log in, what they access and how privileges are used on endpoints and in cloud services like Microsoft 365.
When behaviour looks risky, Heimdal ITDR helps you investigate, block and clean up the threat from the same console, maintaining your security posture, which is a crucial cybersecurity approach for organizations in this day and age.













 Network Security
Network Security
 Vulnerability Management
Vulnerability Management
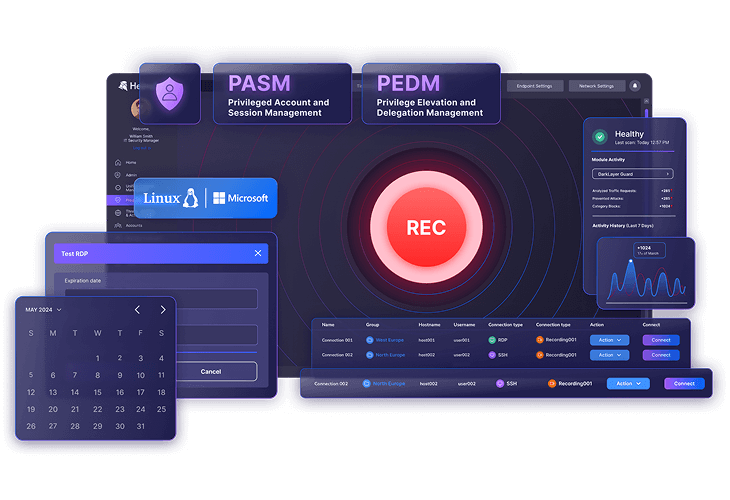
 Privileged Access Management
Privileged Access Management  Endpoint Security
Endpoint Security
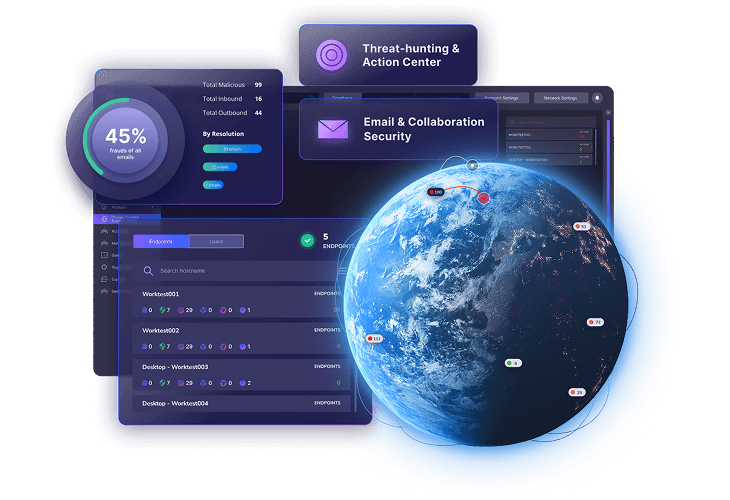
 Threat Hunting
Threat Hunting
 Unified Endpoint Management
Unified Endpoint Management
 Email & Collaboration Security
Email & Collaboration Security